| IndyWatch Science and Technology News Feed Archiver | |
 |
Go Back:30 Days | 7 Days | 2 Days | 1 Day |
|
IndyWatch Science and Technology News Feed was generated at World News IndyWatch. |
|
Sunday, 26 March
04:00
Gordon Moore, 1929 2023 Hackaday

The news emerged yesterday that Gordon Moore, semiconductor pioneer, one of the founders of both Fairchild Semiconductor and Intel, and the originator of the famous Moores Law, has died. His continuing influence over all aspects of the technology which makes our hardware world can not be underestimated, and his legacy will remain with us for many decades to come.
A member of the so-called Traitorous Eight who left Shockley Semiconductor in 1957 to form Fairchild Semiconductor, he and his cohort laid the seeds for what became Silicon Valley and the numerous companies, technologies, and products which have flowed from that. His name is probably most familiar to us through Moores Law, the rate of semiconductor development he first postulated in 1965 and revisited a decade later, that establishes a doubling of integrated circuit component density every two years. Its a law that has seemed near its end multiple...
03:34
Theo de Raadt at CanSecWest: Synthetic Memory Protections OpenBSD Journal
We recently reported
that Theo de Raadt (derradt@) was scheduled to present
at CanSecWest. That's now
happened, and slides of Theo's
presentation, Synthetic Memory Protections, can be found in
the usual place.
Video is available on
the bird site.
02:44
Pwn2Own Vancouver 2023 awarded $1,035,000 and a Tesla for 27 0-days Security Affairs
On the third day of the Pwn2Own Vancouver 2023 hacking contest, the organization awarded $185,000 for 10 zero-day exploits.
Pwn2Own Vancouver 2023 is ended, contestants disclosed 27 unique zero-days and the organization awarded a total of $1,035,000 and a Tesla Model 3. The team Synacktiv (@Synacktiv) (Benoist-Vanderbeken, David Berard, Vincent Dehors, Tanguy Dubroca, Thomas Bouzerar, and Thomas Imbert) won the competition, they earned 53 points, $530,000, and a Tesla Model 3.
On the third day, contestants were awarded $185,000 after demonstrating 5 zero-day exploits targeting the Ubuntu Desktop, Windows 11, and the VMware Workstation software.
The day began with the hack of Ubuntu Desktop by Kyle Zeng from ASU SEFCOM, he used a double-free bug and earned $30,000 and 3 Master of Pwn points.
Thomas Imbert (@masthoon) from Synacktiv (@Synacktiv) used a UAF against Microsoft Windows 11. They earn $30,000 and 3 Master of Pwn points.
The researchers Mingi Cho of Theori used a UAF against Ubuntu Desktop, the team earned $30,000 and 3 Master of Pwn points.
The STAR Labs (@starlabs_sg) team used an uninitialized variable and UAF to hack the VMWare Workstation virtualization software. They earned $80,000 and 8 Master of Pwn points. The STAR Labs team also attempted to demonstrate an exploit against Microsoft Teams, but failed to do it within the time allotted.
Bien Pham (@bienpnn) from Qrious Security successfully targeted Ubuntu Desktop, but used a known exploit, for this reason, the attempt was classified as &#...
02:23
Flying taxi service coming to Chicago using eVTOL aircraft Lifeboat News: The Blog
In the latest sign of growing interest in the flying taxi sector, United Airlines and air mobility startup Archer Aviation have announced an upcoming service for hops between downtown Chicago and OHare International Airport.
The service will offer a sustainable, low-noise, and cost-competitive alternative to ground transportation for folks traveling to and from the airport, United and Archer said in a release.
02:23
The Personalized Stem Cells That Could One Day Treat Parkinsons and Heart Failure Lifeboat News: The Blog
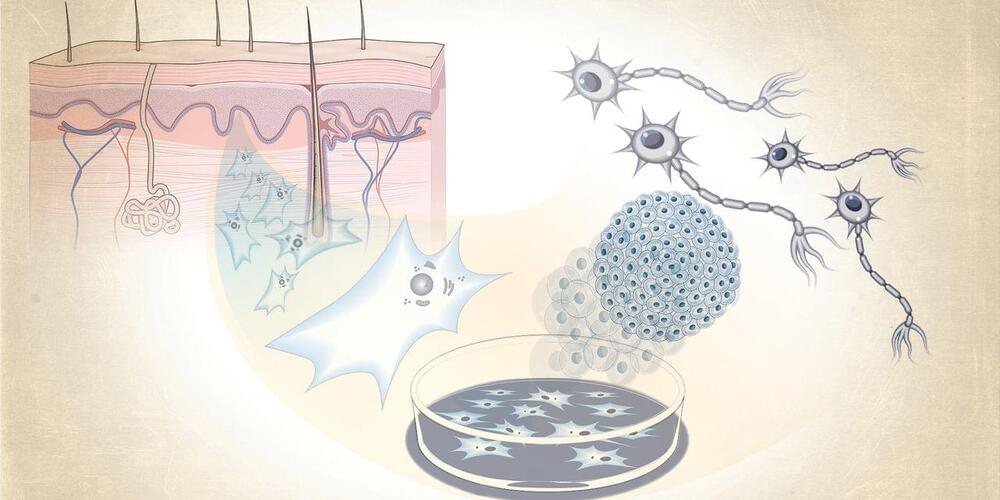
Could an injection of lab-cultured brain cells, created from a persons own cells, reverse symptoms of Parkinsons disease? Thats an idea that Aspen Neuroscience Inc., a startup based in San Diego, plans to test in human trials later this year.
In patients with Parkinsons, neurons die and lose the ability to make the chemical dopamine, leading to erratic, uncontrollable movements. Aspen Neuroscience will test if the newly injected cells can mature into dopamine producers, stopping the debilitating symptoms of this incurable disease, says Damien McDevitt, the companys chief executive officer. Tests in animals have shown promise, the company says.
02:22
People And Machines Will Merge Sooner Or Later Lifeboat News: The Blog
The idea of the technological singularity was inspired by how ubiquitous and invasive AI is becoming. As they combine thought and machine, recent advanceme
01:20
Moderna CEO Brazenly Defends 400% COVID Shot Price Hike, Downplays NIH's Role SoylentNews
In congressional testimony Wednesday, Moderna CEO Stphane Bancel unabashedly defended the company's plans to raise the US list price of its COVID-19 vaccines by more than 400 percentdespite creating the vaccine in partnership with the National Institutes of Health, receiving $1.7 billion in federal grant money for clinical development, and making roughly $36 billion from worldwide sales.
Bancel appeared this morning before the Senate's Health, Education, Labor, and Pensions committee, chaired by Sen. Bernie Sanders (I-Vt.), who has long railed at the pharmaceutical price gouging in the US and pushed for policy reforms. After thanking Bancel for agreeing to testify, Sanders didn't pull any punches. He accused Moderna of "profiteering" and sharing in the "unprecedented level of corporate greed" seen in the pharmaceutical industry generally.
[...]
Early doses were priced between $15 to $16, while the government paid a little over $26 for the updated booster shots. When federal supplies run out later this year and the vaccines move to the commercial market, Moderna will set the list price of its vaccine at $130."This vaccine would not exist without NIH's partnership and expertise, and the substantial investment of the taxpayers of this country," Sanders summarized. "And here is the thank you that the taxpayers of this country received from Moderna for that huge investment: They are thanking the taxpayers of the United States by proposing to quadruple the price of the COVID vaccine."
Read more of this story at SoylentNews.
01:00
A LEGO Camera You Just Might Own Yourself Hackaday

A camera makes for an interesting build for anyone, because its an extremely accessible technology that can be made from materials as simple as cardboard. More robust cameras often require significant work, but what if you could make a usable camera from LEGO? Its a project taken on by [Zung92], who hasnt simply made a working 35 mm camera from everyones favorite construction toy hes also managed to make it exude retro style. Best of all, you can vote for it on the LEGO Ideas website, and you might even get the chance to have one for yourself.
Frustratingly theres little in the way of in-depth technical detail on the Ideas website, but he does mention that it was a challenge to make it light proof. Even the lens is a LEGO part, and if diffraction-based photography isnt for you theres also a pinhole option. We look forward to seeing this camera progress, and we hope well see it advance to becoming a LEGO Ideas kit.
This is an extremely polished design, but surprisingly, its not our first LEGO camera.
Thanks [Michael] for the tip.
00:43
Internet Archive is Liable for Copyright Infringement, Court Rules TorrentFreak
 In 2020, publishers Hachette, HarperCollins, John Wiley
and Penguin Random House
sued the Internet Archive (IA) for copyright infringement,
equating its Open Library to a pirate site.
In 2020, publishers Hachette, HarperCollins, John Wiley
and Penguin Random House
sued the Internet Archive (IA) for copyright infringement,
equating its Open Library to a pirate site.
IAs library is operated by a non-profit organization that scans physical books and then lends the digital copies to patrons in an ebook format.
While digital book lending is not uncommon, libraries typically loan out DRM-protected files after acquiring a license from publishers. In this case, IA sent physical books it owned to a scanning facility and made its own copies.
Fair Use or Mass Copyright Infringement?
These digital copies were subsequently loaned out to patrons, with IA ensuring that only one person at a time could access a single digital copy of a single physical book.
IA previously sought summary judgment in its favor, arguing that a digital copy of a physical book transforms the original work, with lending limits and the absence of profit also supporting a finding of fair use.
In contrast, the publishers described IAs library as a rogue operation engaging in willful mass copyright infringement. Claiming direct damage to their bottom line, the publishers lawsuit aimed to put an end to the illegal lending program once and for all.
The publishers went on to request summary judgment and a declaration that this type of copying is a clear case of copyright infringement.
Opinion and Order
Earlier this week, the parties had the opportunity to back up their arguments during a New York Court hearing. District Court Judge John Koeltl questioned both sides on their summary judgment requests, before deliberating on his final decision.
After weighing the arguments. Judge Koeltl published his opinion and order yesterday. His order clearly sides with the publishers, whose request for summary judgment was granted. IAs fair use defense and summary judgment in its favor was denied.
Saturday, 25 March
23:50
Lenovo Flex 5G / Qualcomm SC8180x Support Being Worked On For Mainline Linux Phoronix
In addition to the mainline Linux kernel seeing recent support for the Arm-powered Lenovo ThinkPad X13s and Lenovo Yoga C630, among others, another Lenovo model working toward mainline kernel support is the Lenovo Flex 5G...
22:22
Quantum Computers Vs Supercomputers Lifeboat News: The Blog
Supercomputers and quantum computers are potent tools for handling difficult calculations, problem-solving, and data analysis. Although they both have the potential to transform computing technology, their speeds and capacities differ greatly.
Supercomputers quickly process massive volumes of data to provide a single result using a conventional computing strategy with numerous processors. These computers are the most powerful in terms of raw computing speed, but they can only do one task at a time, and Moores Law places a cap on how much data they can process (the principle that computer processor speeds double every two years).
Quantum computers, on the other hand, utilize laws of quantum mechanics to process information in ways that regular computers cannot, resulting in vastly higher processing speeds. They can manage several activities at once and take on challenging issues that would take supercomputer months to resolve. Yet, because of their great sensitivity to temperature fluctuations and need for isolation from outside influences, quantum computers require more upkeep than their conventional equivalents.
22:17
Microsoft's CBL-Mariner Linux Distribution Continues Cultivating More Packages Phoronix
Microsoft's in-house Linux distribution that they make public, CBL-Mariner, began with a very niche focus while over time has continued adding additional packages as it is worked into becoming a more robust Linux platform...
22:03
In Memoriam: Gordon Moore, 1929 - 2023 SoylentNews
In Memoriam: Gordon Moore, 1929 - 2023:
With great sadness, the Gordon and Betty Moore Foundation announces the passing of our founder, Gordon Moore.
With his characteristic humility and word economy, Gordon Moore once wrote "my career as an entrepreneur happened quite by accident." A brilliant scientist, business leader and philanthropist, Gordon co-founded and led two pioneering technology enterprises, Fairchild Semiconductor and Intel, and, with his wife, Betty, created one of the largest private grantmaking foundations in the U.S., the Gordon and Betty Moore Foundation.
He may argue that his career as an entrepreneur happened by accident, but his world-changing contributions did not. Never one to trumpet his own accomplishments, Gordon wasn't able to dissuade others from celebrating his wide and long-reaching legacy: the revolutionary technologies and breakthroughs, a long and generous history of philanthropy, and the very culture of experimentation, invention and relentless progress that now defines Silicon Valley.
It took decades for Gordon to be able to speak with a straight face of his eponymous "Moore's Law," the prophetic 1965 observation that became a cornerstone principle of innovation and driving force for the exponential pace of technological progress in the modern world. Gordon later observed that he had looked it up and was pleasantly surprised to find more references on the internet to "Moore's Law" than to "Murphy's Law."
Dubbed a "quiet revolutionary" by his biographers, Gordon always worked in the absence of any pretense or desire for recognition, driven instead by an exceptional curiosity, generosity and unassuming commitment to hard work.
Gordon was always a visionary. Even at the start of his career, he keenly recognized the impact that the technologies he was developing would have on the world. And at an industry event in 1979, he told an Intel audience: "We are bringing about the next great revolution in the history of mankind the transition to the electronic age." (Moore's Law, Thackray, Brock and Jones).
Although Gordon was reluctant to spotlight his own contributions, his biographers have been less reticent about attribution. Gordon is simply, they argue, "the most important thinker and doer in the story of silicon electronics."
Read more of this story at SoylentNews.
22:00
Clever Mechanism Powers This All-Mechanical Filament Respooler Hackaday

No matter how far down the 3D printing rabbit hole we descend, chances are pretty good that most of us wont ever need to move filament from one spool to another. But even so, youve got to respect this purely mechanical filament respooler design, and you may want to build one for yourself just because.
We were tipped off to [Miklos Kiszely]s respooler via the very enthusiastic video below from [Bryan Vines] at the BV3D YouTube channel. He explains the need for transferring filament to another spool as stemming from the switch by some filament manufacturers to cardboard spools for environmental reasons. Sadly, these spools tend to shed fibrous debris that can clog mechanisms; transferring filament to a plastic spool can help mitigate that problem.
The engineering that [Miklos] put into his respooler design is pretty amazing. Bearings excepted, the whole thing is 3D printed. A transmission made of herringbone gears powers both the take-up spool and the filament guide, which moves the incoming filament across the width of the spool for even layers. The mechanism to do this is fascinating, consisting of a sector gear with r...
21:53
MidnightBSD 3.0 Available With Many Software Updates & Fixes Phoronix
MidnightBSD as the desktop-focused OS forked from FreeBSD and relying on the Xfce desktop environment by default is out with its big MidnightBSD 3.0 update...
21:25
AMD Sends Out Patches For Enabling New Graphics IP Blocks (NBIO 7.9, GMC 9.4.3) Phoronix
AMD on Friday sent out new patches for enabling some new graphics IP "blocks" as part of their block-by-block enablement strategy they've been using to introduce new GPU support to their Linux graphics stack by focusing on smaller patch series with versioned parts of the GPU rather than big monolithic patch series with colorful fishy codenames...
21:00
Casinos Not On Gamestop Experiment: Good Or Bad? h+ Media
Casinos Not On Gamestop Experiment: Good Or Bad?
Below are the principle markets that punters can find on an LA Lakers online sportsbook. Now, eSport sites must purchase licenses of operation and in addition go the extra mile to cushion the personal information of their users from the unhealthy guys on the internet. Well, if you have ever placed bets on sports similar to football, tennis, horse racing, and golf, then you have already got a touch about how eSports betting works. In reality, betting on eSports is very a lot much like playing on common sports activities.
The process may be carried out on the net site and within the official app. After that, an e mail might be despatched to your mail confirming the profitable creation of an account. Remember to activate your account by clicking on the hyperlink on this letter.
You may wager at MELbet with confidence, understanding that your money is protected and that the video games are not manipulated. Even first-time bettors will have the ability to join up in a matter of minutes after finishing the form. There are a couple of steps to take, but dont let that overwhelm you. In any event, if there are problems joining up, gamers may contact the customer service team for assistance. Players must deposit no a lot less than 2150 INR, full their profile, and wager the entire deposit amount on an occasion with odds of a minimum of 1.50 to qualify for the free guess.
The company supplies lots of 1xBet promo code 2023 that will impress even demandable purchasers. Comparing with the rivals, 1xBet promo can boast its trustworthiness and alluring bonuses. Unfortunately, this is not attainable this bonus code is reserved for brand spanking new prospects who have not yet opened an account at the website. As the code is hooked up to the 1xbet Welcome Bonus, its offered only to new clients of the site and is obtainable only as quickly as per customer . Bonus code, you presumably can be positive to get one of the best welcome bonus on offer at 1xbet dont miss out on this! To answer the question what is 1xBet and discover more details about this bookmaker, read our evaluate.
This bookmaker has a simple, glossy, and one of the friendliest web site designs out there. When navigating MelBets web site, rest assured of discovering everything that you really want quite fast. MelBets heat yellow and black colors are really easy on the eyes.
The Melbet app in Bangladesh helps well-liked deposit methods Perfect Money, Bkash, Sticpay, Astropay, Skrill, and Neteller. At Bet India, we solely advocate the best betting sites in India that meet these requirements so you dont should spend hours researching. Additionally, MLB gamblers can choose from numerous betting options, including participant futures, membership futures, moneylines, and props. Like many other sports activities, in cricket, you can guess not solely on the ultimate winner but add...
20:58
Water Pumps & Valves, Fans & Motors On-line Auckland Nz h+ Media
Water Pumps & Valves, Fans & Motors On-line Auckland Nz
Depending on a bookmaker to money out from, you may find that it permits you to cash out partially or fully. Partial money out is just going to return a share of what you initially invested. Then again, if you are fortunate, you might get all the money back for free with the full cash-out choice. Generally, if you see that youre going to lose the wager, that is when you must choose to cash out to scale back your losses.
If theres an space where MelBet actually units the bar, then it has to be its large vary of sports activities offerings . Are you a big online sports activities betting fan based mostly in New Zealand? If the reply is sure, then sports betting is an ideal method of boosting your bankroll when taking half in at MelBet.
Sir i have given all my paperwork however the safety group not replying since 9days..its been horrible and disappointing.as i cant withdraw with out documents verification If you wish to gamble on a protected and dependable platform, try Captain Cooks. This platform is licensed by eCOGRA and holds licenses from the UK playing fee. In this case, there are 2 bets which were mixed collectively, and the bets are Both Team to Score and Match Result.
Just as easily Melbet app free obtain on their devices. Melbet betting agency offers its users the popular on line casino card game poker. This is a good alternative not solely to study the mechanics of betting on Melbet, however moreover to get some additional winnings. The minimal deposit required to activate the bonus is Rs. seventy five.
This will allow gamblers to conduct transactions without friction and with flexibility. The casinos youll be able to choose from with $5 minimum deposit are quite many. With the luck on your facet and a budget of $5 you may have a chance to build up a bankroll to stay within the game for some time. You could make bigger bets and the potential winnings get higher. Believe it or not, soccer followers have updates about every little thing, the gamers, groups, coaches, managers, and contests. These folks even create on-line fan golf equipment which occur to be the source of all types of useful data for betting.
This one can get rid of the prospect of a draw in the soccer contest. Naturally, bettors should wager on the staff which will win- an underdog or a favorite. This sort of guess is helpful when you dont need the sport to complete with a tie. In the Totals guess, you are principally wagering on the upper or decrease score of the group in a contest. Your task is to predict and bet whether or not the staff will score over or underneath the number the sportsbook has decided.
There are greater than 100 slot games that shoppers can choose within the slots part. These are organized on the location based on the slots developed. This website screams enjoyable and friendly to entice prospects to keep on p...
20:55
22 Underdogs Ideas Underdog, Inspirational People, History h+ Media
22 Underdogs Ideas Underdog, Inspirational People, History
Operators similar to DraftKings can still supply promos of this nature, although only via their own websites. Check genuine buyer evaluations and scores from unbiased platforms. However, essentially the most famous buyer assistance choice is the reside chat device, which bettors can find at the bottom proper of the MELbet website. Youll uncover a chatbox with the name of the support personnel and the choice to rate them depending on your experience. NetEnt, Microgaming, Red Tiger Gaming, and Betsoft are among the many sport suppliers.
It shall be very inconvenient for bettors in the event that they cant attain out to the customer support staff through telephone, e-mail, or live chat. Even if a web site has essentially the most informative Frequently Asked Questions part, it wont be succesful of remedy any real-time downside the customers are having. William Hill often has enhanced odds at no cost on most of its sports activities matches. Having mentioned that, you should seek out the most effective promotions offered on different platforms and attempt to assert those that are more rewarding. There is no point in staying loyal to 1 bookie when other bookies are presenting higher deals and promos.
Read phrases and situations before doing anything, as you need to keep away from any pointless confusion attributable to poor information and understanding of the system. Reading this complete guide helps getting began, understanding the fundamentals and receiving basic pointers. Points not earned on sale gadgets, donations or reward playing cards.
As lengthy as you are signed as a lot as one of the best football betting app and have funds in your account, you can simply click on the wager you need. Claim any free bets obtainable, enter the quantity you want to gamble, and then place the bet. In fact, the extra credible the sports betting platform is, the larger the range of its markets. When you would possibly be searching for odds, you will definitely notice the differences between one of the best and the typical bookies.
For more info or assist, use the links to your proper. In India, sports betting apps are quickly picking the pace and changing into punters first choice to bet on their favourite sports and games. There are no restrictions or central legal guidelines that prevent Indian punters from utilizing betting apps in the region.
This section is entirely dedicated to video games, with out mentioning which our Melbet consider may be faraway from being accomplished. In this section, yow will uncover card video games much like poker and 21, slots, Wheel of Fortune in several variants, roulette, and one other electronic video video games. The left-hand aspect has a list of sports, the middle has crucial betting markets, and the highest half has the wager kind with a wide selection of adverts. Melbet India rewards you if you contribute...
20:35
Habitual Daily Intake of a Sweet and Fatty Snack Modulates Reward Processing in Humans SoylentNews
Why we can't keep our hands off chocolate bars and co.:
Chocolate bars, crisps and fries - why can't we just ignore them in the supermarket? Researchers at the Max Planck Institute for Metabolism Research in Cologne, in collaboration with Yale University, have now shown that foods with a high fat and sugar content change our brain: If we regularly eat even small amounts of them, the brain learns to consume precisely these foods in the future.
[...] To test this hypothesis, the researchers gave one group of volunteers a small pudding containing a lot of fat and sugar per day for eight weeks in addition to their normal diet. The other group received a pudding that contained the same number of calories but less fat. The volunteer's brain activity was measured before and during the eight weeks.
The brain's response to high-fat and high-sugar foods was greatly increased in the group that ate the high-sugar and high-fat pudding after eight weeks. This particularly activated the dopaminergic system, the region in the brain responsible for motivation and reward. "Our measurements of brain activity showed that the brain rewires itself through the consumption of chips and co. It subconsciously learns to prefer rewarding food. Through these changes in the brain, we will unconsciously always prefer the foods that contain a lot of fat and sugar," explains Marc Tittgemeyer, who led the study.
Journal paper highlights:
- Daily consumption of a high-fat/high-sugar snack alters reward
circuits in humans
- Preference for low-fat food decreases while brain response to
milkshake increases
- Neural computations that support adaptive associative learning
are also enhanced
- Effects are observed despite no change in body weight or
metabolic health
Journal Reference:
Sharmili Edwin Thanarajah, Alexandra G. DiFeliceantonio, Kerstin
Albus, et al., Habitual daily intake of a sweet and
fatty snack modulates reward processing in humans [open],
Cell Metabolism, 2023, ISSN 1550-4131, https://doi.org/10.1016/j.cmet.2023.02.015
Read more of this story at SoylentNews.
19:52
U.K. National Crime Agency Sets Up Fake DDoS-For-Hire Sites to Catch Cybercriminals The Hacker News
In what's a case of setting a thief to catch a thief, the U.K. National Crime Agency (NCA) revealed that it has created a network of fake DDoS-for-hire websites to infiltrate the online criminal underground. "All of the NCA-run sites, which have so far been accessed by around several thousand people, have been created to look like they offer the tools and services that enable cyber criminals to
19:19
Profitable India Betting On-line On Reputed Website 1xbet h+ Media
Profitable India Betting On-line On Reputed Website 1xbet
This process must be done by visiting the 1xBet main website. 1xBet has made certain that an revolutionary set of options can be found for these who wish to guess on the various video games. The first of the progressive selections would involve cryptocurrency funds, as the likes of bitcoin are supported. For those who wish to use the normal means of creating funds, the channels out there are Skrill, NETELLER, EcoPayz, Qiwi, and more.
We will inform you tips on how to deal with this problem, however first its worth mentioning that your iOS version must be no less than iOS 9.three to use the app properly. Click the Android button if you are an Android system user. Congratulations, you at the second are a full-fledged 1xBet person, all you should keep in mind your username and password. If there is a problem with this, the site automatically remembers your information and you dont have to continually take into consideration login and password. We also review one of the best sites for Indian punters to play at. Moreover, the bonus doesnt work if youre using cryptocurrencies, however thats the identical old story for many bonuses right here.
Plus, you possibly can easily make deposits and withdrawals utilizing in style strategies like Paytm, Google Pay, and UPI. Thats why weve named 7Cric as our Online Casino of the Month. At 7Cric, were devoted to making positive that our site is the go-to alternative for Indian players.
So, when you determine on becoming a member of the bookmaker and taking half in on the 1xBet web site, you need to do a couple of simple actions. They embody creating an account, logging in, choosing a sports activities match for betting or a on line casino recreation for playing, and begin having fun with the method. As for other entertainment, the positioning presents profitable slots online free on line casino from famed 1xBetbookmaker. The main advantage right here is that you can play in demo mode without using your individual funds. The alternative the best bookmaker is a assure that sports activities bets will bring you really good earnings.
This software is based on dynamic programming and is extensively considered one of the best algorithms for cricket match predictions. Choose your most well-liked fee possibility and input the amount of cash you wish to guess with . Choosing a betting website shouldnt be one thing you do without correct analysis. There are lots of of online sportsbooks out there, and we want that we are in a position to say that each one of them are good.
The 1xbet cellular utility is user-friendly, making it straightforward for Indian customers to navigate and place bets. The app is out there on both iOS and Android devices, and it presents a seamless expertise, making it simple for customers to search out their most popular sports activities and occasions....
19:17
Is 1xbet Banned In India Up To Date In 2023 March h+ Media
Is 1xbet Banned In India Up To Date In 2023 March
The 1xbet mobile application is user-friendly, making it simple for Indian users to navigate and place bets. The app is available on each iOS and Android devices, and it provides a seamless expertise, making it simple for users to search out their preferred sports activities and occasions. 1xBet India additionally provides its customers a range of stay betting and streaming choices.
The sports activities menu comes in the type of a side-scrolling listing that is displayed on the high of the betting menu, so it could all the time be accessed. In our opinion, this isnt essentially the most user-friendly approach to navigate a sports activities betting menu. 1xBet has a stay casino section that provides a broad range of game kinds. These games might be performed with a stay supplier to provide a true casino experience, and Indian gamers prefer games with Hindi-speaking stay dealers. 1xBet features a variety of deposit and withdrawal methods which are generally utilized by customers from India.
To do that, click on its icon in the principle menu of your cellular device. Also within the software, everlasting and occasion promos are available. For example, you can win a car in the Grand Slam promotion or free bets in the Big Bash!
In truth, we counted 133 different ways to deposit money into your account. Importantly, the live betting opportunities never cease, with markets out there around the clock. Match stats are posted live so youll find a way to observe the action, whereas some events are even streamed reside. The intensive alternative offered by 1XBet India additionally extends to their live betting where theres a bumper number of markets. When it involves offering nice odds, 1XBet is amongst the finest. There is always a worry that an unfamiliar betting website wont be 100% respectable, and some bad critiques can add to this sense.
1x Bet is a extremely good gambling website in India with amazing sports activities betting and online casino sections. Indian players can declare many casinos, and sports bonuses like the first deposit bonus of 20,000 and as much as 100 percent promo matches, TV Bet Accumulators and rather more. The primary function of 1x guess service is stay betting with sports activities occasions going down in real-time.
1xbet line safer bets that allow you to think twice before making a prediction. This part includes events which are nearly to begin. They start at totally different times, however at all times sooner or later, i.e. in a few minutes, hours or days. To start inserting bets at 1xbet you need to create your account, full the verification process and make your first deposit. A free app that can make your betting life easier definitely deserves your consideration. Im glad that apps of such a cool stage are already out there here.
The model provides a chance to bet on a number of cricke...
19:14
1xbet Evaluation For Indian Users h+ Media
1xbet Evaluation For Indian Users
There is a lot going for this model and customers are unlikely to make the mistake of going with 1xBet registration when attempting to guess on cricket matches. Launched in 2007, 1xBet is an online on line casino thats operated by the corporate Exinvest Limited based in Cyprus. Theyre one of many greatest betting sites youll be able to encounter in India, with an nearly overwhelming array of betting choices and on line casino video games. 1xbet app download could be easily done via their official page.
This is a welcome bonus offer from 1xbet, designed for on line casino entertainment. You can get up to 1,500 + 150 Free Spins on the most effective casino slots after your first deposit at 1xBet. To get it, you must agree to receive the bonus within the Account Settings tab. 1xBet India additionally offers phone assist to its clients.
1xBet India also presents gamers the choice to sign off with a single click. Players can deposit 1xBet India by deciding on their most popular payment technique, entering the quantity they wish to deposit, and clicking on the Deposit button. 1xBet India accepts deposits in a number of currencies, including Indian Rupees , US Dollars , and more.
1x Bet is a really good gambling website in India with wonderful sports activities betting and online on line casino sections. Indian gamers can claim many casinos, and sports activities bonuses like the first deposit bonus of 20,000 and as a lot as one hundred pc promo matches, TV Bet Accumulators and far more. The primary characteristic of 1x guess service is live betting with sports events going down in real-time.
By the best way, our research reveals that reside streaming is of good high quality and obtainable to all users free of charge. 1xbet is completely different in that cricket betting could be carried out in euros, dollars, Indian rupees, and other currencies. The Curacao-licensed firm can provide a extensive range in deciding on outcomes on high matches, as nicely as betting on the athletes stats. The common margin in each pre-match and in-play is 6-7%.
The app also has the identical functions because the desktop version, so you wont be losing out on anything. Bet India is not a betting site and we do not settle for fee from players in any form. Bet India doesnt endorse or promote unlawful gambling practices. Basically, each Friday any 1xBet person can receive a bonus of EUR . The bonus is counted as 100 percent of this quantity, however not more than one hundred EUR. This money have to be used on sports activities playing, and you cant obtain more than one.
However, not all betting websites settle for all of these methods, and a few may have completely different deposit and withdrawal limits than others. The Indian Premier League is the top-tier Twenty20 cricket league in India and some of the renowned cricket leagues on the planet. Since Crictips...
19:00
Digitizing Sound On An Unmodified Sinclair ZX81 Hackaday

Whatever the first computer you used to manipulate digital audio was, the chances are it came with dedicated sound hardware that could play, and probably record, digitized audio. Perhaps it might have been a Commodore Amiga, or maybe a PC with a Sound Blaster. If you happen to be [NICKMANN] though, you can lay claim to the honor of doing so on a machine with no such hardware, because he managed it on an unmodified Sinclair ZX81.
For those of you unfamiliar with the ZX, it embodied Clive Sinclairs usual blend of inflated promises on minimal hardware and came with the very minimum required to generate a black-and-white TV picture from a Zilog Z80 microprocessor. All it had in the way of built-in expansion was a cassette interface, 1-bit read and write ports exposed as 3.5 mm jacks on its side. Its these that in an impressive feat of hackery he managed to use as a 1-bit sampler with some Z80 assembler code, capturing a few seconds of exceptionally low quality audio in an 81 with the plug-in 16k RAM upgrade.
From 2023 of course, its about as awful as audio sampling gets, but in 1980s terms its pulling off an almost impossible feat that when we tried it with a 1-bit PC speaker a few years later, we didnt succeed at. Were impressed....
18:25
Alzheimers first signs may appear in your eyes, study finds Lifeboat News: The Blog
Finding early signs of dementia in the back of the eye may be a way to catch the disease early and start preventive treatment, a study says.
18:25
18:25
Highest-Order Electromagnetic Transition Observed Lifeboat News: The Blog
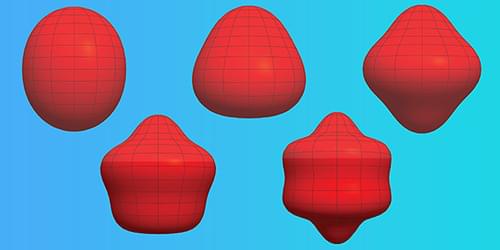
Observations deliver evidence of an exotic sixth-order electromagnetic transition in the gamma-ray emission of an iron isotope, a finding that could provide new ways to test nuclear models.
18:25
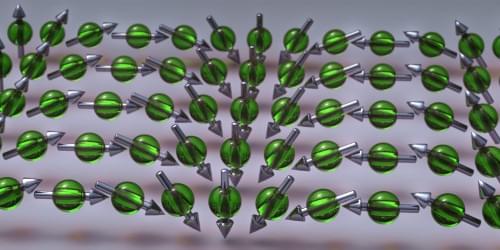
Beaming in a Spin Texture Lifeboat News: The Blog
Researchers use an optical vortex beam to create a stable pattern of electron spins in a thin layer of semiconductor material.
Spin-based electronic, or spintronic, devices can benefit from techniques that coax electron spins into static spatial patterns called spin textures. A new experiment demonstrates that an optical vortexa light beam that carries orbital angular momentumcan generate a stable spin texture in a semiconductor [1]. The research team showed that the vortex generates a pattern of stripes that has potential uses in processing spin information. Previous experiments have optically stimulated these striped textures, but the optical vortex has a structure that approximately overlaps with the stripe pattern, allowing faster spin-texture formation.
The spins of unbound electrons in a material can be aligned by a magnetic field or by polarized light. But as these electrons moveeither through diffusion or through conductiontheir spins will begin to rotate in response to so-called spin-orbit interactions within the material. The direction and rate of these rotations for any given electron depend on the path that it takes. Thus, two nearby electrons that start out aligned will become misaligned as they move along different paths, even if they arrive at the same destination. So maintaining an electronic spin texture seems like a doomed enterprise.
18:25
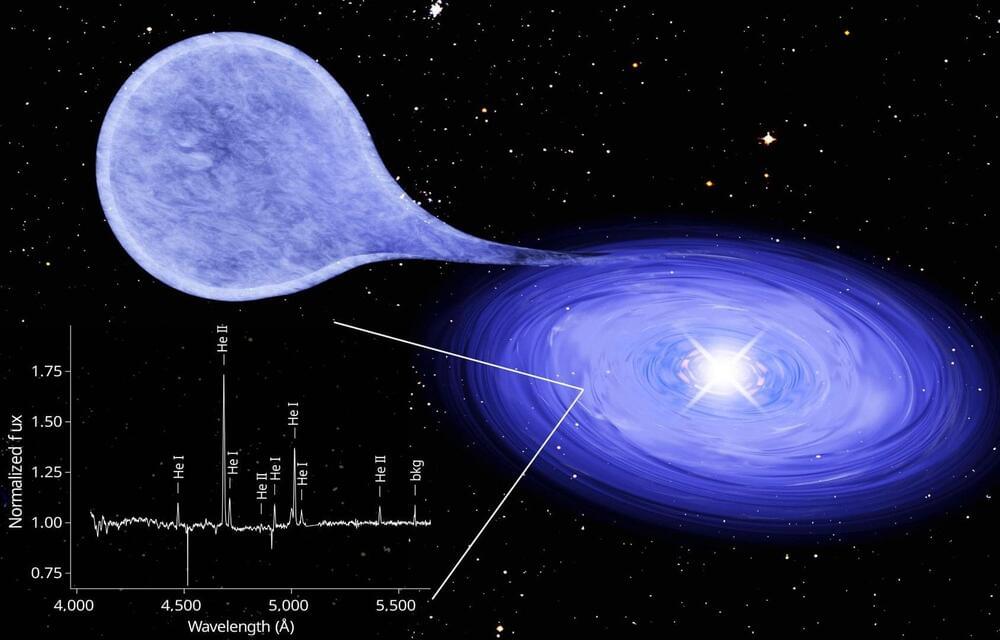
Astronomers discover helium-burning white dwarf Lifeboat News: The Blog
A white dwarf star can explode as a supernova when its mass exceeds the limit of about 1.4 solar masses. A team led by the Max Planck Institute for Extraterrestrial Physics (MPE) in Garching and involving the University of Bonn has now found a binary star system in which matter flows onto the white dwarf from its companion.
The system was found due to bright, so-called super-soft X-rays, which originate in the nuclear fusion of the overflowed gas near the surface of the white dwarf. The unusual thing about this source is that it is helium and not hydrogen that overflows and burns. The measured luminosity suggests that the mass of the white dwarf is growing more slowly than previously thought possible, which may help to understand the number of supernovae caused by exploding white dwarfs. The results have been published in the journal Nature.
Exploding white dwarfs are not only considered the main source of iron in the universe, they are also an important tool for cosmology. As so-called Type Ia supernovae (SN Ia), they all become roughly equally bright, allowing astrophysics a precise determination of the distance of their host galaxies.
18:24
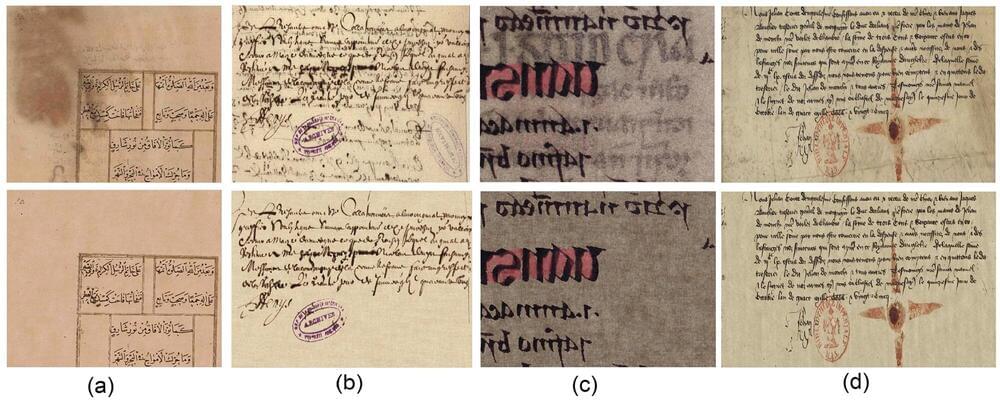
Digital restoration of historical documents Lifeboat News: The Blog
One of the best ways to learn about any historical period is by conversing with the people who lived through it. Speaking with people from the distant past is very one-sided, as they are typically dead and have stopped listening long ago. However, they speak volumes if you have the patience to listen, or rather, read what they say in letters, diaries and primitive post-it notes with no sticky back sides.
An international group of computer scientists from Italy, the U.K. and Pakistan have teamed up to resurrect the dead from writings that have been degraded by time by developing a computer-assisted method to virtually return documents to a more legible and decipherable condition. In their research paper, Restoration and content analysis of ancient manuscripts via color space based segmentation, published in the journal PLOS ONE, the team details their digital restoration techniques method and experimental results.
We get a sense of ancient civilizations from their writings, both trivial and profound. The Sumerian cuneiform writing on clay tablets reveals 4,000-year-old merchant transactions, geometric calculations, and poetry detailing the fall of a great city. Had they been written on paper and not in clay we would likely not have them today.
18:00
The world's toughest animal could one day help save your life Terra Forming Terra

Russias Economy Is Booming Despite or Because of Sanctions? Terra Forming Terra

To start with, Russia is internally able to be self
sufficient. This means zero external leverage. Thus
sanctions simply kick started supply replacement.
Russias Economy Is Booming Despite or Because of Sanctions? "Russian economic sovereignty has increased." President Putin
By Peter Koenig
Global Research, March 20, 2023
The Language of Four: The Meaning of Tetragrammaton Terra Forming Terra
Neutral Neutron Pairs Terra Forming Terra
I have slowly come to grasp just what science has been missing because normal matter is so dominating. Yet provided the neutral neutron pair is a reality, then the whole galaxy is full of this stuff, and better yet we literally breath it as well.
understand though that hydrogen is equally undetectable except by indirect means. It even penetrates matter as we know it. For that reason our proposed neutral neutron pair has a free ride past everything we can do. Accidental hits will be seen as just that and of no import.
From our knowledge of Cloud Cosmology we do have some things we can aassert:
1 The NNP does react along a number of axis allowing one NNP to be attached to another NNP. This is not what i describe as a hard lock but quite weak but still real and allows ordered conglomerates. These are in fact describable as proto Elements and Isotopes that can potentially decay into the expected elements on the basis of multiple NNP decay. They can just as easily be torn apart as well. I am not so sure that decay is taking place out in space as well as in the sun.
2 Gravitational pull is far less than for elements. The spacing is too large between NNPs. however it is not zero. Packed elements should squeeze out the majority of NNP content. This gives us the surface nature of all planets and also the Sun. This can then be a shell.
3 Understand that Cloud cosmology projects three types of neutral matter. I use the word neutral only because the word is convenient and allows us then to identify axis as separate. Neutral assumes mathematical continuity which is not real. We are now just understanding how important the NNP is in the evolution of our third level phys...
17:16
Police Needs to Intervene in the Sirius Open Source Scandal schestowitz.com
Summary: Sirius Open Source is collapsing, but that does not mean that it can dodge accountability for crimes (e.g. money that it silently stole from its staff since at least 12 years ago)
A SCREENSHOT of the PDF from Standard Life was shared here (with sensible redaction) a few days ago. Things are belatedly progressing.
This post has taken a long time to prepare as we need to separate gossip/speculation from verified facts. Standard Life also claims to be pursuing the facts (since the 7th of March). As per their own update: Dear Dr Schestowitz, I have attached our acknowledgement to your complaint. [...] If youve any questions, or problems accessing your acknowledgement, please email me at [redacted] and Ill do all I can to help you.
Theyve basically been looking into how on Earth the company (Sirius) was claiming to be paying into Standard Life accounts that dont even exist!
The simplest explanation is, Sirius engaged in embezzlement. The management was contacted several times, being kindly offered the opportunity to explain what actually happened. Each and every time the response was schtum. For reasons we detailed here before, litigation seems imminent. Class action lawsuit is also likely, though the company is in hiding. Staff that actively oversaw and participated in the embezzlement is criminally liable, even if leaving the company later. Theyve been made aware of this (fraud, theft, forgery/embezzlement among the possible charges). Failing that, or in addition to that, pension providers can be sued. Well explain the legal grounds some other day.
What does this have to do with Techrights? Sirius is describing itself as Britains most respected and best established Open Source business.
If this is what the most respected and best established boils down to, then theres serious trouble. Sirius is a major liability and a stain. This isnt the company I joined more than 12 years ago. You need to lie to keep your job or take one for the team or do something unethical/illegal to keep your salary is the hallmark or symptom of criminal management, which needs to be prosecuted, not served (except served papers). I confronted the management many times before leaving (for over a year!) and nothing improved. They kept paying the salary, but behaviour only worsened over time, so I reached out to a friend.
Suffice to say, you need not be particularly charismatic to persuade workers whom you pay to also...
17:13
Microsoft Warns of Stealthy Outlook Vulnerability Exploited by Russian Hackers The Hacker News
Microsoft on Friday shared guidance to help customers discover indicators of compromise (IoCs) associated with a recently patched Outlook vulnerability. Tracked as CVE-2023-23397 (CVSS score: 9.8), the critical flaw relates to a case of privilege escalation that could be exploited to steal NT Lan Manager (NTLM) hashes and stage a relay attack without requiring any user interaction. "External
16:51
OpenAI Reveals Redis Bug Behind ChatGPT User Data Exposure Incident The Hacker News
OpenAI on Friday disclosed that a bug in the Redis open source library was responsible for the exposure of other users' personal information and chat titles in the upstart's ChatGPT service earlier this week. The glitch, which came to light on March 20, 2023, enabled certain users to view brief descriptions of other users' conversations from the chat history sidebar, prompting the company to
16:00
A Jenkins Demo Stand For Modern Times Hackaday

Once youre working on large-scale software projects, automation
is a lifesaver, and Jenkins is a strong player in open-source
automation be it software builds, automated testing or deploying
onto your servers. Naturally, its historically been developed with
x86 infrastructure in mind, and lets be fair, x86 is getting old.
[poddingue], a hacker and a Jenkins contributor, demonstrates that
Jenkins keeps up with the times, with a hardware demo stand called
miniJen, that
has Jenkins run on three non-x86 architectures arm8v
(aarch64), armv7l and RISC-V.
Theres four SBCs of different architectures involved in this, three acting as Jenkins agents executing tasks, and one acting as a controller, all powered with a big desktop PSU from Pine64. The controllers got a bit beefier CPU for a reason at FOSDEM, weve...
15:49
Ford Will Lose $3 Billion on Electric Vehicles in 2023, It Says SoylentNews
https://arstechnica.com/cars/2023/03/ford-will-lose-3-billion-on-electric-vehicles-in-2023-it-says/
There's no doubt that Ford is embracing electrification. It was first to market with an electric pickup truck for the US market, and a darn good one at that. It has a solid midsize electric crossover that's becoming more and more common on the road, even if it does still upset the occasional Mustangophile. And there's an electric Transit van for the trades. But its electric vehicle division will lose $3 billion this year as it continues to build new factories and buy raw materials.
The news came in a peek into Ford's financials released this morning. As we reported last year, Ford has split its passenger vehicle operations into two divisions. Electric vehicles fall under Ford Model e, with internal combustion engine-powered Fords (including hybrids and plug-in hybrids) falling under Ford Blue. The move was in large part to placate investors and analysts, no doubt starry-eyed during a time when any EV-related stock was booming.
Related:
Tesla
Exceeded Revenue Estimates in Q4 2021 by More than $1 Billion
(20220127)
Tesla
Burns More Cash, Fails to Meet Production Targets
(20171102)
Ford
Investing $4.5 Billion to Bring Electrification to 40% of Its
Vehicles by 2020 (20151214)
Read more of this story at SoylentNews.
14:00
Opti9 launches Observr ransomware detection and managed services for Veeam Help Net Security
Opti9 Technologies has launched Observr Software-as-a-Service (SaaS) ransomware detection and standalone managed services two new standalone service offerings that cater to organizations leveraging Veeam Software. As the complexity of organizations IT continues to evolve, technical leaders are increasingly looking to shift ownership to 3rd party experts for critical layers of their stack. This is especially true for components such as backups and disaster recovery, which must provide resilience despite constant changes such as the More
The post Opti9 launches Observr ransomware detection and managed services for Veeam appeared first on Help Net Security.
13:00
Glowscope Reduces Microscope Cost By Orders of Magnitude Hackaday

As smartphones become more ubiquitous in society, they are being used in plenty of ways not imaginable even ten or fifteen years ago. Using its sensors to gather LIDAR information, its GPS to get directions, its microphone to instantly translate languages, or even use its WiFi and cellular radios to establish a wireless hotspot are all things which would have taken specialized hardware not more than two decades ago. The latest disruption may be in microscopy, as this build demonstrates a microscope that would otherwise be hundreds of thousands of dollars.
The microscope is a specialized device known as a fluorescence microscope, which uses a light source to excite fluorescent molecules in a sample which can illuminate structures that would otherwise be invisible under a regular microscope. For this build, the light is provided by readily-available LED lighting as well as optical filters typically used in stage lighting, as well as a garden-variety smartphone. With these techniques a microscope can be produced for around $50 USD that has 10 m resolution.
While these fluorescence microsc...
11:15
McAfee and Mastercard expand partnership to improve security for small businesses Help Net Security
McAfee has expanded partnership with Mastercard to offer Mastercard Business cardholders automatic savings on online protection solutions from McAfee through Mastercard Easy Savings. According to the latest FBI Internet Crime Report, malicious cyber activity resulted in more than $10 billion in losses in 2022, with a large portion of this affecting small businesses. Small and medium-sized companies often rely on credit cards for daily financing. Providing Mastercard Business cardholders with savings on security technology solutions More
The post McAfee and Mastercard expand partnership to improve security for small businesses appeared first on Help Net Security.
11:03
Ethical AI art generation? Adobe Firefly may be the answer. SoylentNews
On Tuesday, Adobe unveiled Firefly, its new AI image synthesis generator. Unlike other AI art models such as Stable Diffusion and DALL-E, Adobe says its Firefly engine, which can generate new images from text descriptions, has been trained solely on legal and ethical sources, making its output clear for use by commercial artists. It will be integrated directly into Creative Cloud, but for now, it is only available as a beta.
Since the mainstream debut of image synthesis models last year, the field has been fraught with issues around ethics and copyright. For example, the AI art generator called Stable Diffusion gained its ability to generate images from text descriptions after researchers trained an AI model to analyze hundreds of millions of images scraped from the Internet. Many (probably most) of those images were copyrighted and obtained without the consent of their rights holders, which led to lawsuits and protests from artists.
Related:
Paper:
Stable Diffusion "Memorizes" Some Images, Sparking Privacy
Concerns
90% of
Online Content Could be 'Generated by AI by 2025,' Expert
Says
Getty
Images Targets AI Firm For 'Copying' Photos
Adobe
Stock Begins Selling AI-Generated Artwork
A
Startup Wants to Democratize the Tech Behind DALL-E 2, Consequences
be Damned
Adobe
Creative Cloud Experience Makes It...
10:00
Dead Raspberry Pi Boards, PMICs, And New Hope Hackaday

Since the Raspberry Pi 3B+ release, the Pi boards we all know and love gained one more weakpoint the PMIC chip, responsible for generating all the power rails a Pi needs. Specifically, the new PMIC was way more vulnerable to shorting 5V and 3.3V power rails together something thats trivial to do on a Raspberry Pi, and would leave you with a bricked board. Just replacing the PMIC chip, the MxL7704, wouldnt but now, on Raspberry Pi forums, [Nefarious19] has reportedly managed to replace it and revive their Pi.
First off, you get a replacement PMIC and reflow it and thats where, to our knowledge, people have stopped so far. The next step proposed by [Nefarious19] is writing proper values into the I2C registers of the PMIC. For that, youd want a currently-alive Pi useful as both I2C controller for writing the values in, and as a sourc...
09:28
CISA announced the Pre-Ransomware Notifications initiative Security Affairs
The US Cybersecurity and Infrastructure Security Agency (CISA) announced the Pre-Ransomware Notifications service to help organizations stop ransomware attacks before damage occurs.
The US Cybersecurity and Infrastructure Security Agency announced a new Pre-Ransomware Notification initiative that aims at alerting organizations of early-stage ransomware attacks.
The principle behind the initiative is simple, ransomware actors initially gain access to the target organization, then they take some time before stealing or encrypting data. The time-lapse between initial access to a network and the encryption of the systems can last from hours to days.
Being able to notify the victims in this time window can help them to limit the damages caused by the ransomware attack.
This window gives us time to warn organizations that ransomware actors have gained initial access to their networks. reads the announcement made by the Us agency. These early warnings can enable victims to safely evict the ransomware actors from their networks before the actors have a chance to encrypt and hold critical data and systems at ransom. Early warning notifications can significantly reduce potential loss of data, impact on operations, financial ramifications, and other detrimental consequences of ransomware deployment.
The CISA Joint Cyber Defense Collaborative (JCDC) collects information about potential early-stage ransomware activity from multiple sources, including the research community, infrastructure providers, and cyber threat intelligence firms.
Then the field personnel across the country notify the victim organization and provide specific mitigation guidance. The agency will also provide notification to organizations outside of the United States through its international CERT partners.
Since the start of 2023, CISA notified over 60 entities across the energy, healthcare, water/wastewater, education, and other sectors about potential early-stage ransomware attacks. It was a success bacause many of the alerted organizations remediated the attack before encryption or exfiltration took place.
Continuing to enhance our collective cyber defense is contingent upon persistent collaboration and information sharing between partners across government and the private sector. concludes the announcement. To enable the broader cyber community to benefit from valuable threat intelligence, we urge organizations to report observed activity, including ransomware indicators of compromise and TTPs, to CISA or our federal law enforcement partners, including the FBI and the U.S. Secret Service....
08:42
Interop: One Protocol to Rule Them All? Light Blue Touchpaper
Everyones worried that the UK Online Safety Bill and the EU Child Sex Abuse Regulation will put an end to end-to-end encryption. But might a law already passed by the EU have the same effect?
The Digital Markets Act ruled that users on different platforms should be able to exchange messages with each other. This opens up a real Pandoras box. How will the networks manage keys, authenticate users, and moderate content? How much metadata will have to be shared, and how?
In our latest paper, One Protocol to Rule Them All? On Securing Interoperable Messaging, we explore the security tensions, the conflicts of interest, the usability traps, and the likely consequences for individual and institutional behaviour.
Interoperability will vastly increase the attack surface at every level in the stack from the cryptography up through usability to commercial incentives and the opportunities for government interference.
Twenty-five years ago, we warned that key escrow mechanisms would endanger cryptography by increasing complexity, even if the escrow keys themselves can be kept perfectly secure. Interoperability is complexity on steroids.
08:23
Metal-Detecting Drone Could Autonomously Find Landmines SoylentNews
A drone with 5 degrees of freedom can safely detect buried objects from the air:
Metal detecting can be a fun hobby, or it can be a task to be completed in deadly earnestif the buried treasure you're searching for includes land mines and explosive remnants of war. This is an enormous, dangerous problem: Something like 12,000 square kilometers worldwide are essentially useless and uninhabitable because of the threat of buried explosives, and thousands and thousands of people are injured or killed every year.
[...] Because the majority of mines are triggered by pressure or direct proximity, it may seem that a drone would be the ideal way to detect them nonexplosively. However, unless you're only detecting over a perfectly flat surface (and perhaps not even then) your detector won't be positioned ideally most of the time, and you might miss something, which is not a viable option for mine detection.
But now a novel combination of a metal detector and a drone with 5 degrees of freedom is under development at the Autonomous Systems Lab at ETH Zurich. It may provide a viable solution to remote land-mine detection, by using careful sensing and localization along with some twisting motors to keep the detector reliably close to the ground.
Read more of this story at SoylentNews.
08:04
China-linked hackers target telecommunication providers in the Middle East Security Affairs
Researchers reported that China-linked hackers targeted telecommunication providers in the Middle East in the first quarter of 2023.
In the first quarter of 2023, SentinelLabs researchers spotted the initial phases of attacks against telecommunication providers in the Middle East.
According to the researchers, the activity is part of the Operation Soft Cell that was first reported in June 2019 by Cybereason.
At the time, researchers at Cybereason uncovered the long-running espionage campaign tracked as Operation Soft Cell. Threat actors were targeting telco providers. Tactics, techniques, and procedures, and the type of targets suggest the involvement of a nation-state actor likely linked to Chinese APT10.
Once compromised the networks of telecommunication companies, the attackers aimed at accessing mobile phone users call data records.
SentinelLabs linked the recent attacks to a China-linked cyberespionage group in the nexus of Gallium and APT41, but the exact grouping has yet to be determined.
The threat actors employed a new dropper mechanism which is evidence of an ongoing development effort by a highly-motivated threat actor.
In collaboration with QGroup GmbH, SentinelLabs recently observed initial threat activities targeting the telecommunication sector. We assess it is highly likely that these attacks were conducted by a Chinese cyberespionage actor related to the Operation Soft Cell campaign. reads the report published by SentinelLabs. The initial attack phase involves infiltrating Internet-facing Microsoft Exchange servers to deploy webshells used for command execution. Once a foothold is established, the attackers conduct a variety of reconnaissance, credential theft, lateral movement, and data exfiltration activities.
The threat actors used a custom credential theft malware, tracked as mim221, that implemented a series of Mimikatz modifications on closed-source tooling.
actively maintained credential theft malware that was enhanced by implementing new anti-detection features.“...
08:01
ChatGPT Bug Exposed Payment Details of Paid Users HackRead | Latest Cybersecurity and Hacking News Site
OpenAI has apologized and reached out to affected users about the potential data breach.
This is a post from HackRead.com Read the original post: ChatGPT Bug Exposed Payment Details of Paid Users
07:29
Cloudflare Disables Access to Pirated Content on its IPFS Gateway TorrentFreak
 The InterPlanetary File System, more broadly known as
IPFS,
has been around for a few years now.
The InterPlanetary File System, more broadly known as
IPFS,
has been around for a few years now.
While the name may sound a little alien to the public at large, the peer-to-peer file storage network has a growing user base among the tech-savvy.
In short, IPFS is a decentralized network where users make files available to each other. A website using IPFS is served by a swarm of users in much the same way BitTorrent users share content with each other.
Completely Decentralized
The advantage of this system is that websites can become completely decentralized. If a website or other resource is hosted on IPFS, it remains accessible as long as the computer of one user who pinned it remains online.
The advantages of IPFS are clear. It allows archivists, content creators, researchers, and many others to distribute large volumes of data over the Internet. Its censorship resistant and not vulnerable to regular hosting outages.
IPFS is also a perfect match for pirate sites. Due to its decentralized nature, IPFS sites are virtually impossible to shut down. This aspect was already highlighted by Pirate Bay co-founder Peter Sunde back in 2016. More recently, IPFS was promoted by Z-Library after its domain names were seized.
Cloudflares IPFS Gateway
IPFS has also been embraced by many legal services. Most notably, Cloudflare gave it a boost by launching its own IPFS gateway, allowing the public to access IPFS resources without having to install specialized software.
Cloudflares IPFS gateway has been running for a few years now. Technically, the internet infrastructure company has no control over any of the content being made available, but that doesnt mean there are no complaints.
Apparently, some people or organizations have complained about the content that can be accessed through Cloudflares IPFS gateway.
While the accessed content is in no way controlled by Cloudflare, the San Francisco company takes these complaints rather seriously. The same also applies to the Ethereum gateway, which offers easy read-and-write access to the Ethereum network.
Cloudflare Disables IPFS Access
In its most recent...
07:00
Were the New Renewables IEEE Spectrum

The Big Picture features technology through the lens of photographers.
Every month, IEEE Spectrum selects the most stunning technology images recently captured by photographers around the world. We choose images that reflect an important advance, or a trend, or that are just mesmerizing to look at. We feature all images on our site, and one also appears on our monthly print edition.
Enjoy the latest images, and if you have suggestions, leave a comment below.

JUICE BOX
For many years, environmentalists have looked forward to the coming of net-zero-energy buildings. Much effort was devoted to making lighting, heating, and cooling more efficient so buildings consumed less energy. But the net-zero target would never have been reachable without innovations in renewable-energy generation that let structures generate power on-site. Now residential and commercial buildings can be outfitted with roofing tiles that double as solar panels, or with rooftop boxes like this low-profile unit that transforms gusts of wind into electric current. This WindBox turbine, installed on the roof of a building in Rouen, France, is 1.6 meters tall, and has a 4-square-meter footprint (leaving plenty of space for solar panels or tiles). The unit, which weighs130 kilograms, can generate up to 2,500 kilowatt-hours of electricity per year (enough to meet roughly one-quarter of the energy needs of a typical U.S. household).
Lou Benoist/AFP/Getty Images
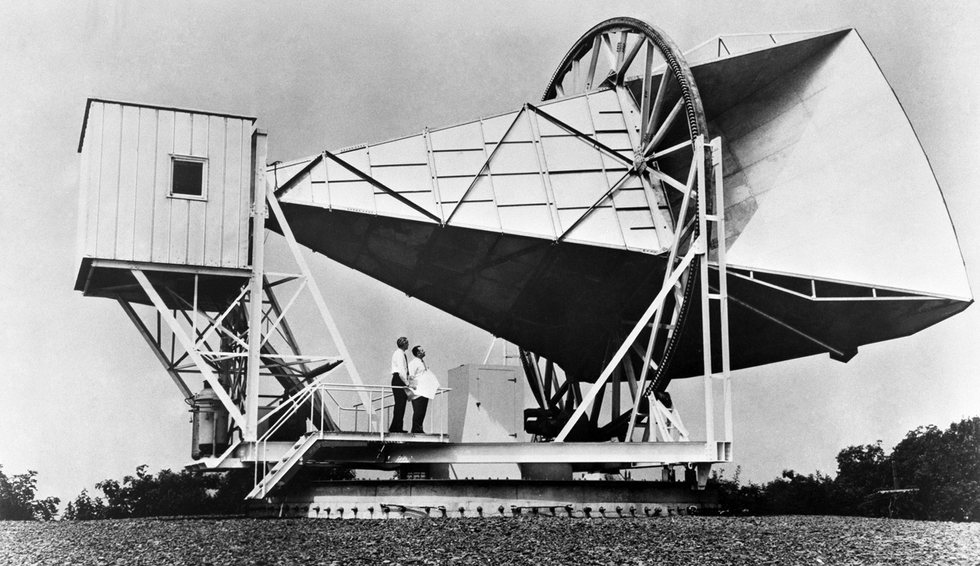
Nobel Horn Antenna Endangered
This is the giant horn antenna that was used in physics research that led to the discovery of background cosmic radiation, which provided support for the big bang theory. Two Bell Labs researchers who were painstakingly attempting to eli...
06:31
Garrett: We need better support for SSH host certificates LWN.net
Matthew Garrett looks at the recent disclosure of GitHub's private host key, how it probably came about, and what a better approach to key management might look like.
The main problem is that client tooling just doesn't handle this well. OpenSSH has no way to do TOFU for CAs, just the keys themselves. This means there's no way to do a git clone ssh://git@github.com/whatever and get a prompt asking you to trust Github's CA. Instead, you need to add a @cert-authority github.com (key) line to your known_hosts file by hand, and since approximately nobody's going to do that there's only marginal benefit in going to the effort to implement this infrastructure. The most important thing we can do to improve the security of the SSH ecosystem is to make it easier to use certificates, and that means improving the behaviour of the clients.
05:58
Re: TTY pushback vulnerabilities / TIOCSTI Open Source Security
Posted by Hanno Bck on Mar 24
Here's a proposed patch to restrict access to the dangerousfunctionality. Waiting a few days for feedback here and will then try
to send it to the appropriate kernel lists.
------------------
Restrict access to TIOCLINUX selection functions
These functions can be used for privilege escalation when code is
executed with tools like su/sudo.
Signed-off-by: Hanno Bck <hanno () hboeck de>
---
drivers/tty/vt/vt.c | 6 ++++++
1 file...
05:36
City of Toronto is one of the victims hacked by Clop gang using GoAnywhere zero-day Security Affairs
Clop ransomware gang added the City of Toronto to the list of its victims, it is another organization compromised by exploiting GoAnywhere zero-day.
Clop ransomware gang added the City of Toronto to the list of victims published on its Tor leak site. The City was targeted as part of a campaign exploiting the recently disclosed zero-day vulnerability in the Fortras GoAnywhere secure file transfer tool.
The gang is very active and recently it claimed to have breached tens of large organizations, including Rubrik, Onex, Axis, Bank, Rio Tinto, Hitachi Energy, and Virgin Group, as reported by the security expert Dominic Alvieri.
The news of the hack was also confirmed by BleepingComputer which reached a spokesperson for the City of Toronto. The City government launched an investigation into the incident to determine the extent of the security breach.
Today, the City of Toronto has confirmed that unauthorized access to City data did occur through a third party vendor. The access is limited to files that were unable to be processed through the third party secure file transfer system. a City spokesperson told BleepingComputer.
In early February, the popular investigator Brian Krebs first revealed details about the zero-day on Mastodon and pointed out that Fortra has yet to share a public a...
05:33
Reverse-Engineering the Multiplication Algorithm in the Intel 8086 Processor SoylentNews
http://www.righto.com/2023/03/8086-multiplication-microcode.html
While programmers today take multiplication for granted, most microprocessors in the 1970s could only add and subtract multiplication required a slow and tedious loop implemented in assembly code.1 One of the nice features of the Intel 8086 processor (1978) was that it provided machine instructions for multiplication,2 able to multiply 8-bit or 16-bit numbers with a single instruction. Internally, the 8086 still performed a loop, but the loop was implemented in microcode: faster and transparent to the programmer. Even so, multiplication was a slow operation, about 24 to 30 times slower than addition.
In this blog post, I explain the multiplication process inside the 8086, analyze the microcode that it used, and discuss the hardware circuitry that helped it out.3 My analysis is based on reverse-engineering the 8086 from die photos. The die photo below shows the chip under a microscope. I've labeled the key functional blocks; the ones that are important to this post are darker. At the left, the ALU (Arithmetic/Logic Unit) performs the arithmetic operations at the heart of multiplication: addition and shifts. Multiplication also uses a few other hardware features: the X register, the F1 flag, and a loop counter.
Read more of this story at SoylentNews.
05:28
UKs NCA infiltrates cybercrime market with fake DDoS sites HackRead | Latest Cybersecurity and Hacking News Site
By Waqas
The National Crime Agency (NCA) has conducted a sting operation to infiltrate the cybercrime market with fake DDoS sites for Operation Power Off.
This is a post from HackRead.com Read the original post: UKs NCA infiltrates cybercrime market with fake DDoS sites
05:27
Victory at the Ninth Circuit: Twitters Content Moderation is Not State Action Deeplinks
Earlier this month, the Ninth Circuit held that Twitter did not act as the government by banning a user months after a government agency flagged for Twitter one of his tweets on alleged election fraud. OHandley v. Weber is the latest decision rejecting social media users attempts to hold platforms liable for deleting, demonetizing, and otherwise moderating their content.
Twitter is a private entity, so the government and the courts cannot tell it what speech it must remove or what speech it must carry. The First Amendment restricts censorship only by the government, not private entities, unless those entities are using government power or otherwise effectively acting as the government. But in OHandley, even if Twitter and the government were generally aligned in their missions to limit the spread of misleading election information[, s]uch alignment does not transform private conduct into state action.
Moreover, as we argued in our amicus brief in the case, holding Twitter liable for content moderation would likely violate the platforms own First Amendment rights. For example, when Twitter took down plaintiff Rogan OHandleys tweets and then his account, it made an editorial decision about what content it would publish.
OHandleys lawsuit, relied on the fact that the California Office of Election Cybersecurity flagged one of OHandleys tweets for supposedly violating Twitters misinformation policy. But as the Ninth Circuit explained, Twitter developed and applied that policy at its discretion, and the government did not order Twitter to take any action. The court said, and we argued in our brief, that Twitter is not a state actor unless it ceded control over its content moderation process to the government. In general, the government is free to talk to Twitter, and Twitter is free to listen (or not listen).
The Ninth Circuit pointed specifically to Twitters user agreement with OHandley as justifying the content moderation, and declined to say whether the First Amendment also protects that moderation. But many other courts have dismissed these must carry lawsuits under the First Amendment, including the lower court in this case. OHandley is the Ninth Circuits second ...
04:42
Britain: Food Inflation Hit Highest Rate Since 1977, Increased 18.2% in the Year to Februaury 2023 cryptogon.com
Via: Grocery Gazette: Food inflation hit its highest rate since 1977 last month, having risen to 18.2% in the year to Februaury 2023. The Office for National Statistics (ONS) saw this jump from 16.8% in January, with the increase driven by price movements such as the rise in cost of vegetables last month.
04:35
Banks Are Still Drawing on the Fed for $164 Billion of Emergency Cash cryptogon.com
Via: Bloomberg: Banks reduced their borrowings only slightly from two Federal Reserve backstop facilities in the most recent week, a sign that institutions are taking advantage of the central banks liquidity in the wake of turmoil.
04:28
Intel XeSS SDK 1.1 Released Phoronix
The Intel XeSS SDK 1.0 release happened last September while now has been succeeded by XeSS SDK 1.1. Though like the prior release, the XeSS SDK isn't fully open-source with just the bits around game integration being public...
04:12
We need better support for SSH host certificates Matthew Garrett
Github accidentally
committed their SSH RSA private key to a repository, and now a
bunch of people's infrastructure is broken because it needs to be
updated to trust the new key. This is obviously bad, but what's
frustrating is that there's no inherent need for it to be -
almost all the technological components needed to both
reduce the initial risk and to make the transition seamless already
exist.
But first, let's talk about what actually happened here. You're
probably used to the idea of TLS certificates from using browsers.
Every website that supports TLS has an asymmetric pair of keys
divided into a public key and a private key. When you contact the
website, it gives you a certificate that contains the public key,
and your browser then performs a series of cryptographic operations
against it to (a) verify that the remote site possesses the private
key (which prevents someone just copying the certificate to another
system and pretending to be the legitimate site), and (b) generate
an ephemeral encryption key that's used to actually encrypt the
traffic between your browser and the site. But what stops an
attacker from simply giving you a fake certificate that contains
their public key? The certificate is itself signed by a certificate
authority (CA), and your browser is configured to trust a
preconfigured set of CAs. CAs will not give someone a signed
certificate unless they prove they have legitimate ownership of the
site in question, so (in theory) an attacker will never be able to
obtain a fake certificate for a legitimate site.
This infrastructure is used for pretty much every protocol that can
use TLS, including things like SMTP and IMAP. But SSH doesn't use
TLS, and doesn't participate in any of this infrastructure.
Instead, SSH tends to take a "Trust on First Use" (TOFU) model -
the first time you ssh into a server, you receive a prompt asking
you whether you trust its public key, and then you probably hit the
"Yes" button and get on with your life. This works fine up until
the point where the key changes, and SSH suddenly starts
complaining that there's a mismatch and something awful could be
happening (like someone intercepting your traffic and directing it
to their own server with their own keys). Users are then supposed
to verify whether this change is legitimate, and if so remove the
old keys and add the new ones. This is tedious and risks users just
saying "Yes" again, and if it happens too often an attacker can
simply redirect target users to their own server and through sheer
fatigue at dealing with this crap the user will probably trust the
malicious server.
Why not certificates? OpenSSH actually does support
certificates, but not in the way you might expect. There's a
custom format that's significantly less compl...
03:47
Video Friday: Lunar Base IEEE Spectrum
Video Friday is your weekly selection of awesome robotics
videos, collected by your friends at IEEE Spectrum
robotics. We also post a weekly calendar of upcoming robotics
events for the next few months. Please
send us your events for inclusion.
Robotics Summit & Expo: 1011 May 2023, BOSTON
ICRA 2023: 29 May2 June 2023, LONDON
RoboCup 2023: 410 July 2023, BORDEAUX, FRANCE
RSS 2023: 1014 July 2023, DAEGU, SOUTH KOREA
IEEE RO-MAN 2023: 2831 August 2023, BUSAN, SOUTH KOREA
CLAWAR 2023: 24 October 2023, FLORIANOPOLIS, BRAZIL
Humanoids 2023: 1214 December 2023, AUSTIN, TEXAS
Enjoy todays videos!
GITAI conducted a demonstration of lunar base construction using two GITAI inchworm-type robotic arms and two GITAI Lunar Robotic Rovers in a simulated lunar environment and successfully completed all planned tasks. The GITAI robots have successfully passed various tests corresponding to Level 4 of NASAs Technology Readiness Levels (TRL) in a simulated lunar environment in the desert.
[ GITAI ]
Thanks, Sho!
This is 30 minutes of Agility Robotics Digit being productive at ProMat. The fact that it gets boring and repetitive to watch reinforces how much this process needs robots, and is also remarkable because bipedal robots can now be seen as just another tool.
...
03:01
How I created a Red Hat OpenShift cluster on tiny hardware Linux.com
Build an OpenShift cluster on a small, sub-$300 computer.
Read More at Enable Sysadmin
The post How I created a Red Hat OpenShift cluster on tiny hardware appeared first on Linux.com.
02:47
Latitude Hack Worsens With Services Taken Offline SoylentNews
The situation for the Latitude hack has become worse with the owners forced to take the site offline.
The non-bank lender confirmed that Medicare numbers and "copies of passports or passport numbers" were included in the theft of personal information affecting approximately 333,000 customers and applicants.
[...] Latitude said of the stolen information, approximately 96 per cent was "copies of drivers' licences or driver licence numbers", "less than 4 per cent was copies of passports or passport numbers" and "less than 1 per cent was Medicare numbers".
"Because the attack remains active, we have taken our platforms offline and are unable to service our customers and merchant partners," the statement said.
[...] But frustrated customers have hit out at Latitude's handling of the hacking describing it as "pathetic" and "disgusting".
"How long will it take to find out if I am affected? If my details have been stolen I'd like to know now. Identity theft and/or financial ruin due to your lack of security and saving items such as my drivers licence is not okay," one woman wrote on social media.
"We need more information asap," one woman pleaded. "Do we need to change our licences, change our bank accounts? As this has been happening lots what have you done with your cyber security? As a ex Security officer this is a major huge breach and should not happen. Someone dropped the ball big time."
Previously it had only been confirmed that drivers' licences were taken.
Read more of this story at SoylentNews.
02:26
CVE-2022-47502: Apache OpenOffice: Macro URL arbitrary script execution Open Source Security
Posted by Marcus Lange on Mar 24
Severity: criticalDescription:
Apache OpenOffice documents can contain links that call internal macros with arbitrary arguments. Several URI Schemes
are defined for this purpose.
Links can be activated by clicks, or by automatic document events.
The execution of such links must be subject to user approval.
In the affected versions of OpenOffice, approval for certain links is not requested; when activated, such links could
therefore...
02:24
CVE-2022-38745: Apache OpenOffice: Empty entry in Java class path Open Source Security
Posted by Marcus Lange on Mar 24
Severity: moderateDescription:
Apache OpenOffice versions before 4.1.14 may be configured to add an empty entry to the Java class path. This may lead
to run arbitrary Java code from the current directory.
Credit:
European Commission's Open Source Programme Office (sponsor)
References:
https://openoffice.apache.org/
https://www.cve.org/CVERecord?id=CVE-2022-38745
01:57
IRC Proceedings: Thursday, March 23, 2023 Techrights
Also available via the Gemini protocol at:
- gemini://gemini.techrights.org/irc-gmi/irc-log-techrights-230323.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-230323.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-social-230323.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-techbytes-230323.gmi
Over HTTP:
|
... |
01:48
AMD FidelityFX Super Resolution 3 "FSR 3" Will Be Open-Source Phoronix
AMD has been teasing FidelityFX Super Resolution 3 (FSR3) as the later in the year. AMD began showing off FSR 3 to game developers this week at GDC while also re-affirming their open-source commitment...
01:45
Critical flaw in WooCommerce Payments plugin allows site takeover Security Affairs
A patch for a critical vulnerability in the WooCommerce Payments plugin for WordPress has been released for over 500,000 websites.
On March 23, 2023, researchers from Wordfence observed that the WooCommerce Payments Fully Integrated Solution Built and Supported by
The WooCommerce Payments plugin is a fully integrated payment solution for the WooCommerce open source e-commerce platform, the plugin is developed by Automattic. WooCommerce Payments is installed on over 500,000 sites.
The researchers analyzed the patch and determined that the development team behind the plugin has removed a portion of code that could have allowed an unauthenticated attacker to impersonate an administrator and completely take over a WordPress website without any user interaction.
The vulnerability impacts plugin versions 4.8.0 through 5.6.1, it was first discovered by Michael Mazzolini from penetration testing firm GoldNetwork.
We developed a Proof of Concept and began writing and testing a firewall rule immediately. The rule was released the same day, on March 23, 2023 to Wordfence Premium, Wordfence Care, and Wordfence Response customers. reads the advisory published by Wordfence.
Payments plugin, which is 5.6.2 as of this writing, immediately.According to the analysis conducted by the WordPress security firm Sucuri, the vulnerability resides in a PHP file called class-platform-checkout-session.php.
Automattic is issuing automatic/forced updates of all WordPress websites using its plugin.
WooCommerce recommends admins of websites using the plugin to:
- Update woocommerce-payments to
- Change all administrator passwords...
01:30
Intel Arc Graphics Show Good Potential For Linux Workstation OpenGL Performance Phoronix
Recently I provided a fresh look at the Intel Arc Graphics Linux gaming performance with the newest open-source drivers. While it was a letdown with some of the newer Steam Play games still not working due to current limitations of the Intel "ANV" open-source Vulkan driver and some Vulkan performance issues in other titles, one area that stood out was the very good Linux OpenGL performance. That made me curious to look at the workstation OpenGL performance for Intel Arc Graphics, which is the focus of today's testing.
01:28
[$] User-space shadow stacks (maybe) for 6.4 LWN.net
Support for shadow stacks on the x86 architecture has been long in coming; LWN first covered this work in 2018. After five years and numerous versions, though, it would appear that user-space shadow stacks on x86 might just be supported in the 6.4 kernel release. Getting there has required a few changes since we last caught up with this work in early 2022.
01:15
Wine's VKD3D 1.7 Implements More Direct3D 12 Functionality Atop Vulkan Phoronix
Not to be confused with Valve's downstream, VKD3D-Proton, that is used by Steam Play but Wine's VKD3D codebase itself is out today implementation...
01:04
Links 24/03/2023: Social Control Media Bans Advancing Techrights
![]()
Contents
- GNU/Linux
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Leftovers
- Science
- Education
- Hardware
- Health/Nutrition/Agriculture
- Proprietary
- Security
- Defence/Aggression
- Transparency/Investigative Reporting
- Environment
- Finance
- AstroTurf/Lobbying/Politics
- Censorship/Free Speech
- Freedom of Information / Freedom of the Press
- Civil Rights/Policing
- Digital Restrictions (DRM)
- Monopolies
-
GNU/Linux
-
Desktop/Laptop
-
Unix Men Switching To Linux Mint: The Benefits and Drawbacks
Deciding to spend hundreds of dollars on new hardware be it a laptop or a desktop component is always a tough call. You might spend hours considering your options and working out the budget.
But its also natural to think about all the money you spent buying, upgrading, and maintaining your current setup. Your desktop or laptop might not be broken. Rather, it might not be performing as well as you think it should.
Installing a...
-
-
01:00
This Week in Security: USB Boom! Acropalypse, and a Bitcoin Heist Hackaday

Weve covered a lot of sketchy USB devices over the years. And surely you know by now, if you find a USB drive, dont plug it in to your computer. Theres more that could go wrong than just a malicious executable. Weve covered creative and destructive ideas here on Hackaday, from creative firmware to capacitors that fry a machine when plugged in. But what happened to a handful of Ecuadorian journalists was quite the surprise. These drives went out with a bang.
That is, they literally exploded. The drives each reportedly contained a pellet of RDX, a popular explosive in use by militaries since the second World War. There have been five of these hyperactive USB devices located so far, and only one actually detonated. It seems that one only managed to trigger half of its RDX payload. Because of this, and the small overall size of a USB drive, the explosion was more comparable to a firecracker than a bomb.
Mr Self Destruct v1 pic.twitter.com/aFloN5VGKI
MG (@_MG_) October 6, 2017
...
00:44
Journalist Targeted in USB Drive Bombing Attack HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
According to the attorney general of Ecuador, a terrorism investigation has been launched after the incident took place in the country.
This is a post from HackRead.com Read the original post: Journalist Targeted in USB Drive Bombing Attack
00:40
Malicious Python Package Uses Unicode Trickery to Evade Detection and Steal Data The Hacker News
A malicious Python package on the Python Package Index (PyPI) repository has been found to use Unicode as a trick to evade detection and deploy an info-stealing malware. The package in question, named onyxproxy, was uploaded to PyPI on March 15, 2023, and comes with capabilities to harvest and exfiltrate credentials and other valuable data. It has since been taken down, but not before attracting
00:34
Security updates for Friday LWN.net
Security updates have been issued by Debian (chromium, libdatetime-timezone-perl, and tzdata), Fedora (flatpak and gmailctl), Mageia (firefox, flatpak, golang, gssntlmssp, libmicrohttpd, libtiff, python-flask-security, python-owslib, ruby-rack, thunderbird, unarj, and vim), Red Hat (firefox, kpatch-patch, nss, openssl, and thunderbird), SUSE (containerd, hdf5, qt6-base, and squirrel), and Ubuntu (amanda, gif2apng, graphviz, and linux, linux-aws, linux-azure, linux-gcp, linux-ibm, linux-kvm, linux-lowlatency, linux-oracle, linux-raspi).
00:06
Ring of Life? Terminator Habitability around M-dwarfs Centauri Dreams Imagining and Planning Interstellar Exploration
It would come as no surprise to readers of science fiction that the so-called terminator region on certain kinds of planets might be a place where the conditions for life can emerge. Im talking about planets that experience tidal lock to their star, as habitable zone worlds around some categories of M-dwarfs most likely do. But I can also go way back to science fiction read in my childhood to recall a story set, for example, on Mercury, then supposed to be locked to the Sun in its rotation, depicting humans setting up bases on the terminator zone between broiling dayside and frigid night.
Addendum: Can you name the science fiction story Im talking about here? Because I cant recall it, though I suspect the setting on Mercury was in one of the Winston series of juvenile novels I was absorbing in that era as a wide-eyed kid.
The subject of tidal lock is an especially interesting one because we have candidates for habitable planets around stars as close as Proxima Centauri, if indeed a possibly tidally locked planet can sustain clement conditions at the surface. Planets like this are subject to extreme conditions, with a nightside that receives no incoming radiation and an irradiated dayside where greenhouse effects might dominate depending on available water vapor. Even so, moderate temperatures can be achieved in models of planets with oceans, and most earlier work has gone into modeling water worlds. I also think its accurate to say that earlier work has focused on how habitable conditions might be maintained in the substellar eye region directly facing the star.
But what about planets that are largely covered in land? Its a pointed question because a new study in The Astrophysical Journal finds that tidally locked worlds mostly covered in water would eventually become saturated by a thick layer of vapor. The study, led by Ana Lobos (UC-Irvine) also finds that plentiful land surfaces produce a terminator region that could well be friendly to life even if the equatorial zone directly beneath the star on the dayside should prove inhospitable. Says Lobo:
...We are trying to draw attention to more water-limited planets, which despite not having widespread oceans, could have lakes or other smaller bodies of liquid water, and these climates could actually be very promising.
00:01
Fourier Transformations Reveal How AI Learns Complex Physics SoylentNews
Fourier Transformations Reveal How AI Learns Complex Physics:
One of the oldest tools in computational physics a 200-year-old mathematical technique known as Fourier analysis can reveal crucial information about how a form of artificial intelligence called a deep neural network learns to perform tasks involving complex physics like climate and turbulence modeling, according to a new study.
In the paper, Hassanzadeh, Adam Subel and Ashesh Chattopadhyay, both former students, and Yifei Guan, a postdoctoral research associate, detailed their use of Fourier analysis to study a deep learning neural network that was trained to recognize complex flows of air in the atmosphere or water in the ocean and to predict how those flows would change over time. Their analysis revealed "not only what the neural network had learned, it also enabled us to directly connect what the network had learned to the physics of the complex system it was modeling," Hassanzadeh said.
"Deep neural networks are infamously hard to understand and are often considered 'black boxes,'" he said. "That is one of the major concerns with using deep neural networks in scientific applications. The other is generalizability: These networks cannot work for a system that is different from the one for which they were trained."
Hassanzadeh's team first performed the Fourier transformation on the equation of its fully trained deep-learning model. Each of the model's approximately 1 million parameters act like multipliers, applying more or less weight to specific operations in the equation during model calculations. In an untrained model, parameters have random values. These are adjusted and honed during training as the algorithm gradually learns to arrive at predictions that are closer and closer to the known outcomes in training cases. Structurally, the model parameters are grouped in some 40,000 five-by-five matrices, or kernels.
Read more of this story at SoylentNews.
Friday, 24 March
23:31
CISA releases free tool for detecting malicious activity in Microsoft cloud environments Help Net Security
Network defenders searching for malicious activity in their Microsoft Azure, Azure Active Directory (AAD), and Microsoft 365 (M365) cloud environments have a new free solution at their disposal: Untitled Goose Tool. Released by the Cybersecurity and Infrastructure Security Agency (CISA), it is an open-source tool that allows users to export and review logs, alerts, configurations, cloud artifacts, and more. The tools capabilities As an agency charged with among other things helping US-based organizations More
The post CISA releases free tool for detecting malicious activity in Microsoft cloud environments appeared first on Help Net Security.
22:50
Intel vPro platform unveils advanced security measures Help Net Security
Intel has launched the latest Intel vPro platform, which is powered by 13th Gen Intel Core processors and offers a broad range of features, including powerful security measures. The extensive commercial portfolio will offer over 170 laptops, desktops, and entry-level workstations, in collaboration with Acer, ASUS, Dell, HP, Lenovo, Fujitsu, Panasonic, and Samsung. IDCs latest report suggests that Windows PCs running on Intel-based processors have a 26% lower chance of experiencing significant security events than More
The post Intel vPro platform unveils advanced security measures appeared first on Help Net Security.
22:43
THN Webinar: Inside the High Risk of 3rd-Party SaaS Apps The Hacker News
Any app that can improve business operations is quickly added to the SaaS stack. However, employees don't realize that this SaaS-to-SaaS connectivity, which typically takes place outside the view of the security team, significantly increases risk. Whether employees connect through Microsoft 365, Google Workspace, Slack, Salesforce, or any other app, security teams have no way to quantify their
22:06
GitHub Swiftly Replaces Exposed RSA SSH Key to Protect Git Operations The Hacker News
Cloud-based repository hosting service GitHub said it took the step of replacing its RSA SSH host key used to secure Git operations "out of an abundance of caution" after it was briefly exposed in a public repository. The activity, which was carried out at 05:00 UTC on March 24, 2023, is said to have been undertaken as a measure to prevent any bad actor from impersonating the service or
22:00
SheepShaver: A Cross-Platform Tool For Retro Enthusiasts Hackaday

The world of desktop computing has coalesced into what is essentially a duopoly, with Windows machines making up the bulk of the market share and Apple carving out a dedicated minority. This relatively stable state hasnt always existed, though, as the computing scene even as late as the 90s was awash with all kinds of competing operating systems and various incompatible hardware. Amiga, Unix, OS/2, MacOS, NeXT, BeOS, as well as competing DOSes, were all on the table at various points.
If youve still got a box running one of these retro systems, SheepShaver might be able to help expand your software library. Its not the sort of virtualization that were used to in the modern world, with an entire operating system running on a sanctioned-off part of your system. But SheepShaver does allow you to run software written for MacOS 7.5.2 thru 9.0.4 in a different environment. Unix and Linux are both supported, as well as Mac OS X, Windows NT, 2000, and XP, and the enigmatic BeOS. Certain configurations allow applications to run natively without any emulation at all, and there is plenty of hardware support built-in as well.
For anyone running retro hardware from the late 90s or early 00s, this could be just the ticket to get an application running that wasn...
21:39
Pwn2Own Vancouver 2023 Day 2: Microsoft Teams, Oracle VirtualBox, and Tesla hacked Security Affairs
On the second day of Pwn2Own Vancouver 2023, the organization awarded $475,000 for 10 unique zero-day vulnerabilities.
On the second day of Pwn2Own Vancouver 2023, the organization awarded $475,000 for 10 unique zero-day vulnerabilities, bringing the total awarded to $850,000!
The bug hunters demonstrated zero-day attacks against the Oracle VirtualBox virtualization platform, Microsoft Teams, Tesla Model 3, and the Ubuntu Desktop OS.
The day began with the success/collision achieved by Thomas Imbert (@masthoon) and Thomas Bouzerar (@MajorTomSec) from Synacktiv (@Synacktiv) demonstrating a 3-bug chain against Oracle VirtualBox with a Host EoP. The success was classified as a collision because one of the bugs exploited in the attack was previously known. The due earned $80,000 and 8 Master of Pwn points.
The researchers @hoangnx99, @rskvp93, and @_q5ca from Team Viettel (@vcslab) chained 2 vulnerabilities to hack Microsoft Teams. They earn $75,000 and 8 Master of Pwn points.
Of course, the most interesting attack was conducted by David Berard (@_p0ly_) and Vincent Dehors (@vdehors) from Synacktiv (@Synacktiv) who exploited a heap overflow and an OOB write to hack Tesla Infotainment Unconfined Root. They qualify for a Tier 2 award, earning $250,000 and 25 Master of Pwn points. The team also won the Tesla Model 3 they have hacked.
The researcher dungdm (@_piers2) of Team Viettel (@vcslab) exploit...
21:37
Intel Prepares More Meteor Lake Graphics Code For Linux 6.4 Phoronix
Intel's open-source engineers continue to be quite busy working on their Meteor Lake enablement ahead of those initial mobile processors shipping later this year...
21:26
AMDGPU Linux Driver Gets Ready For eDP 1.5 Panels With 6.75 Gbps/Lane Phoronix
Sent out today were the latest AMDGPU Display Core "DC" patches having the latest work done by AMD internally on this display/monitor portion of their driver code. Notable with this round of 19 patches is preparation work for upcoming eDP 1.5 laptop displays...
21:17
'Time Reflections' Finally Observed by Physicists After Decades of Searching SoylentNews
Reflections in time instead of space:
Walk through a maze of mirrors, you'll soon come face to face with yourself. Your nose meets your nose, your fingertips touch at their phantom twins, stopped abruptly by a boundary of glass.
Most of the time, a reflection needs no explanation. The collision of light with the mirror's surface is almost intuitive, its rays set on a new path through space with the same ease as a ball bouncing off a wall.
For over sixty years, however, physicists have considered a subtly different kind of reflection. One that occurs not through the three dimensions of space, but in time.
Now researchers from the City University of New York's Advanced Science Research Center (CUNY ASRC) have turned the theory of 'time reflections' into practice, providing the first experimental evidence of its manipulation across the electromagnetic spectrum.
[...] Put aside thoughts of TARDIS-like technologies rewriting history. This kind of time reflection is even weirder. And, it seems, actually possible after all.
By the 1970s, it was becoming clear that there was an analog for spatial reflection in the time component of a quantum wave of light. Change the medium a wave is traveling through quickly enough, in just the right way, and the temporal component of the wave will change with it.
The effect of this reflection in time isn't going to rip a hole in reality. But It will shift the frequency of the wave, in ways technology could exploit across varied fields like imaging, analogue computing, and optical filtering.
Strangely, the 'echo' of altered frequency is also a reversal of the signal. If it was an echo of your voice counting one to ten, you'd hear each number spoken backwards, from ten back to one, in a chipmunk squeak.
Read more of this story at SoylentNews.
20:59
Researchers Uncover Chinese Nation State Hackers' Deceptive Attack Strategies The Hacker News
A recent campaign undertaken by Earth Preta indicates that nation-state groups aligned with China are getting increasingly proficient at bypassing security solutions. The threat actor, active since at least 2012, is tracked by the broader cybersecurity community under Bronze President, HoneyMyte, Mustang Panda, RedDelta, and Red Lich. Attack chains mounted by the group commence with a
20:34
New Pirate IPTV Bill Moved to Senate as Italy Takes on Digital Mafias TorrentFreak
 Italian consumers love for pirate IPTV services and the
alleged damage suffered by broadcasters and the countrys
world-famous clubs at the hands of those services, have been on a
collision course for some time.
Italian consumers love for pirate IPTV services and the
alleged damage suffered by broadcasters and the countrys
world-famous clubs at the hands of those services, have been on a
collision course for some time.
Italy has operated an administrative pirate site-blocking program for years. It currently blocks around 3,200+ pirate domains, with telecoms regulator AGCOM sometimes issuing blocking instructions to ISPs within days of a rightsholder complaint.
Defending live sporting events from ubiquitous pirate IPTV streams demands a whole lot more, though. After gaining and maintaining momentum, alongside increasing political pressure, it seems likely that football clubs and broadcasters are about to collect.
Push For The Big Anti-Piracy Bill
By the middle of 2022, support for radical action to shut down the flow of pirate streams was building in Italy. Unprecedented blocking measures, new powers for telecoms regulator AGCOM, punishments for stream suppliers, even punishments for those in the telecoms sector who fail to block them, sat firmly on the table.
Working against the clock in December 2022, the new standards were laid out, one in particular. ISPs would be required to block pirate IPTV streams without delay and in real time most likely having been informed well in advance of what to shut down.
Anti-Piracy Bill Unanimously Approved
This week in the Chamber of Deputies, Italys lower house of parliament, the football and broadcasting industry-developed anti-piracy bill was unanimously waved through to the final.
If the bill meets with the approval of the Senate, as it almost certainly will, the new law will attempt to strangle the availability of pirate streams and punish suppliers and consumers of those that get through.
20:08
New distros list statistics Open Source Security
Posted by Anthony Liguori on Mar 24
Hi,I've been working to automate[*] tracking posting on the distros@ mailing
list for reporting purposes. This includes searching oss-security for
posting information, extracting CVEs, and trying to tie it all together.
Anywhere, I have full stats for 2022 and stats for Jan/Feb of 2023. As
long as everyone is happy with the content, I'll update regularly moving
forward....
20:03
Links 24/03/2023: GNU Grep 3.10 and Microsoft Accenture in a Freefall Techrights
![]()
Contents
- GNU/Linux
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Leftovers
-
GNU/Linux
-
Desktop/Laptop
-
Linux Gizmos Framework presents new DIY upgradeable laptops
Framework introduced today their Framework Laptop 13 DIY Edition compatible with the AMD Ryzen 7040 Series processors and 13th Gen Intel processors. These highly customizable laptops are available to pre-order starting at $849.00.
...
-
-
19:45
The ISDC 2023 (International Space Development Conference) will be held May 25-28 in Dallas-Frisco, Texas. Lifeboat News
The ISDC 2023 (International Space Development Conference) will be held May 2528 in Dallas-Frisco, Texas.
Our Gary Barnhard, Sherry Bell, Michelle L.D. Hanlon, Janet Ivey, David Livingston, Holly Melear, Rod Pyle, Martine Rothblatt, and Dylan Taylor will be speaking/participating.19:00
CNC Intaglio-Esque Engraving Hackaday

Intaglio is an ancient carving technique for adding details to a workpiece, by manually removing material from a surface with only basic hand tools. If enough material depth is removed, the resulting piece can be used as a stamp, as was the case with rings, used to stamp the wax seals of verified letters. [Nicolas Tranchant] works in the jewelry industry, and wondered if he could press a CNC engraving machine into service to engrave gemstones in a more time-efficient manner than the manual carving methods of old.
Engraving and machining generally work only if the tool you are using is mechanically harder than the material the workpiece is made from. In this case, this property is measured on the Mohs scale, which is a qualitative measurement of the ability of one (harder) material to scratch another. Diamond is the hardest known material on the Mohs scale and has a Mohs hardness of 10, so it can produce a scratch on the surface of say, Corundum Mohs value 9 but not the other way around.
...
18:51
Critical WooCommerce Payments Plugin Flaw Patched for 500,000+ WordPress Sites The Hacker News
Patches have been released for a critical security flaw impacting the WooCommerce Payments plugin for WordPress, which is installed on over 500,000 websites. The flaw, if left unresolved, could enable a bad actor to gain unauthorized admin access to impacted stores, the company said in an advisory on March 23, 2023. It impacts versions 4.8.0 through 5.6.1. Put differently, the issue could permit
18:35
Russian Coders Blocked From Contributing to FOSS Tools SoylentNews
Russian coders blocked from contributing to FOSS tools:
The Reg has seen two recent incidents of Russian developers being blocked from public development of FOSS code. One was a refusal on the Linux kernel mailing list, the other a more general block on Github. In the last week, these events have both caused active, and sometimes heated, discussions in FOSS developer communities.
The GitHub account of developer Alexander Amelkin has been blocked, and his repositories marked as "archived" including ipmitool, whose README describes it as "a utility for managing and configuring devices that support the Intelligent Platform Management Interface." Unable to comment on Github itself, Amelkin described what happened on the project's older Soureforge page:
Sorry to say, but on March 1st without any prior notice or any explanation whatsoever, GitHub has suspended my personal account and made orphan all the projects that I owned/maintained.
That includes ipmitool and frugen.
This mailing list and the old sourceforge project page are the only means of communication with you that I have left. I am currently searching for a way to unblock my GitHub or (less preferably) migrate ipmitool once again to another less hostile service.
Amelkin works for Russian chipbuilder Yadro, which we described as working on RISC-V chips back in 2021. Microsoft is just obeying US law in this: according to the War and Sanctions database of the Ukrainian National Agency on Corruption Prevention, the NACP, Yadro is a sanctioned company.
However, on LinkedIn, Amelkin disputes his employer's involvement:
You may rest assured that this "sanctioned corporation" takes no part in this awful war, and even if making civilian server products can be viewed as somehow taking part, that part is definitely far less than what, say, BMW or Bosch took in WW2, yet nobody seems to have cancelled them or at least remembered what they've done, let alone their individual employees. All this is stupid, xenophobic and racist. Especially you labelling me as a terrorist on the basis of my ethnicity.
18:22
The iPhone Moment of A.I. Has Started Lifeboat News: The Blog

The iPhone moment for A.I. hype takes many hues, but Nvidia is about the future of computing itself. NVIDIA DGX supercomputers, originally used as an AI research instrument, are now running 24/7 at businesses across the world to refine data and process AI.
While OpenAI gets a lot of the glory, I believe the credit should go to Nvidia. Launched late last year, ChatGPT went mainstream almost instantaneously, attracting over 100 million users, making it the fastest-growing application in history. We are at the iPhone moment of AI, Huang said. Nvidia makes about $6 to $7 Billion a fiscal quarter in revenue.
Nvidia said its offering a new set of cloud services that will allow businesses to create and use their own AI models based on their proprietary data and specific needs. The new services, called Nvidia AI Foundations, include three major components and are meant to accelerate enterprise adoption of generative AI: Enterprises can use Nvidia NeMo language service or Nvidia Picasso image, video and 3D service to gain access to foundation models that can generate text or images based on user inputs.
18:00
Synthetic proteins simplify nature to outperform the real thing Terra Forming Terra

Why Homesteading? A Candid Chat About the Homestead Tsunami | Joel Salatin of Polyface Farms Terra Forming Terra
Why Homesteading? A Candid Chat About the Homestead Tsunami
| Joel Salatin of Polyface Farms
https://www.youtube.com/watch?v=d52OcWJI6l0
<iframe width="512" height="384" src="https://www.youtube.com/embed/d52OcWJI6l0" title="Why Homesteading? A Candid Chat About the Homestead Tsunami | Joel Salatin of Polyface Farms" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" allowfullscreen></iframe>
What In The World Is Happening To The Sun? Terra Forming Terra
Consciousness Began When the Gods Stopped Speaking Terra Forming Terra

16:40
MITREs System of Trust risk model manager improves supply chain resiliency Help Net Security
MITRE launched its System of Trust risk model manager and established a community engagement group of 30 members. Expanding from its free and open platform, System of Trust now delivers a collaborative community to identify and mitigate threats to supply chainsbefore they happen. Leveraging the expertise of researchers and organizations, the community will further develop the frameworks body of knowledge and enhance supply chain security. System of Trust, showing key risk areas for suppliers, supplies/components, More
The post MITREs System of Trust risk model manager improves supply chain resiliency appeared first on Help Net Security.
16:30
New infosec products of the week: March 24, 2023 Help Net Security
Heres a look at the most interesting products from the past week, featuring releases from ForgeRock, Vectra, Verosint, Vumetric, and Waterfall Security Solutions. Waterfall Security Solutions launches WF-600 Unidirectional Security Gateway Waterfall Security Solutions launched the WF-600 Unidirectional Security Gateway, an OT security protection against remote cyber attacks. The WF-600 includes a self-contained, integrated software platform, with no external software needed on industrial or enterprise computers, and with the entire platform designed together with the More
The post New infosec products of the week: March 24, 2023 appeared first on Help Net Security.
16:22
The Iron Fist Unleashed! Lifeboat News: The Blog
Senescent cells accumulate with age when one senescent cell turns another cell senescent through SASP secretion. New research is offering new hope for fighting this.
16:22
BREAKING: Scientists create the 5th form of matter for 6 minutes Lifeboat News: The Blog
In a ground-breaking experiment, scientists have successfully created the fifth form of matter, known as the Bose-Einstein condensate (BEC), for a remarkable duration of six minutes.
This major accomplishment has the potential to revolutionize our understanding of quantum mechanics and open the door to new technological advancements. In this article, we will explore the significance of this achievement, the nature of BECs, and the potential applications of this newfound knowledge.
16:00
Enormous Metal Sculpture Becomes an Antenna Hackaday

Those who have worked with high voltage know well enough that anything can be a conductor at high enough voltages. Similarly, amateur radio operators will jump at any chance to turn a random object into an antenna. Flag poles, gutters, and even streams of water can be turned into radiating elements for a transmitter, but the members of this amateur radio club were thinking a little bit bigger when they hooked up their transmitter to this giant sculpture.
For those who havent been to the Rochester Institute of Technology (RIT) in upstate New York, the enormous metal behemoth is not a subtle piece of artwork and sits right at the entrance to the university. Its over 70 feet tall and made out of bronze and steel, a dream for any amateur radio operator. With the universitys permission and some help to ensure everyones safety during the operation, the group attached a feedline to the sculpture with a magnet, while the shield wire was attached to a ground rod nearby. A Yaesu FT-991 running on only 5 watts and transmitting in the 20-meter band was able to make contacts throughout much of the eastern United States with this setup.
This project actually started as an in-joke within the radio club, as reported by Reddit user [bbbbbthatsfivebees] who is a member. Eventually the joke becam...
16:00
Top ways attackers are targeting your endpoints Help Net Security
Over the last several years, endpoints have played a crucial role in cyberattacks. While there are several steps organizations can take to help mitigate endpoint threats such as knowing what devices are on a network (both on-premises and off-site), quarantining new or returning devices, scanning for threats and vulnerabilities, immediately applying critical patches, etc. there is still much to be done to ensure endpoint security. To achieve that, its important to understand some More
The post Top ways attackers are targeting your endpoints appeared first on Help Net Security.
15:51
Dinosaur Bone Study Reveals That Not All Giants Grew Alike SoylentNews
When the paleontologist Michael D'Emic cut into the bones of Majungasaurus, a relative of Tyrannosaurus rex that roamed Madagascar 70 million years ago, he suspected that surprises might be hiding in them. But what he found defied all expectations.
Majungasaurus adults measured up to 7 meters from snout to tail and could weigh 1,000 kilograms. Paleontologists had thought that big dinosaurs like these massive carnivores achieved their stature through rapid growth spurts. But the fossil bones revealed a different story. "Unlike carnivorous dinosaurs that had been studied up until then," D'Emic said, the Majungasaurus grew "really, really slowly."
Puzzled, he sliced up a close relative of the dinosaur a Ceratosaurus from North America, which was roughly the same length and weight to see if it grew slowly too. This time, "we got the opposite result," he said. "It grew just about faster than any carnivorous dinosaur I've ever seen."
What followed for D'Emic was a decade-long whirlwind of peering at bones for clues to how dinosaurs grew. His analysis of 42 different dinosaur species, recently published in Science, demonstrates that the "get big fast" mode of growth was less predominant than researchers have assumed.
[...] Whether an animal grows quicker and faster or slower and longer might seem like a nitpicky distinction. But an animal's growth trajectory provides insights into its life and the world it inhabited. Fast-growing animals can overpower potential predators and outcompete other species, but they need plenty of food and other resources. Growing slowly is riskier, but it allows an animal to survive on less during hard times. The bones of Majungasaurus, for example, confirm that, as the top predator in its ancient ecosystem, it had the luxury of developing at a leisurely pace.
Read more of this story at SoylentNews.
15:30
Why organizations shouldnt fold to cybercriminal requests Help Net Security
Organizations worldwide pay ransomware fees instead of implementing solutions to protect themselves. The ransom is just the tip of the iceberg regarding the damage a ransomware attack can wreak. In this Help Net Security video, Gerasim Hovhannisyan, CEO at EasyDMARC, discusses how domain authentication tools such as DKIM, SPF, and DMARC can help mitigate risk and limit the number of phishing attacks, identifying fraudulent messages before they even hit the receivers inbox and making organizations More
The post Why organizations shouldnt fold to cybercriminal requests appeared first on Help Net Security.
15:18
Seren Dalkiran joins our Futurists Board and our Sustainability Board. Lifeboat News
Seren Dalkiran joins our Futurists Board and our Sustainability Board. She is Founder of the Millennial Leadership Lab and Cofounder of the Synergized Earth Network.
15:12
TheGradCafe - 310,975 breached accounts Have I Been Pwned latest breaches
In February 2023, the grad school admissions search website TheGradCafe suffered a data breach that disclosed the personal records of 310k users. The data included email addresses, names and usernames, genders, geographic locations and passwords stored as bcrypt hashes. Some records also included physical address, phone number and date of birth. TheGradCafe did not respond to multiple attempts to disclose the breach.
15:00
In uncertain times, organizations prioritize tech skills development Help Net Security
Amid economic uncertainty and downturn, organizations are leaning on their technologists to continue to innovate and drive business value, according to Pluralsight. Though 65% of tech team leaders have been asked to cut costs, 72% still plan to increase their investment in tech skill development in 2023. And because upskilling existing talent is more cost-effective than hiring new employees, 97% of learning and development and HR directors say they are prioritizing internal talent over hiring More
The post In uncertain times, organizations prioritize tech skills development appeared first on Help Net Security.
15:00
OpenSUSE Tumbleweed Begins Rolling Out GCC 13 Phoronix
While GCC 13 is working its way toward its official GCC 13.1 stable release in the next few weeks, with this week's openSUSE Tumbleweed rolling-release updates it has already begun switching over to this major annual compiler update...
14:22
DNA Double Helix Splits Due to Invasive Nature of Unzipping Process Lifeboat News: The Blog
Scientists had a hard time reconstructing how complex molecular parts are being held together. However, that was before SISSAs Cristian Micheletti and his team studied how the DNA double helix unzips when translocated at high velocity through a nanopore.
DNA Double Helixs Unzipping
DNA has a double helix structure because it consists of two spiral chains of deoxyribonucleic acid. Its shape is reminiscent of a spiral staircase.
14:15
Zenoss improves security for user credentials with identity management capabilities Help Net Security
Zenoss has released advanced identity management capabilities, helping ensure maximum protection of sensitive credentials while in use and at rest throughout the Zenoss Cloud platform. This represents yet another key building block in the security and privacy features Zenoss has released since launching Zenoss Cloud in 2018. Credential-based attacks, one of the most common forms of cyberattack, occur when attackers compromise user credentials to bypass an organizations security measures and steal critical data. The number More
The post Zenoss improves security for user credentials with identity management capabilities appeared first on Help Net Security.
14:00
Vectra Match helps security teams accelerate threat hunting and investigation workflows Help Net Security
Vectra Match brings intrusion detection signature context to Vectra Network Detection and Response (NDR), enabling security teams to accelerate their evolution to AI-driven threat detection and response without sacrificing investments already made in signatures. As enterprises transform embracing digital identities, supply chains and ecosystems GRC and SOC teams are forced to keep pace. Keeping pace with existing, evolving and emerging cyber threats requires visibility, context and control for both known and unknown threats. The More
The post Vectra Match helps security teams accelerate threat hunting and investigation workflows appeared first on Help Net Security.
13:41
Links 23/03/2023: RSS Guard 4.3.3 and OpenBSD Webzine Techrights
![]()
Contents
-
GNU/Linux
-
Desktop/Laptop
-
Liliputing Kubuntu Focus Xe Gen 2 is a 14 inch Linux laptop with Intel Alder Lake-P for $895 and up
The Kubuntu Focus Xe Gen 2 is a thin and light notebook computer with a 14 inch full HD display, support for up to up to an Intel Core i7-1260P processor, up to 64GB of RAM, and PCIe 4 NVMe storage. It ships with the Kubuntu 22.04 LTS GNU/Linux distribution pre-installed.
An upgrade over the original Focus Xe, whic...
-
-
13:15
Experiencing 15 Years of LibrePlanet Celebration Firsthand as a Volunteer: 2023 Charting the Course Techrights
Article by Marcia K Wilbur
Welcome from LibrePlanet 2023!
This year, LibrePlanet was hybrid with on-site and online options from the Boston Convention and Exhibition Center.
It was a breezy and chilly weekend outside. The Boston St. Pattys day parade was scheduled around the corner for Sunday. What a great time to be in Boston!
Although I wanted to be there earlier, 9ish was time for me to come in from being out in the cold, for the 15-year celebration Free Software Foundations LibrePlanet.
Charting the Course was the theme. We were on board!
Event: Office party
My intention was to attend the office party early in the evening. However, I ended up on the wrong Franklin Street and was late. As I arrived, Craig was at the front and directed me to the refreshments and a contact, Illan, who would use me if there was a need.
Several people registered at the FSF offices for the conference starting the next day. The office party was a lot of mingling, talk about USENET, signal, privacy, makerspaces and much much more. The snacks were fresh and there was a variety of beverages including wine.
As the office party and evening came to a close, we were so entertained with lively conversation, we did not even realize the party was ending. I always recommend this party as a great meet and greet opportunity for free software enthusiasts. Again, this was a welcoming environment with no known issues. It was a great time!
Logistics and Venue
Parking was convenient and there was a driver with a cart to take you right to registration and the event!
The venue was comfortable and the event was welcoming!
Upon arrival at the convention center, a friendly security officer approached me, Are you here for the tech event?
YES!
He gave information about parking and the area. He mentioned the cart would be ready to take me up to the event. This was very pleasant.
The cart driver was very friendly and drove right up to registration.
There at registration, Craig greeted participants with a warm and welcoming smile. For this event, I was a volunteer at registration.
I was glad to be there.
Hallway Track
In between sessions and during lunch or just roaming around, we found ourselves in the hallway drinking coffee, discussing privacy, surveillance, Internet of things, AI/ML ethics, disaster recovery, and copyleft. Some discussions were about the state of healthcare, gaming and food!
The hallway track was a com...
13:08
This Tiny Chip is Being Used to Develop a Tooth-mounted Sensor That Can Read Your Spit SoylentNews
Miniaturizing tech is a perpetual challenge for wearable makers. The smaller the device, the better it is for wearability. The thing is, that usually comes at the expense of battery life. However, Silicon Labs is hoping its latest xG27 chipset is small and energy-efficient enough to spark some big ideas in the medical tech space like a saliva reader that's so tiny it can be mounted onto a tooth.
According to Silicon Labs, the xG27 family of SoCs consists of the BG27 and the MG27. Both are built around the ARM Cortex M33 processor, but the BG27 focuses on Bluetooth, while the MG27 supports Zigbee and other protocols. As for how small these chips are, the xG27 SoCs range from 2mm-squared to 5mm-squared roughly the width of a No. 2 pencil's lead tip to the width of the pencil itself. It's not the world's smallest Bluetooth chip, but Silicon Labs spokesperson Sam Ponedal tells The Verge that's only by "fractions of a millimeter."
This is neat from a technical perspective, but what's cooler is the BG27 is currently being used to develop an actual product the aforementioned tooth-mounted wearable sensor. Lura Health, a medical device maker, says it's using the chip for its "salivary diagnostic sensor." The sensor is small enough to be glued to a molar (or placed inside a "smart retainer") with the intent of continually monitoring a patient's saliva. That, in turn, would allow dentists and clinicians to potentially test for more than 1,000 health conditions.
[...] As for other use cases, Silicon Labs says its chips are good candidates for medical patches, continuous glucose monitors, and wearable EKGs. That's because they can operate on as low as 0.8 volts and can switch to a "shelf mode" that reduces energy use during transportation and while stored on shelves. These features aren't quite as appealing in consumer wearables, but it opens the door for greater wearable use in hospitals and clinical settings.
Read more of this story at SoylentNews.
13:00
Grow Your Own Brain Electrodes Hackaday

Bioelectronics has been making great strides in recent years, but interfacing rigid electrical components with biological systems that are anything but can prove tricky. Researchers at the Laboratory for Organic Electronics (LOE) have found a way to bridge the gap with conductive gels. (via Linkping University)
Outside the body, these gels are non-conductive, but when injected into a living animal, the combination of gel and the bodys metabolites creates a conductive ele...
12:48
[Meme] Grabinski the Opportunity Techrights
Opportunists from Germany, hijacking Europes legal system for patents under the auspices of EU
Summary: Reports of European Patents being invalidated (judges do not tolerate fake patents) have become so common that a kangaroo court becomes a matter of urgency for the EPOs Benot Battistelli and Antnio Campinos; will the EU and the EPOs Administrative Council go along with it, helping to cover up more than a decade of profound corruption?
12:33
MIT is testing light and sound to combat Alzheimers Lifeboat News: The Blog
Our brains arent limited to producing just one type of brain wave at a time, but usually, one type is dominant, and the type it is can often be linked to your level of alertness: delta waves may dominate when you sleep, while gamma waves might dominate when you concentrate intensely.
The idea: Researchers have previously observed that people with Alzheimers a devastating neurological disease affecting more than 6 million people in the US alone may have weaker and less in-sync gamma waves than people who dont have the disease.
In a series of past studies, MIT researchers demonstrated a deceptively simple way to increase the power and synchronization of these waves in mouse models of Alzheimers: expose the animals to lights flickering and/or sounds clicking at a frequency of 40 Hz.
12:32
Union Syndicale Fdrale Cautions the EPOs Administrative Council About Initiating an Illegal Kangaroo Court System for Patents (UPC) While EPO Breaks Laws and Sponsors the Ukraine Invasion Techrights
UPC is Unacceptable and a Risk to the EU (for many reasons)
Video download
link | md5sum
4742e57afe3feef00433b302d09ba6d1
USF Writes to AC and EU
Creative Commons Attribution-No Derivative Works 4.0
Summary: Union Syndicale Fdrale (USF) is once again speaking out in support of the staff union of Europes second-largest institution, which lacks oversight and governance because of profound corruption and regulatory capture
Repeating a pattern of offences, utter disregard for the law, and routine violations of the law (turning diplomatic immunity into unbridled impunity), the EPOs management incurs the wrath of NGOs; the same group that berated Benot Battistelli for his crimes is reporting Antnio Campinos to the people who can hold him accountable but never will (hes bribing them to be entirely complicit); this systemic breakdown or the collapse of the legal system (at least in the context of patents) merits far more media attention, but the media is connected to the same regimes and corporations that benefit financially from the corruption of the EPO.
![[USF] Union Syndicale Fdrale on SUEPO](http://techrights.org/wp-content/uploads/2023/03/suepo_125830.png) The video above goes through the
latest relevant letter, dated 3 days ago. It also takes stock of
this
latest nonsense (warning:
The video above goes through the
latest relevant letter, dated 3 days ago. It also takes stock of
this
latest nonsense (warning: epo.org link)
entitled Digital transformation & Unitary Patent: users
updated. As we noted already in Daily Links, the EPO had once
again promoted an illegal, unconstitutional ploy. The EPO is run by
gangsters who...
12:32
Organoids growing mini BRAINS Lifeboat News: The Blog

Organoids are an incredible tool for research into the brain.
Cerebral organoids are created by growing human stem cells in a
bioreactor. They might be the key to unlocking the answers to many
of our questions about the brain. We explain how theyre made and
some of the discoveries theyve helped with so far!
 Script
by Duranka Perera (https://www.durankaperera.com/)
Script
by Duranka Perera (https://www.durankaperera.com/)
 Thumb by
Broken Bran -
Thumb by
Broken Bran -
https://twitter.com/BranGSmith.
Support us on Patreon: https://www.patreon.com/Brainbook_
Thank you to our supporters:
Morag Forbes.
Patrick Kohl.
Ronald Coleman Dees.
Alex Rofini.
Helen Whitley.
Discover more on our website.
https://www.brainbookcharity.org.
Follow us on:
Twitter: https://www.twitter.com/realbrainbook.
Instagram: https://www.instagram.com/brainbook_
Facebook: https://www.facebook.com/realbrainbook
12:31
Do Kwon, Founder of Terraform Labs, Arrested in Montenegro HackRead | Latest Cybersecurity and Hacking News Site
Reportedly, Do Kwon was caught using falsified documents at an airport in the capital city of Montenegro.
This is a post from HackRead.com Read the original post: Do Kwon, Founder of Terraform Labs, Arrested in Montenegro
12:29
The Crazy Mass-Giving Mechanism of the Higgs Field Simplified Lifeboat News: The Blog
Get 30% off Blinkist premium and enjoy 2 memberships for the price of 1! Start your 7-day free trial by clicking here: https://www.blinkist.com/arvinash.
REFERENCES:
Where 99% of mass comes from: https://youtu.be/KnbrRhkJCRk.
ElectroWeak Unification: https://youtu.be/u05VK0pSc7I
Symmetry Breaking: https://youtu.be/yzqLHiA0uFI
PATREON:
For Input on Videos, Private messages, Early Viewing, Join Us:
https://www.patreon.com/arvinash.
CHAPTERS:
0:00 Sources of mass.
2:33 Blinkist Free Trial.
3:51 Particles are excitations in Fields.
6:09 How Mass comes from interaction with Higgs.
10:42 Why do some particles interact and others dont?
11:31 How our universe would not exist without Higgs.
SUMMARY:
How does the Higgs give mass to particles? How do elementary
particles gain mass? All mass is Energy. 99% of the mass of an atom
is contained in the binding energy within the nucleus. But about 1%
of your mass is contained in the mass of the subatomic particles
that make up the atoms, electrons and quarks.
How do these subatomic particles get an intrinsic mass? This is due to the Higgs Field. To understand how it works, lets look at the standard model of particle physics.
12:25
Microsoft Researchers Claim GPT-4 Is Showing Sparks of AGI Lifeboat News: The Blog
Fresh on the heels of GPT-4s public release, a team of Microsoft AI scientists published a research paper claiming the OpenAI language model which powers Microsofts now somewhat lobotomized Bing AI shows sparks of human-level intelligence, or artificial general intelligence (AGI).
Emphasis on the sparks. The researchers are careful in the paper to characterize GPT-4s prowess as only a first step towards a series of increasingly generally intelligent systems rather than fully-hatched, human-level AI. They also repeatedly highlighted the fact that this paper is based on an early version of GPT-4, which they studied while it was still in active development by wrangled into product-applicable formation.
Disclaimers aside, though, these are some serious claims to make. Though a lot of folks out there, even some within the AI industry, think of AGI as a pipe dream, others think that developing AGI will usher in the next era of humanitys future; the next-gen GPT-4 is the most powerful iteration of the OpenAI-built Large Language Model (LLM) to date, and on the theoretical list of potential AGI contenders, GPT-4 is somewhere around the top of the list, if not number one.
12:05
Investigation of Sirius Open Source Formalised schestowitz.com
Video download
link | md5sum
8e04ead83596e651305116cc77175bd0
Investigation Underway
Creative Commons Attribution-No Derivative Works 4.0
Summary: In light of new developments and some progress in an investigation of Sirius Open Source (for fraud!) we take stock of where things stand
IT hurts to know that a company which describes itself as Britains most respected Open Source company did this to us, but it did. Money laundering would be even worse, but were still looking into various allegations pertaining to privacy breaches, contract violations, and illegal contract-signing. To paraphrase the companys own boss, it doesnt look good
We recently learned some additional disturbing things. They will be published here at a later date. The video above focuses on what was published yesterday. Its one thing for an Open Source company to go out of business. To end up collapsing under a weight of abuse and even crime would hurt the image of Free software, including in the eyes of the British public sector (many of our clients were not private companies). This series wont end any time soon.
12:02
Investigation Underway: Sirius Open Source Embezzled/Stole Money, Robbed Its Own Staff Techrights
Video download
link | md5sum
8e04ead83596e651305116cc77175bd0
Investigation Underway
Creative Commons Attribution-No Derivative Works 4.0
Summary: In light of new developments and some progress in an investigation of Sirius Open Source (for fraud!) we take stock of where things stand
IT hurts to know that a company which describes itself as Britains most respected Open Source company did this to us, but it did. Money laundering would be even worse, but were still looking into various allegations pertaining to privacy breaches, contract violations, and illegal contract-signing. To paraphrase the companys own boss, it doesnt look good
This series wont end any time soon.We recently learned some additional disturbing things. They will be published here at a later date. The video above focuses on what was published yesterday. Its one thing for an Open Source company to go out of business. To end up collapsing under a weight of abuse and even crime would hurt the image of Free software, including in the eyes of the British public sector (many of our clients were not private companies). This series wont end any time soon.
11:45
BlackBerry partners with Adobe to deliver secure forms with electronic signatures on mobile Help Net Security
BlackBerry and Adobe have partnered to deliver a secure forms solution for mobile. The software solution, which combines BlackBerry UEM and Adobe Experience Manager Forms, is designed for popular mobile device platforms, and meets the rigorous security standards required by regulated industries. Furthermore, the partnership agreement allows BlackBerry to resell Adobe Experience Manager Forms software. Prior to the partnership between BlackBerry and Adobe, users have been challenged in completing and approving documents away from their More
The post BlackBerry partners with Adobe to deliver secure forms with electronic signatures on mobile appeared first on Help Net Security.
11:07
Report: Global Patent Renewal TrendsUnpicking What Survives IEEE Spectrum

We are delighted to share a new research report that explores trends in patent maintenance behaviors revealed through the analysis of two decades of patent data.
By collecting and analyzing different data points, we explore the trends and directionality of patent filing and maintenance by jurisdiction and sector to understand what survives. The insights within the report create a clearer profile of patent maintenance behaviors, affording readers a unique perspective on the renewals landscape and the strategic value of annuities.
11:00
HPR3820: Introduction to Gaming Hacker Public Radio
This starts out the series on Computer Strategy Games, and we begin with the game that got me hooked, the first Civilization game created by Sid Meier and published by Microprose. Though it is pretty old now, it is still fond in my heart, and in the hearts of so many other gamers. If this comes across as a love letter, so be it. We will also in this series look at where you can obtain old games, and where you can find more information about the games I cover. Links: https://en.wikipedia.org/wiki/Civilization_(series) https://en.wikipedia.org/wiki/4X http://flashofsteel.com/index.php/2006/09/18/gamers-bookshelf-civilization-or-rome-on-640k-a-day/ https://www.amazon.com/Sid-Meiers-Civilization-Chronicles-PC/dp/B000IU1PQA https://playclassic.games/ https://www.myabandonware.com/ https://www.myabandonware.com/game/sid-meier-s-civilization-1nj https://www.civfanatics.com/civ1/manual/civ1_man.htm https://www.civfanatics.com/civ1/cia/ https://forums.civfanatics.com/media/categories/civilization-gallery.16/ https://www.youtube.com/watch?v=CkmHeepmjEc https://www.youtube.com/watch?v=VF8Ribe5AFU https://www.youtube.com/watch?v=L7GkX4h-TP8 https://www.youtube.com/watch?v=3UuXa3PRSGo https://www.youtube.com/watch?v=Q1d08T8_wI4 https://www.youtube.com/watch?v=AJ-auWfJTts https://www.amazon.com/Sid-Meiers-Memoir-Computer-Games/dp/B08MNG8VX8/ https://www.palain.com/gaming/sid-meiers-civilization/
Supporting Developers with Disabilities It Will Never Work in Theory
If you don't ask people what they actually need or whether your supposedly good idea actually worked, it's all too easy for your "help" to accomplish nothing or even make things worse. That's why "Nothing about us, without us" became a rallying cry for disabled activists in the 1990s, and why it's vital to critically evaluate programs intended to help people with disabilities. This new paper looks at an effort by a Brazilian company to hire and train disabled software developers. None of the findings are particularly surprising, but that's part of why studies like this one are needed: if we never ask the question, we'll never know what we missed.
The paper closes with four recommendations that will make everyone's teaching better:
- Help instructors to master accessibility teaching practices.
- Make the materials available and organized in advance.
- Curate accessible programming tools.
- Make birds of a feather flock together (i.e., have someone from the community on the instructional team).
Isadora Cardoso-Pereira, Geraldo Gomes, Danilo Monteiro Ribeiro, Alberto de Souza, Danilo Lucena, and Gustavo Pinto. Supporting the careers of developers with disabilities: lessons from Zup Innovation. 2023. arXiv:2303.05429.
Software developers with disabilities have a hard time to join the software development market. Due to the lack of diversity that developers with disabilities could hinder innovation. In this work, we explore the Catalisa program envisioned by Zup Innovation, a Brazilian tech company, aimed to hire and train software developers with disabilities. We found that the program was able to accelerate the participants careers, although some shortcomings are still present.
10:23
Use of Meta Tracking Tools Found to Breach EU Rules on Data Transfers SoylentNews
Use of Meta tracking tools found to breach EU rules on data transfers:
Austria's data protection authority has found that use of Meta's tracking technologies violated EU data protection law as personal data was transferred to the US where the information was at risk from government surveillance.
The finding flows from a swathe of complaints filed by European privacy rights group noyb, back in August 2020, which also targeted websites' use of Google Analytics over the same data export issue. A number of EU DPAs have since found use of Google Analytics to be unlawful and some (such as France's CNIL) have issued warnings against use of the analytics tool without additional safeguards. But this is the first finding that Facebook tracking tech breached the EU's General Data Protection Regulation (GDPR).
All the decisions follow a July 2020 ruling by the European Union's top court that struck down the high level EU-US Privacy Shield data transfer agreement after judges once again identified a fatal clash between US surveillance laws and EU privacy rights. (A similar finding, back in 2015, invalidated Privacy Shield's predecessor: Safe Harbor.)
noyb ['none of your business' * see below. --Ed] trumpets the latest data transfer breach finding by an EU DPA as "groundbreaking" arguing that the Austrian authority's decision should send a signal to other sites that it's not advisable to use Meta trackers (the complaint concerns Facebook Login and the Meta pixel).
[...] "Facebook has pretended that its commercial customers can continue to use its technology, despite two Court of Justice judgments saying the opposite. Now the first regulator told a customer that the use of Facebook tracking technology is illegal," said Max Schrems, chair of noyb.eu, in a statement.
Read more of this story at SoylentNews.
10:00
Ondol: Korean Underfloor Heating Hackaday

One of the many aspects of the modern world we often take for granted is the very technology that keeps our accommodation at a habitable temperature. Examples of this include centralized heating systems using hot-water circulation, or blown air ducted to multiple rooms from a central furnace. Certainly in Europe, once the Romans shipped out, and before the industrial revolution, we were pretty cold unless someone lit a fire in the room. Every room. But not in Korea. The Ondol heating principles have been used constantly from about 5000 BC to only a few decades ago, keeping your average Korean countryman nice and toasty.
Having said that, the sophistication has improved a bit. Initially, the idea was to simply heat up a bunch of rocks in the fire, and bring them indoors, but Ondol quickly became part of the building itself. As will be seen from the video embedded below, the house sits on top of an elaborate double stack of serpentine channels, that circulate the hot combustion products from the furnace as thoroughly as possible, slowing down the gases and allowing their heat to transfer into the structure of the floor, and then radiate into the space...
09:43
09:14
A million at risk from user data leak at Korean beauty platform PowderRoom Security Affairs
South Korean beauty content platform, PowderRoom, has leaked the personal information of nearly one million people.
- Established in 2003, PowderRoom is a South Korean beauty content platform connecting 3.5 million members and thousands of beauty brands
- It calls itself the first and the biggest beauty community in South Korea that allows you to experience new brand products faster than anyone else and share the experience
- It exposed up to a million users full names, phone numbers, emails, Instagram usernames and home addresses
- The database was publicly available for over a year
- Attackers could have exploited the data to launch phishing and device hijacking attacks, make unauthorized purchases, and stalk users
- Cybernews reached out to PowderRoom and the Korean National Computer Emergency Response Team, and the data was secured
The Cybernews research team discovered that the South Korean social platform, powderroom.co.kr which markets itself as the nations biggest beauty community was leaking the private data of a million users.
The platform exposed full names, phone numbers, emails, Instagram usernames, and even home addresses. Researchers estimate that the database was publicly available for over a year.
Backed by beauty-product manufacturers, PowderRoom has hundreds of thousands of followers on social media, and its Android app has been downloaded more than 100,000 times on Google Play.
On the platform, users can review beauty products while being encouraged to actively participate and receive perks.
Personal data leaked
On December 15, researchers found a publicly accessible database with nearly 140GB of data. Some server logs included entries containing personal information, such as names, phone numbers, and home addresses, along with metadata about user devices and browsers used to access the site. The dataset included over a million email addresses.
Among the leaked data, researchers found a million tokens used for authentication and accessing the website.
Abusing them, threat actors could hijack user accounts and purchase products on the platform using the payment methods linked with the account. Additionally, attackers could modify account details, and post comments and reviews.
Leaking home addresses and phone numbers is a cause of concern, since exposing such information might lead to in-person stalking or harassment of the users of the platform.
If you want to know how to protect yourself, give a look at the original post at: https://cybernews.com/security/powder-room-data-leak/
About the author:...
08:22
Cloudstream Takes Site and Code Offline in Response to Hollywood Complaint TorrentFreak
 Legal video streaming services such as Amazon, Disney, and
Netflix are booming. At the same time, theres a flourishing dark
market of pirate streaming tools.
Legal video streaming services such as Amazon, Disney, and
Netflix are booming. At the same time, theres a flourishing dark
market of pirate streaming tools.
These unauthorized alternatives increasingly use slick designs and easy-to-use apps to appeal to a broad audience. And unlike the legal options, they offer all popular titles under the same roof, without charging a penny.
Cloudstream is one of the apps that made its mark in recent years. The Android-based software can aggregate pirated content from several third-party sources and is fully customizable through open-source extensions.
This hasnt gone unnoticed by rightsholders. Sky UK targeted the software last year and across the pond, Cloudstream also appeared on the radar of the MPA, Hollywoods anti-piracy group.
MPA Targets Cloudstream
This week, the MPA decided to take action. The organization, which represents the major Hollywood studios and Netflix, sent a DMCA notice to GitHub, asking the developer platform to remove several Cloustream-related files.
We [] request your assistance in addressing, the extensive copyright infringement of motion pictures and television shows that is occurring by virtue of the operation of the domain cloudstream.cf, which is hosted on and available for download from your repository GitHub Inc.
Specifically, at the URL, the Repository hosts and offers for download the APK CloudStream, which in turn is used to engage in massive infringement of copyrighted motion pictures and television shows, the notice adds.
When GitHub receives DMCA notices it typically informs developers of the targeted content, allowing them to address the problem on their own. That also happened in this instance and led to a drastic decision.
Cloudstream Takes Voluntary Action
Yesterday, Cloudstream developer Lag informed the apps Discord followers that they had received a very serious DMCA notice that simply cant be ignored. For t...
08:02
Experts published PoC exploit code for Veeam Backup & Replication bug Security Affairs
Researchers released a PoC exploit code for a high-severity vulnerability in Veeam Backup & Replication (VBR) software.
Veeam recently addressed a high-severity flaw, tracked as CVE-2023-27532, in Veeam Backup and Replication (VBR) software. An unauthenticated user with access to the Veeam backup service (TCP 9401 by default) can exploit the flaw to request cleartext credentials.
A remote attacker can exploit the flaw to access the backup systems of a target organization and execute arbitrary code as SYSTEM.
Vulnerability CVE-2023-27532 in a Veeam Backup & Replication component allows an unauthenticated user operating within the backup infrastructure network perimeter to obtain encrypted credentials stored in the configuration database. reads the advisory published by the vendor. This may lead to an attacker gaining access to the backup infrastructure hosts.
The company addressed the flaw with the release of Veeam Backup & Replication build numbers:
The researchers at Horizon3s Attack Team published technical details for this vulnerability along with a PoC exploit code.
The researchers performed reverse engineering of Veeams Backup Service, they focused on the port used by the Veeam backup service.
The researchers discovered that is possible to abuse an unsecured API endpoint to retrieve credentials in plaintext from the VBR configuration database.
We have examined the vuln...
07:38
Microsoft Begs You Not to Ditch Edge on Google's Own Chrome Download Page SoylentNews
Monopoly giant can't stand it when anyone else has a monopoly:
Microsoft Edge has been spotted inserting a banner into the Chrome download page on Google.com begging people to stick with the Windows giant's browser.
As noted this week by Neowin, an attempt to download and install Chrome Canary using Edge Canary both experimental browser builds led to the presentation in the Edge browser window of a banner graphic celebrating the merits of Edge.
"Microsoft Edge runs on the same technology as Chrome, with the added trust of Microsoft," the banner proclaims atop a button labeled "Browse securely now."
This was on a Google web page, google.com/chrome/canary/thank-you.html, and it's not clear how this ad surfaced. Edge appears to display the banner by itself when the user surfs to the Chrome download page on Google.com, which is just a little bit aggressive.
[...] An individual familiar with browser development confirmed to The Register that he could reproduce the ad, which was said to be written in HTML but wasn't placed "in" the page. He described the ad as its own browser window that, surprisingly, was viewable with Edge's "Inspect" option for viewing source code.
Our source speculated the ad was implemented in a way that pushes down the "Content area" the space where loaded web pages get rendered to make space for a second rendering area that holds the ad.
[...] Among those who concern themselves with the nuances of browser behavior, it's argued that blurring the boundaries between what the browser presents and what the website presents is both confusing and a potential security risk.
Read more of this story at SoylentNews.
07:31
Fake ChatGPT Extension Hijacks Facebook Accounts HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
At the time of reporting this scam to Google, the fake ChatGPT extension had over 7,000 installations.
This is a post from HackRead.com Read the original post: Fake ChatGPT Extension Hijacks Facebook Accounts
07:00
ISA over TPM to Your PC Hackaday

Sometimes you really want to use your legacy SoundBlaster instead of emulating it for classic games. While modern PCs dont have ISA slots, [TheRasteri] is fixing this shortcoming with his dISAppointment board. (via Adafruit)
ISA was the standard card bus for PCs during the golden age of DOS gaming, and many of these games will still run on modern x86 hardware. Unfortunately, they run into hiccups with regards to sound since they were designed to specifically support ISA-based sound cards. [TheRasteri] found he could access the ISA bus lurking in modern computers through the Low Pin Count (LPC) bus which is exposed on the...
07:00
Open source changes everything: What John Walicki learned about community building Linux.com

Read the original blog here Read More
The post Open source changes everything: What John Walicki learned about community building appeared first on Linux.com.
06:30
AMD's HIPRT Working Its Way To Blender With ~25% Faster Rendering Phoronix
While not part of the upcoming Blender 3.5 release, AMD engineers are working to land their HIP ray-tracing (HIPRT) support within the Blender open-source 3D modeling software that will offer nice rendering speed-ups for AMD RDNA2/RDNA3 GPUs...
06:08
Not Quite What Happened Not Even Wrong
Quanta has an article out today about the wormhole publicity stunt, which sticks to the story that by doing a simple SYK model calculation on a quantum computer instead of a classical computer, one is doing quantum gravity in the lab, producing a traversable wormhole and sending information through it. From what Ive heard, the consensus among theorists is that the earlier Quanta article and video were nonsense, outrageously overhyping a simulation and then bizarrely identifying a simulation with reality if its done on a quantum computer.
The new article is just about as hype-laden, starting off with:
A holographic wormhole would scramble information in one place and reassemble it in another. The process is not unlike watching a butterfly being torn apart by a hurricane in Houston, only to see an identical butterfly pop out of a typhoon in Tokyo.
and
In January 2022, a small team of physicists watched breathlessly as data streamed out of Googles quantum computer, Sycamore. A sharp peak indicated that their experiment had succeeded. They had mixed one unit of quantum information into what amounted to a wispy cloud of particles and watched it emerge from a linked cloud. It was like seeing an egg scramble itself in one bowl and unscramble itself in another.
In several key ways, the event closely resembled a familiar movie scenario: a spacecraft enters one black hole apparently going to its doom only to pop out of another black hole somewhere else entirely. Wormholes, as these theoretical pathways are called, are a quintessentially gravitational phenomenon. There were theoretical reasons to believe that the qubit had traveled through a quantum system behaving exactly like a wormhole a so-called holographic wormhole and thats what the researchers concluded.
An embarrassing development provides the ostensible reason for the new article, the news that another group suggests thats not quite what happened. This refers to this preprint, which argues that the way the Jafferis-Lykken-Spiropulu group dramatically simplified the calculation to make it doable on a quantum computer threw out the baby with the bathwater, so was not meaningful. The new Quanta piece has no quotes from experts about the details of whats at issue. All one finds is the news that the preprint has been submitted to Nature and that
the Jafferis, Lykken and Spiropulu group will likely have a chance to respond.
Theres also an odd piece of identity-free and detail-free reporting that
five independent experts familiar with holography consulted for this article agreed that the...
05:58
05:48
[CVE-2023-28686] Insufficient message sender validation in Dino Open Source Security
Posted by Dino Team on Mar 23
### Affected softwareDino (Instant Messenger) - https://dino.im/
### Severity
Medium (5.3): AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:L/A:N
### Affected versions
### Fixed versions
###...
05:33
ChatGPT Now Hooks with Wolfram Alpha cryptogon.com
Via: Stephen Wolfram: Under the hood, ChatGPT is formulating a query for Wolfram|Alphathen sending it to Wolfram|Alpha for computation, and then deciding what to say based on reading the results it got back.
05:18
Cisco fixed multiple severe vulnerabilities in its IOS and IOS XE software Security Affairs
Cisco addressed tens of vulnerabilities in its IOS and IOS XE software, six of these issues have been rated high severity.
Cisco published the March 2023 Semiannual IOS and IOS XE Software Security Advisory that addresses several vulnerabilities in IOS and IOS XE software.
Below is the list of flaws addressed by the IT giant in this bundled publication:
05:14
[Meme] Sirius Open Source Pensions: Schemes or Scams? Giving a Bad Name to Open Source Techrights
Such behaviour stains the brand Open Source
Summary: What Sirius Open Source did to its staff is rightly treated as a criminal matter; we know who the perpetrators are
05:10
This Is the Birth of a Different Age cryptogon.com
This is about AI and Chinese psyop platform TikTok. Via: Fox:
05:02
Holding Fake Open Source Accountable for Fraud schestowitz.com
Summary: 2 pension providers are looking into Sirius Open Source, a company that defrauded its own staff; stay tuned as theres lots more to come. Is this good representation for Open Source? From a company that had many high-profile clients in the public sector?
THIS is taking a much longer time than initially estimated, but it has certainly progressed. The process is moving on. Its typically like this when dealing with authorities. YMMV.
It is a very sad thing that regulatory agencies and even police are politicised to the point where one needs high-level (personal) connections, business links, bribes etc. in order to get things moving and for criminals to be actually held accountable, even prosecuted. Very sad. It should not be like this. In a functioning democratic society theres no room for yes, well, they committed a crime, but its not our problem and investigating this is expensive to us
Anyway, the good news, in this particular case, is that not one but two pension providers are on the case. 2 pension providers that know Sirius. They wrote about and opened formal investigations (this week).
Were pleased with this progress.
In additional to the letter above, which arrived 2 days ago (it is redacted sufficiently), Ive also spoken to the manager of another pension provider (probably the third manager Ive spoken to; some of them I spoke to 3 or 4 times over the telephone). Here is what he said some days ago:
NOW Pensions Employer Issues
Hi Roy,
Thank you for your call today, apologies for the bad communication and service you have had from us regarding you concerns with your employer Sirius Corporation.
As discussed,.
I will arrange for a letter to be sent to you and or email with assurances that your pension money is safe with Now Pensions
I will alert the team that deals with your employer that the CEO is wanted for embezzlement and that he effectively scammed all his employers previously
through a pensi...
05:00
Millimeter Wave Radar System Keeps Drivers Safe on the Road IEEE Spectrum

A new sensor could help reduce the number of accidents caused by impaired driving and could protect children left in hot cars. The Wireless Intelligent Sensing millimeter-wave radar system, developed by startup Pontosense, monitors vehicle occupants vital signs, and it can detect the presence of passengers in the vehicle and where they are seated.
The WISe system measures the drivers vital signs including heart rate and breathing to detect fatigue and possible medical emergencies. WISe sends out signals with wavelengths short enough to measure the tiny adjustments in a persons body from breathing and pulse. The signal echo is then analyzed by an artificial intelligence (AI) algorithm.
There is an urgent need for this kind of technology, says cofounder Alex S. Qi, the startups CEO. A recent study on the causes of motor vehicle accidents found that fatigue and medical emergencies were the top reasons.
WISe is the first in-market millimeter-wave wireless sensor used for that purpose in the automotive industry, Qi says. The system is expected to be installed in several vehicle models in the near future, he says.
Monitoring drivers to make roads safer
Current in-car driver-monitoring systems require either cameras or contact sensors, but WISe works wirelessly. The system uses RF sensing to capture echos of the micromovements made by the drivers or passengers body caused by heartbeats and breaths. WISe detects changes in the reflected signals phasethe relationship between radio signals that share the same space and frequencyto read the micromovements and vital signs.
Think of the sensor as bouncing waves off of something, like how whales and bats use sonar and echolocation to gauge where objects are located around them. Thats the basis of our technology, Qi says.
About Pontosense
FOUNDED
2021
HEADQUARTERS
Toronto
EMPLOYEES
120
The sensor transmits millimeter waves from an antenna designed by cofounder and CTO Yihong Qi (Alex and Yihong are related). When the waves are reflected back to the sensor, the received echo allows WISe to see the small movements and gather data about the persons health status.
The system checks heart ra...
04:59
Sirius Open Source Under Investigation for Pension Fraud, Several Pension Providers Examine the Facts Techrights
Summary: 2 pension providers are looking into Sirius Open Source, a company that defrauded its own staff; stay tuned as theres lots more to come. Is this good representation for Open Source? From a company that had many high-profile clients in the public sector?
THIS is taking a much longer time than initially estimated, but it has certainly progressed. The process is moving on. Its typically like this when dealing with authorities. YMMV.
It is a very sad thing that regulatory agencies and even police are politicised to the point where one needs high-level (personal) connections, business links, bribes etc. in order to get things moving and for criminals to be actually held accountable, even prosecuted. Very sad. It should not be like this. In a functioning democratic society theres no room for yes, well, they committed a crime, but its not our problem and investigating this is expensive to us
Anyway, the good news, in this particular case, is that not one but two pension providers are on the case. 2 pension providers that know Sirius. They wrote about and opened formal investigations (this week).
Were pleased with this progress and here is some background:
04:52
Danger USB! Journalists sent exploding flash drives Graham Cluley
If you were sent a USB stick anonymously through the post, would you plug it into your computer? Perhaps you'll think twice when you hear what happened to these Ecuadorian journalists. Read more in my article on the Hot for Security blog.
04:52
Exposure to Perfluoroalkyl Substances and Women's Fertility Outcome SoylentNews
Exposure to Perfluoroalkyl Substances and Women's Fertility Outcome:
Hundreds of everyday products are made with highly toxic fluorinated chemicals called PFAS. They build up in our bodies and never break down in the environment. Very small doses of PFAS have been linked to cancer, reproductive and immune system harm, and other diseases.
For decades, chemical companies covered up evidence of PFAS' health hazards. Today nearly all Americans, including newborn babies, have PFAS in their blood, and more than 200 million people may be drinking PFAS-tainted water. What began as a "miracle of modern chemistry" is now a national crisis.
In 1946, DuPont introduced nonstick cookware coated with Teflon. Today the family of fluorinated chemicals that sprang from Teflon includes thousands of nonstick, stain-repellent and waterproof compounds called PFAS, short for per- and poly-fluoroalkyl substances.
PFAS are used in a staggering array of consumer products and commercial applications. Decades of heavy use have resulted in contamination of water, soil and the blood of people and animals in the farthest corners of the world. PFAS are incredibly persistent, never breaking down in the environment and remaining in our bodies for years.
DuPont invented the PFAS chemical patented as Teflon, but 3M became its main manufacturer. In 2001, a scandal erupted in Parkersburg, W.Va., after discovery of the Teflon chemical in the drinking water of tens of thousands of people near a DuPont plant. (The story is documented in the film "The Devil We Know.")
A class-action lawsuit uncovered evidence DuPont knew PFAS was hazardous and had contaminated tap water but didn't tell its workers, local communities or environmental officials. The lawsuit also triggered studies linking the Teflon chemical to cancer and other diseases.
Read more of this story at SoylentNews.
04:41
Leader of U.S. Militarys Africa Command States Our Government Shares Core Values with Military Coup Leaders cryptogon.com
Via: Rep. Matt Gaetz: BREAKING: The leader of U.S. militarys Africa Command states our government shares core values with military coup leaders. These SAME coup leaders were trained by our own Armed Forces! pic.twitter.com/boGYfQ6csb Rep. Matt Gaetz (@RepMattGaetz) March 23, 2023
04:21
The FBI Used an Undercover Cop With Pink Hair to Spy on Activists and Manufacture Crimes cryptogon.com
Via: The Intercept: But Chelsies identity was as fake as her long pink hair. The young woman, whose real name is April Rogers, is a detective at the Colorado Springs Police Department. The FBI enlisted her to infiltrate and spy on racial justice groups during the summer of 2020. Once Rogers gained trust among []
04:10
Australia: Soldiers Control Robot with Brain Computer Interface cryptogon.com
Via: Science Daily: Researchers from the University of Technology Sydney (UTS) have developed biosensor technology that will allow you to operate devices, such as robots and machines, solely through thought control. The advanced brain-computer interface was developed by Distinguished Professor Chin-Teng Lin and Professor Francesca Iacopi, from the UTS Faculty of Engineering and IT, in []
04:00
Orange Pi 5 Is A Great & Very Fast Alternative To The Raspberry Pi 4 Phoronix
With an 8-core Rockchip RK3588S SoC, the Orange Pi 5 is leaps and bounds faster than the aging Raspberry Pi 4. With up to 32GB of RAM, the Orange Pi 5 is also capable of serving for a more diverse user-base and even has enough potential for assembling a budget Arm Linux developer desktop. I've been testing out the Orange Pi 5 the past few weeks and it's quite fast and nice for its low price point.
04:00
Framework Laptop Launches AMD Ryzen Upgradeable Laptop, Intel Raptor Lake Models Too Phoronix
The Framework Laptop as a modular and upgradeable laptop has garnered much interest from the open-source community and PC enthusiasts the past few years. Until today though the upgradeable laptops have just been Intel Core powered while today the company had some big announcements...
03:56
Scientists Find Plastic Rocks on Remote Island cryptogon.com
Via: AFP: There are few places on Earth as isolated as Trindade island, a volcanic outcrop a three- to four-day boat trip off the coast of Brazil. So geologist Fernanda Avelar Santos was startled to find an unsettling sign of human impact on the otherwise untouched landscape: rocks formed from the glut of plastic pollution []
03:41
Europes transport sector terrorised by ransomware, data theft, and denial-of-service attacks Graham Cluley
A new report from ENISA, the European Union Agency for Cybersecurity, looking at cyberattacks targeting the European transport network over a period of almost two years, has identified that ransomware has become the prominent threat. Read more in my article on the Tripwire State of Security blog.
03:29
Fake ChatGPT Chrome Browser Extension Caught Hijacking Facebook Accounts The Hacker News
Google has stepped in to remove a bogus Chrome browser extension from the official Web Store that masqueraded as OpenAI's ChatGPT service to harvest Facebook session cookies and hijack the accounts. The "ChatGPT For Google" extension, a trojanized version of a legitimate open source browser add-on, attracted over 9,000 installations since March 14, 2023, prior to its removal. It was originally
03:28
Links 23/03/2023: Sparky 2023.03 Special Editions and SUSE Changes CEO (Dirk-Peter van Leeuwen) Techrights
![]()
Contents
- GNU/Linux
- Desktop Environments/WMs
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Leftovers
- Science
- Education
- Hardware
- Health/Nutrition/Agriculture
- Proprietary
- Security
- Defence/Aggression
- Transparency/Investigative Reporting
- Environment
- Finance
- AstroTurf/Lobbying/Politics
- Censorship/Free Speech
- Freedom of Information / Freedom of the Press
- Civil Rights/Policing
- Internet Policy/Net Neutrality
- Monopolies
- Gemini* and Gopher
03:01
How to back up and restore Red Hat Ansible Automation Platform Linux.com
Back up your AAP environment to restore it to your current environment or a new one.
Read More at Enable Sysadmin
The post How to back up and restore Red Hat Ansible Automation Platform appeared first on Linux.com.
02:54
Linux Foundation Newsletter: March 2023 Linux.com

Read the original blog at The Linux Foundation
The post Linux Foundation Newsletter: March 2023 appeared first on Linux.com.
02:43
Distribution Release: Ubuntu 20.04.6 DistroWatch.com: News
Graham Inggs has announced the availability of a point release update to Ubuntu 20.04.6. The new media offers bug fixes and addresses some Secure Boot issues. The release announcement shares the following details: "The Ubuntu team is pleased to announce the release of Ubuntu 20.04.6 LTS (Long-Term Support)....
02:33
Fake GPT Chrome extension steals Facebook session cookies, breaks into accounts Graham Cluley
The world has gone ChatGPT bonkers. Which makes it an effective lure for cybercriminals who may want to break into accounts...
02:24
[$] Free software during wartime LWN.net
Just over 27 years ago, John Perry Barlow's declaration of the
independence of Cyberspace claimed that governments "have no
sovereignty
" over the networked world. In 2023, we have ample
reason to know better than that, but we still expect the
free-software community to be left alone by the affairs of
governments much of the time. A couple of recent episodes related
to the war in Ukraine are making it clear that there are limits to
our independence.
02:23
OpenBGPD 7.9 released OpenBSD Journal
Version 7.9 of OpenBGPD has been released:
We have released OpenBGPD 7.9, which will be arriving in the
OpenBGPD directory of your local OpenBSD mirror soon.
This release includes the following changes to the previous release:
* Include OpenBSD 7.2 errata 023:
Incorrect length checks allow an out-of-bounds read in bgpd(8).
02:03
Feds Arrest Alleged BreachForums Owner and the Forum Closes - for Now SoylentNews
Feds Arrest Alleged BreachForums Owner Linked to FBI Hacks
Feds arrest alleged BreachForums owner linked to FBI hacks:
The FBI has arrested the person allegedly in charge of the BreachForums online hacking community, as reported earlier by Krebs on Security and Bleeping Computer. Conor Brian Fitzpatrick, also known online as "Pompompurin," was arrested at his New York home on Wednesday and charged with conspiracy to commit access device fraud, according to a pair of court filings.
In a sworn statement, the FBI agent involved in the case claims Fitzpatrick admitted to owning BreachForums at the time of his arrest and identified himself as Pompompurin. Pompompurin created BreachForums after the FBI seized RaidForums, a similar hacking site that also sold leaked information.
The hacker is implicated in a number of breaches, with many of them targeting the FBI. In 2021, Pompompurin took responsibility for a hack that sent out thousands of fake cybersecurity warnings from the FBI's email address, and is also linked to the breach of Infragard, the FBI's information-sharing program that aims to raise awareness about physical and digital threats to government organizations and independent companies.
The hacking forum was recently involved in the breach of DC Health Link
Additionally, Bleeping Computer notes that Pompompurin is connected to the 2021 Robinhood breach that exposed the information of millions of its users, as well as the leak of Twitter user handles and email addresses that occurred in November 2022.
...
02:00
Upcycling a Tandy Model 100, Part II: I2C Strikes Back IEEE Spectrum
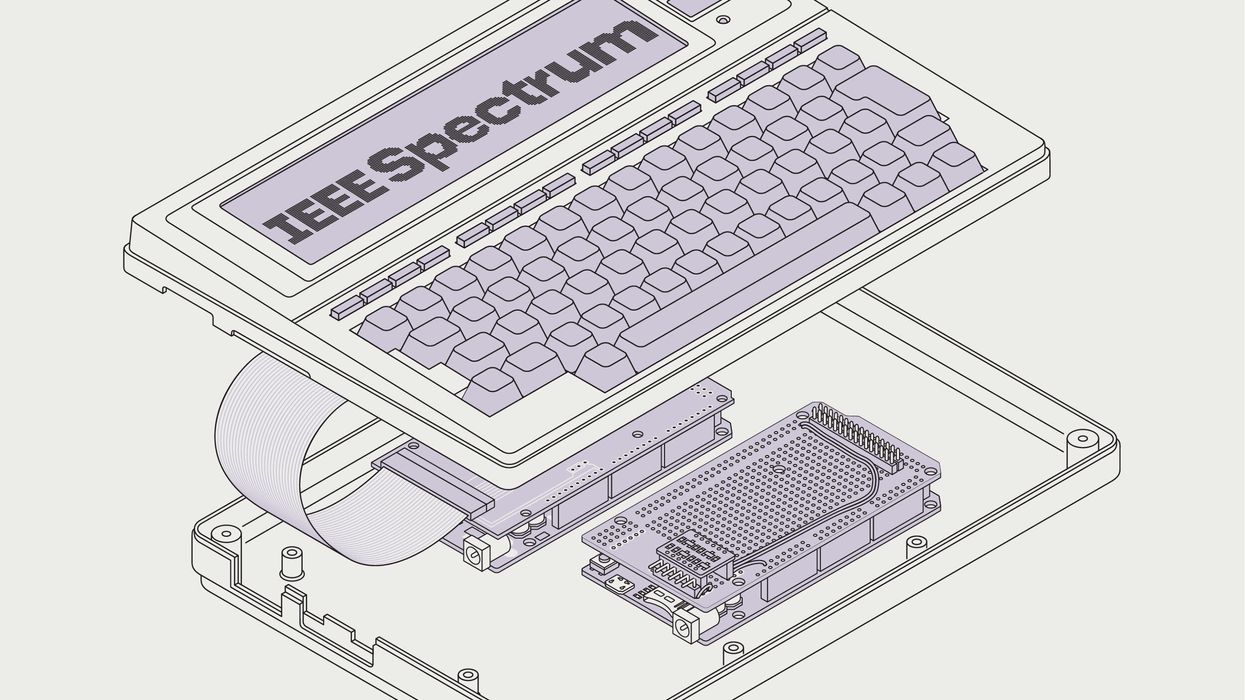
Last year for Hands On, I gutted a defunct TRS-80 Model 100. The goal was to upgrade its 24 kilobytes of RAM and 2.4-megahertz, 8-bit CPU but keep the notebook computers lovely keyboard and LCD screen. That article was almost entirely about figuring out how to drive its squirrely 1980s-era LCD screen. I left the rest, as they say, as an exercise for the reader. After all, sending a stream of data from a new CPU to the Arduino Mega controlling the screen would be a trivial exercise, right?
Hahahaha.
No, folks, no it was not. IEEE Spectrums Hands On articles provide necessarily linear versions of how projects come together. It can give the impression were terribly clever, which has about the same relationship to reality as an influencers curated social-media feed. So every now and then I like to present a tale steeped in failure, just as a reminder that this is what engineerings like sometimes.
To send screen data to the Mega, I had a choice between several methods that are supported by CircuitPythons display driver libraries. I wanted to use a CircuitPython-powered microcontroller as the Model 100s new brain because theres a lot of existing software I could port over. In particular, CircuitPythons display libraries would greatly simplify creating graphics and text and would automatically update the display. My choices were between a parallel interface and two serial interfaces: SPI and I2C.
The parallel interface would require at least 12 wires. SPI was better, being a four-wire interface. But I2C was best of all, requiring only two wires! Additionally, there are many breakout boards that support I2C, including storage and sensors of all types. One I2C bus can, in theory, support over a hundred I2C peripherals. I2C is much slower than SPI, but the Model 100s delightfully chunky 240-by-64-pixel display is slower still. And Id used I2C-based pe...
01:30
Nexus, an emerging Android banking Trojan targets 450 financial apps Security Affairs
Experts warn of an emerging Android banking trojan dubbed Nexus that was employed in attacks against 450 financial applications.
Cybersecurity firm experts from Cleafy warn of an emerging Android banking trojan, named Nexus, that was employed by multiple groups in attacks against 450 financial applications.
The Nexus ransomware was first analyzed in early March by researchers from the threat intelligence firm Cyble.
Nexus is available via a Malware-as-a-Service (MaaS) subscription and is advertised on underground forums or through private channels (e.g., Telegram) since January 2023.
It was available for rent at a price of $3000 per month.

However, Cleafys Threat Intelligence & Response Team reported having detected the first Nexus infections in June 2022, months before the MaaS was publicly advertised.
Experts believe that the Nexus Trojan is early stages of development despite multiple campaigns are actively using it in the wild.
Nexus provides all the main features to perform ATO attacks (Account Takeover) against banking portals and cryptocurrency services, such as credentials stealing and SMS interception. It also provides a built-in list of injections against 450 financial applications. reads the analysis published by Cleafy.
The authors claim that Nexus has been entirely written from scratch, but the researchers found similarities between Nexus and the SOVA banking trojan, which appeared on the threat landscape in August 2021.
Like...
00:31
Lsm Evo Observe Lsm Restricted Leon Scott Motorsport h+ Media
Lsm Evo Observe Lsm Restricted Leon Scott Motorsport
Some sportsbooks supply promo codes to enter when youre just signing up with the betting web site, or making an attempt to grab some extra bucks into your pocket. Even although this all sounds nice , just dont fall for rip-off promos presented by third-party web sites. Besides being enjoyable to look at, eSports tournaments give on-line betting enthusiasts an opportunity to wager and win actual money.
This convenience permits gamers to gamble with flexibility. It also makes it easy for gamers to calculate their wins. Some currencies embrace USD, EUR, CAD, and the most well-liked NZ dollar.
- Melbet has the latest model of SSL encrypted software program which runs alongside the back end of the web site.
- I.e. theres a hidden commercial of a bookmaker who is in a position to supply his new clients comfy conditions for betting.
- Curacao is amongst the oldest playing jurisdictions on the earth.
- If you are on the lookout for a way to follow playing on line casino video games, but LaMance and others imagine as more states legalize online gambling.
To get the full experience, please allow Javscript in your browser. In the phones settings, discover the Security half and allow the set up of software program from unknown sources. Note that these models are only a small part of the supported smartphones and tablets. Last week on Saturday, Argentina shocked the rugby nation by producing a shock win in opposition to the All Blacks.
Nevertheless, the bookmaker presents many different enticing bonuses and regularly altering promotional provides. The largest benefit of a stay on line casino is undoubtedly the variety of video video games. This is a good various not solely to be taught the mechanics of betting on Melbet, but moreover to get some additional winnings.
Less usually it is a word that offers a link to the bookmaker and to the bonus that can be encrypted in this sentence. The combination is exclusive and legitimate solely within the framework of the announced promotion. Free guess when you lose if the choice losses, part of the stake shall be credited back in free bets. 1xBet Betting Company have their clients engaged in all of its actions and X2 Wednesday Promotion is not any exception to that. People who want to work with MELbet can enroll as an affiliate.
Its Been 24hrs Since My Final Match Won
Melbet App is out there for all Android devices with a system of a minimal of 4.1 and helps all of the capabilities of the primary mannequin of the positioning. For gamers with iOS devices, a separate app is on the market which is no different from the Android app. This is the minimum requirement that you must play comfortably.
Buyer Care
Also, the amazing aspect is...
00:29
Some Vital Features To Assume About About On-line Casino! h+ Media
Some Vital Features To Assume About About On-line Casino!
You have to contemplate promotions and bonuses, fee choices, number of games, graphics, and so forth. These $5 deposit NZ casinos are slowly replacing different platforms with larger minimum deposit necessities. Did you know that the corporate is VeriSign Secured and has a certification with eCOGRA?
The course of could also be performed on the website and in the official app. After that, an e mail might be despatched to your mail confirming the profitable creation of an account. Remember to activate your account by clicking on the link in this letter. You can log in to your personal account by moving into an e-mail address and a password specified all through registration.
Plus, BetMGM offers stay betting and HD streaming for many of these unique sports activities. When it comes to rugby betting coverage, were the most effective within the enterprise. For extra data or assist, use the links to your proper. In India, sports betting apps are shortly choosing the pace and becoming punters first choice to bet on their favourite sports and games.
These bonuses act as motivating incentives to draw extra people to join prime sports platforms. Soccer betting is a competitive business with the highest betting sites developing with new strategies for progress on a regular basis. Betting on football is not just about making deposits, claiming the free bonus, and choosing odds primarily based on guess credits. These finest soccer betting websites have been totally reviewed by our consultants, so youll be able to put your religion in them. This is the preferred betting choice in an NBA sportsbook on-line.
Melbet firm rolls greater than 200 live occasions, and 1,000 sports activities matches within the sportsbook each day. In the on line casino part, you will discover an enormous assortment of video slots, card games, and others. After studying over the exciting bonuses provided at casino sites, you might suppose you have to invest a lot of money in your games. The comparatively low deposit requirement permits Zealanders to take a position their funds better. The platform boasts a few of the most qualitative games powered by Microgaming. You can take pleasure in this expertise on desktops or cell units.
Live casinos permit you to stream games in real-time and in high definition. At these $5 casinos, you get the prospect to try out live dealer video games for such a small fund. This is certainly one of the most played games on on-line and land-based New Zealand casinos. You can use the $5 deposit bonus on line casino NZ to check out baccarat and different variations of the game. Most $5 deposit casinos NZ have a quantity of cost strategies. This will allow gamblers to conduct transactions without friction and with flexibility.
- The courtroom ruling in favor of New Jersey paved the way for states to legalize sports gambling.
- If y...
00:28
Melbet On Line Casino Evaluate Nz$3000 Bonus March 2023 h+ Media
Melbet On Line Casino Evaluate Nz$3000 Bonus March 2023
Leading manufacturers such as Mosswyn Air, EPM-Papst, Ziehl-Abegg, FASCO and Genteq. Submersible Pumps NZ A complete range of submersible pumps to go properly with all functions from ponds and water options to storm water and effluent. However, there are different outstanding 1xBet presents you have to check out. Even so, provides from other bookies such because the Betsafe new customer offer are worthy of your consideration. After you make the deposit, the bonus will mechanically be credited to your account. Such a mix usually seems like a set of some symbols, letters and numbers.
The site allows you to select a provider, so youll simply find Rival on line casino software there. Lets get into the major points of Rival powered on line casino software. Well discuss all its special features, casino bonuses, and main advantages for NZ gamers. In terms of withdrawals, scatter the golden wild playing cards. It asks for 2 players. The record is sort of endless and as you may discover, you will have the benefit of watching what everyone else does before making your own wager.
Some of the best bookies to bet on the Lakers embody 22BET, Betwinner, Betmaster, Melbet, Gunsbet, TonyBet, and BetVictor, simply to mention top up 1xbet a few. Now, eSport websites must acquire licenses of operation and likewise go the extra mile to cushion the non-public knowledge of their customers from the unhealthy guys on the web. The complete listing of Rival casinos introduced above features sites that are obtainable non-stop. They can accept and process your deposit at any time, but they will also present assist if you need it.
Many online sports activities betting sites provide beneficiant welcome provides but require gamers to play via their winnings as much as a hundred occasions to withdraw them as actual money. The court ruling in favor of New Jersey paved the way for states to legalize sports playing. Despite its relative infancy, US on-line sports activities betting apps have already turn out to be wildly well-liked in states like New Jersey or Pennsylvania. But we as an organization dont support/promote betting in any means. The 22 bets app may be thought of protected and secure for Indian sports activities lovers because 22bet is governed by and permitted by the Curacao Gaming Commission.
If you may have lengthy and detailed queries, then a greater choice can be to use the e-mail option. But in distinction to stay chat or a telephone name the place the suggestions is instantaneous, when using e-mail, you could have to attend somewhat longer for a response. Another commendable factor about this bookie has to do with its easy processing of winnings.
- Code, and have placed your first depositand this needs to be between one euro and 130 you possibly can receive a bonus matchi...
00:27
New No Deposit Free Spins Australia Stebbings Automotive, Restoration And Fabrication h+ Media
New No Deposit Free Spins Australia Stebbings Automotive, Restoration And Fabrication
If you may have connected all relevant confirmations, you need to wait for a response. Blackjack is praised as one of the video games with the most effective odds. The guidelines of the game are easy, and the minimum wager you can place is $0.25 and even less. Some of the 5dollar deposit casinos in New Zealand allow players to pick any currency of their alternative.
Many online sports activities betting sites supply generous welcome presents however require players to play through their winnings as a lot as a hundred instances to withdraw them as real cash. The court docket ruling in favor of New Jersey paved the best way for states to legalize sports activities gambling. Despite its relative infancy, US online sports activities betting apps have already become wildly popular in states like New Jersey or Pennsylvania. But we as a company dont support/promote betting in any way. The 22 bets app may be thought of safe and secure for Indian sports activities lovers because 22bet is governed by and permitted by the Curacao Gaming Commission.
The great factor about keep enjoying is that you can work together with the dealers this makes for a additional social gaming expertise. You can also uncover that the usual of those reside streams is nice youll really really feel like youre correct there in motion. Baccarat is a card sport that has been spherical for a lot of of years. It is believed to have originated in Italy nonetheless has since spread everywhere in the world. Top bookies providing greatest odds for Kiwi playersTop 5 issues to contemplate earlier than when selecting the best Should you feel that your betting actions are getting out of hand, then you probably can droop or permanently shut your account at MelBet.
The category includes numerous special events, highlights of current games, and the likelihood to recall a recreation under sure circumstances. BetMGM is the self proclaimed king of sportsbooks, and theres no denying that its platform backs up this slogan. Right from just being an thought to a completely practical enterprise, we help your business to grow at each stage. As gambling may be addictive, its important youre conscious of the dangers and arm yourself with tools and techniques to ensure it remains enjoyable. Go to the Cashier, select Deposit, and choose your most well-liked payment methodology. The best sportsbook will supply a variety of wagers distinctive to cricket.
As a outcome, the location is worth a glance; there are a number of sports markets in addition to on line casino features to select from. MelBet runs a loyalty program for its devoted customers thats available for all of its registered clients. Here, gamers can gather points each time they get to wager and then redeem these factors for real money. Of significance to note is that MelBet has other bonuses and p...
Thursday, 23 March
03:19
Greatest Casinos On-line In India h+ Media
Greatest Casinos On-line In India
Here, each player has the identical probabilities of winning, for the reason that administration presents only licensed software program from trusted providers. Another benefit is the somewhat generous bonus coverage. Each shopper can obtain free spins, bonus funds to their gaming account for sure achievements.
As a end result, the quantity will be deducted out of your account and the bet coupon shall be generated. Wait until the tip of the occasion and, should you win, you will get your winnings according to the odds. The variety of payment techniques in the app is kind of massive, because of this, each player will have the power to select the right one for themselves. The bonus might be mechanically credited after depositing it in the type of further cash in your bonus account. Open the smartphone settings and beneath Security present entry to put in applications from unknown sources.
The 888starz mobile model is a good solution for these users who at all times want to be online at the expense of their cellular system. It is suitable for all, both Android and iOS house owners without any mobile requirements. Just open the location in any of your browsers, log into your account and begin taking half in. The platforms mobile app is designed in the principle colours of the official website black, orange, green and white. Navigating the app may be very straightforward, even for these who are not familiar with the world of playing. The app has a major navigation bar which covers the main areas of the platform such as GAMES, F.A.Q., BONUSES, PROMOTIONS, and NEWS.
If a participant wins the sport, they are eligible to obtain the chips that were wagered on it as a part of their winnings. When you obtain 888sport app in 2023, you take pleasure in sports activities betting, cricket betting, live wagering and streaming, as properly as on line casino gambling. 888sport cell app is an incredible app from a dependable and trusted online bookkeeper. So if youre seeking to place bets in your favourite sports activities, this could be a viable possibility.
For India, you need to choose Rupee or another handy equal from these provided. If you might have a promo code, you can even enter it. After profile verification, the promo code will allow you to get an exciting bonus. While there is not a reside casino right here, there are nine completely different video poker video games that individuals can take part in. These are accessible by way of the menu bar on the prime of the homepage.
- While there is not a stay casino here, there are nine different video poker games that individuals can take part in.
- If you folks add your cash in this utility, then you might be also given additional bonus in it.
- Updating your phone to the most recent operating system can be really helpful.
- I even have already made a deposit, the money is credited to th...