A digital identification tool provided
by OCR Labs to major banks and government agencies leaked sensitive
credentials, putting clients at severe risk.
- London-based OCR Labs is a major provider of digital ID
verification tools. Its services are used by companies and
financial institutions including BMW, Vodafone, the Australian
government, Westpac, ANZ, HSBC, and Virgin Money.
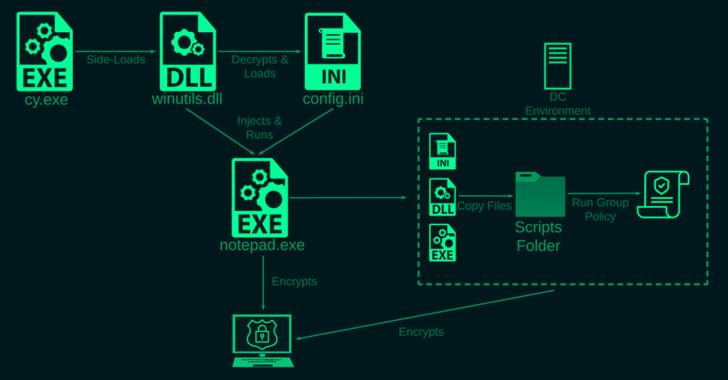
- A misconfiguration of the companys systems exposed sensitive
credentials to the public.
- Data leak affected QBANK, Defence Bank, Bloom Money, Admiral
Money, MA Money, and Reed.
- Using leaked data, threat actors could potentially breach banks
backend infrastructure and consequently the infrastructure of their
clients.
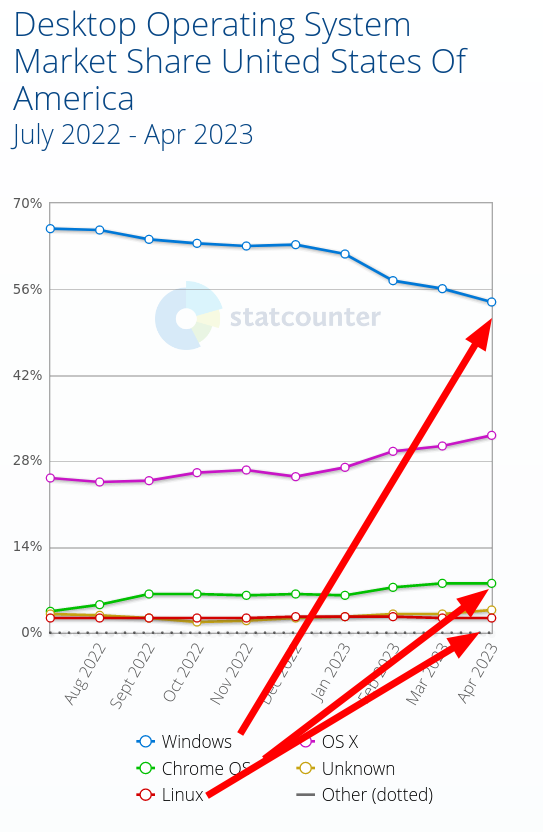
- Financial services are the main target for cybercriminals, so
the threat for the organizations and their customers is
severe.
- Cybernews contacted OCR Labs, and the company fixed the
issue.
The Cybernews research team discovered a misconfiguration in the
OCR Labs system that exposed sensitive data.
The company is a leading provider of digital ID verification
tools, with its IDkit tool being used by major banks, telecoms
companies, and governmental agencies. IDKit verifies users by
linking their faces to their identity documents.
The discovered data leak impacted financial institutions in
Australia QBANK, mainly used by government agency workers, Defence
Bank, catering to the Australian armed forces, and MA Money, a
company that focuses on residential mortgages.
The leak also affected Bloom Money and Admiral Money two
financial companies based in the UK, and Reed, which is the UKs top
recruitment agency.
Using leaked data, threat actors could potentially breach
companies backend infrastructure and consequently the
infrastructure of their clients. While financial services are the
main target for cybercriminals, the threat to the organizations and
their customers is severe.
Cybernews reached out to the company, and it fixed the
issue.
A treasure trove of credentials
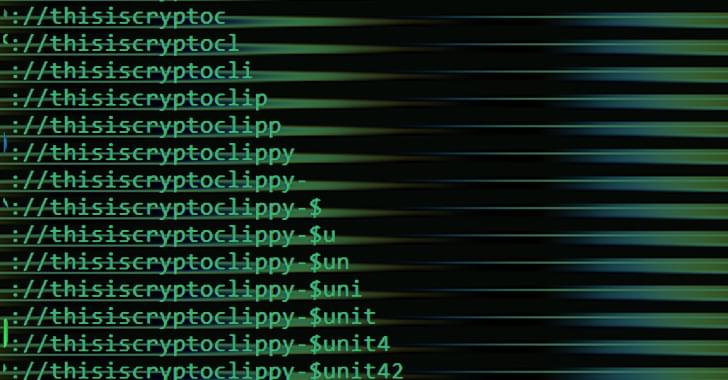
On March 8, 2023, the Cybernews research team discovered a
publicly accessible environment file (.env) belonging to idkit.com,
owned by OCR Labs.
The file contained database credentials, including host, port,
and username, Amazon
Web Services (AWS) with Simple Queue Service (SQS) access
credentials, application tokens, and various application
programming interface (API) keys.
Among the leaked data, researchers found Google and Liveness API
keys. Liveness is used in the digital identification process,
determining whether the sample belongs to a live person or a fake,
thereby preventing ...









 If
players can change their games as they see fit, theres a real
danger theyll choose different options than what the left
wants.
If
players can change their games as they see fit, theres a real
danger theyll choose different options than what the left
wants.



 Optimize your site for search engines
Optimize your site for search engines The
New Right celebrates health strong men and beautiful women as part
of a broader vitalist movement that has taken hold of young men and
women across the West.
The
New Right celebrates health strong men and beautiful women as part
of a broader vitalist movement that has taken hold of young men and
women across the West..jpg?itok=0KujRkzo)


 Cultural
Marxism is dystopia peddling utopia through grievance narratives
and rank emotionalism, the hallmarks of transgenderism.
Cultural
Marxism is dystopia peddling utopia through grievance narratives
and rank emotionalism, the hallmarks of transgenderism. Mitch
McConnell has been silent as the lead contender for the Republican
presidential nomination is politically persecuted.
Mitch
McConnell has been silent as the lead contender for the Republican
presidential nomination is politically persecuted.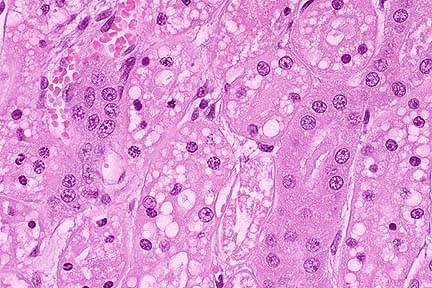
 Instead
of speaking out in support of Christians, the people who run the
country offered solidarity to transgender Americans like the
shooter.
Instead
of speaking out in support of Christians, the people who run the
country offered solidarity to transgender Americans like the
shooter.



 Gonzales
is actively working to sink the entire Republican congressional
strategy to ensure the border remains open.
Gonzales
is actively working to sink the entire Republican congressional
strategy to ensure the border remains open.





 READ MORE AT THE EXPOSE IT WAS ALL A LIE: How
your Government tricked you...
READ MORE AT THE EXPOSE IT WAS ALL A LIE: How
your Government tricked you...