Today, were announcing .onion addresses for eff.org and
two of its affiliated projects: Certbot, an EFF-developed tool for
automatically obtaining and renewing TLS certificates for websites,
and Surveillance Self-Defense, which provides resources and
guidance for individuals and organizations to protect themselves
from surveillance and other security threats.
We have been made aware of events that indicate
censorship could be
occurring on some of our resources. By accessing
these websites through their Tor .onion addresses, users can
further protect their privacy and security while using another
avenue to access important information.
A Tor onion address is a unique identifier for a hidden
service hosted on the Tor network. It is a random string of letters
and numbers followed by the ".onion" top-level domain. Unlike
traditional websites, which have a public IP address that can be
used to locate the server hosting the website, Tor hidden services
have a unique address on the Tor network that provides end-to-end
encryption and anonymity. Tor routes the connection through several
relays, which can be run by different individuals or organizations
all over the world. The final exit relay would connect to eff.org
normally. The ISP can see that
youre using Tor, but cannot easily see what site you are
visiting.

Tor onions are useful for hosting a copy of your website
within the Tor network without the need to leave via an exit relay,
providing an extra layer of protection and obscurity.
EFF has long partnered with Tor and supported the project.
So we are glad to have our own resources hosted on the Tor network
for those out there in parts of the world where internet
surveillance is heightened or modified due to oppressive regimes
and laws.
eff.org
iykpqm7jiradoeezzkhj7c4b33g4hbgfwelht2evxxeicbpjy44c7ead.onion
certbot.eff.org
5yl6j7al5iwjn3kltayvumj5d25agnq4t6rznkvphossoqyzb3batwid.onion
ssd.eff.org
y7yea4pmqqtznb33qiugvysyn2bob5v62e4pvoadoibrwkq3tsddjeyd.onion












 Over the
past several years, a wave of copyright infringement lawsuits has
targeted alleged cheaters and cheat makers.
Over the
past several years, a wave of copyright infringement lawsuits has
targeted alleged cheaters and cheat makers.









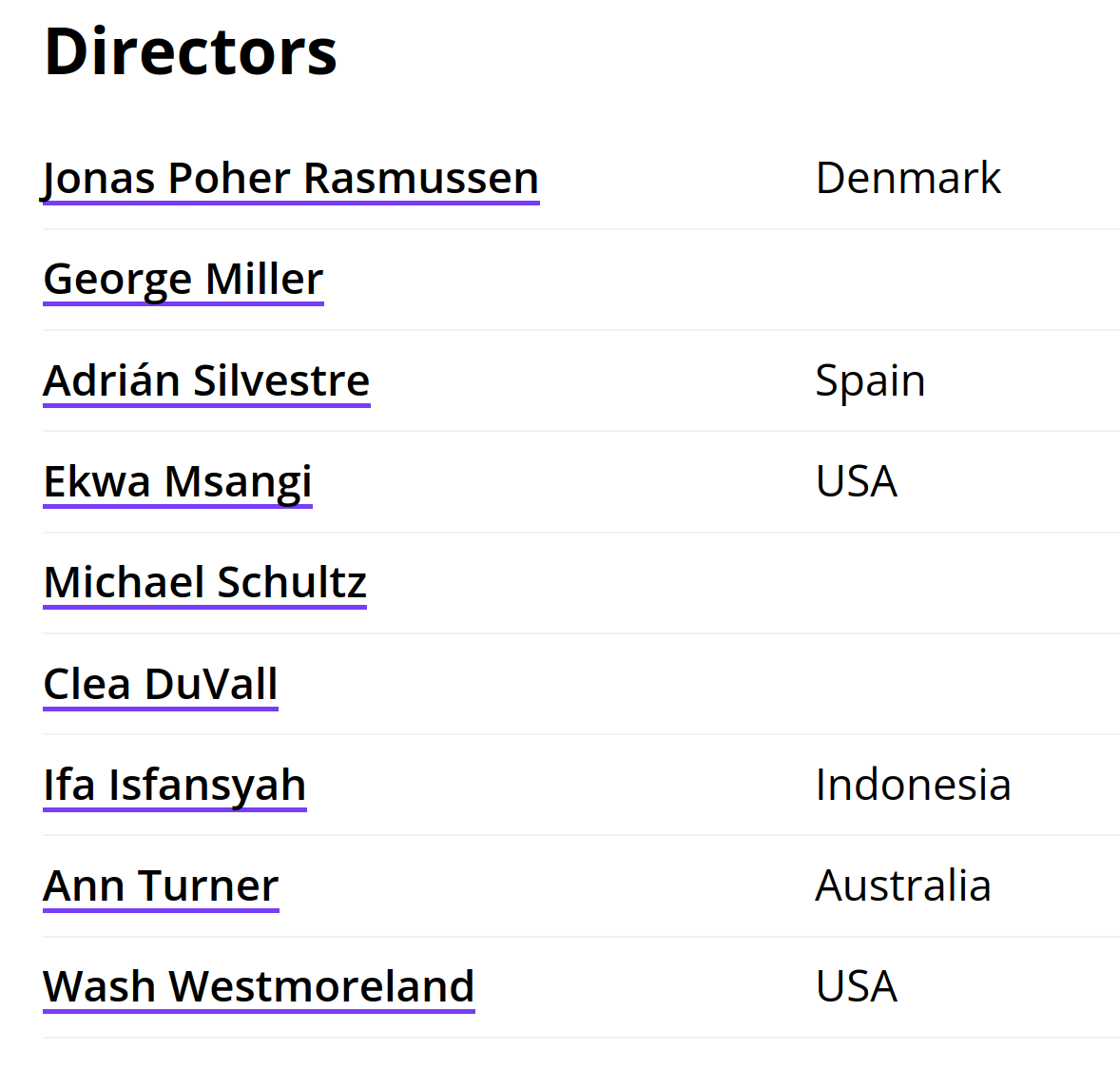










 Two years ago, the Motion Picture Association (MPA)
Two years ago, the Motion Picture Association (MPA) 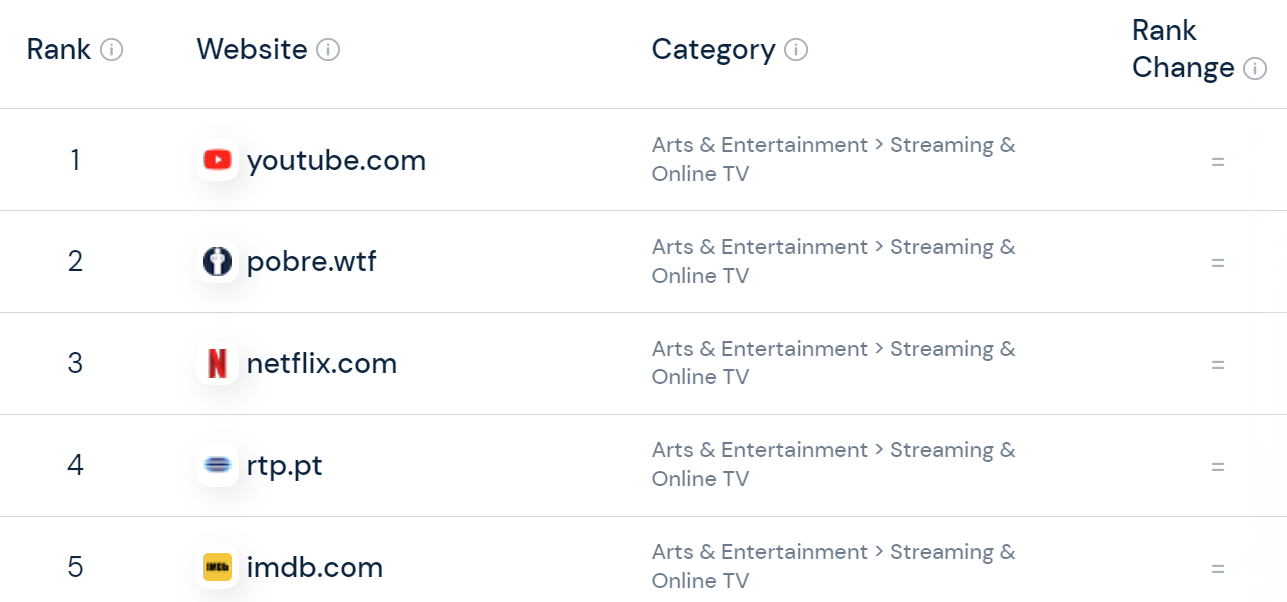















 CasinoThis is the principle part that comprises all games the
bookie has. For instance, as a substitute of betting on whose hand
might be higher in Baccarat, you guess on the Bankers hand to be
eight. The bookie works with the highest software developers like
NetEnt and Microgaming. Having examined 1XBet totally, it is little
wonder that the net casino is massively popular in India. With a
great number of games being available, all from prime software
providers, the casino additionally scores highly in terms of funds,
cell betting and bonuses.
CasinoThis is the principle part that comprises all games the
bookie has. For instance, as a substitute of betting on whose hand
might be higher in Baccarat, you guess on the Bankers hand to be
eight. The bookie works with the highest software developers like
NetEnt and Microgaming. Having examined 1XBet totally, it is little
wonder that the net casino is massively popular in India. With a
great number of games being available, all from prime software
providers, the casino additionally scores highly in terms of funds,
cell betting and bonuses.





















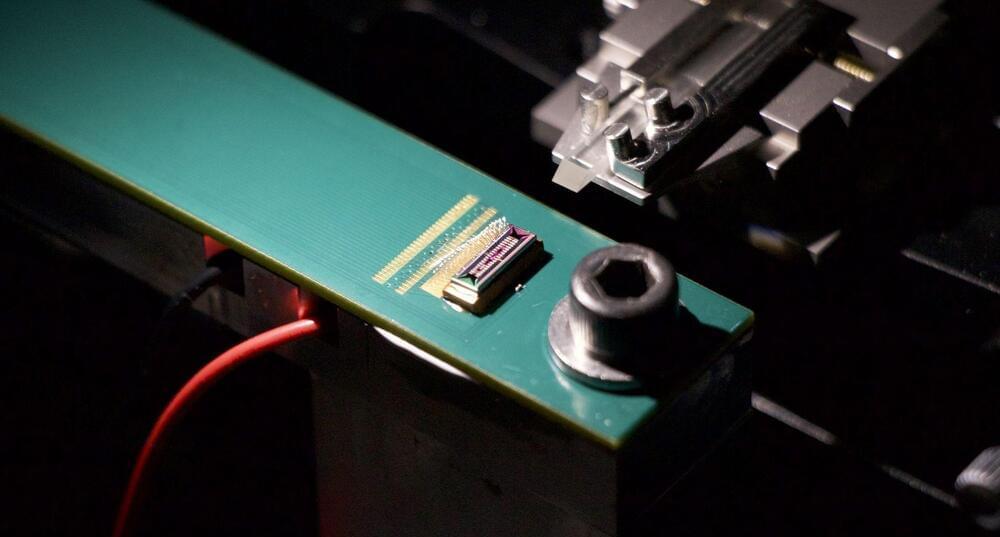
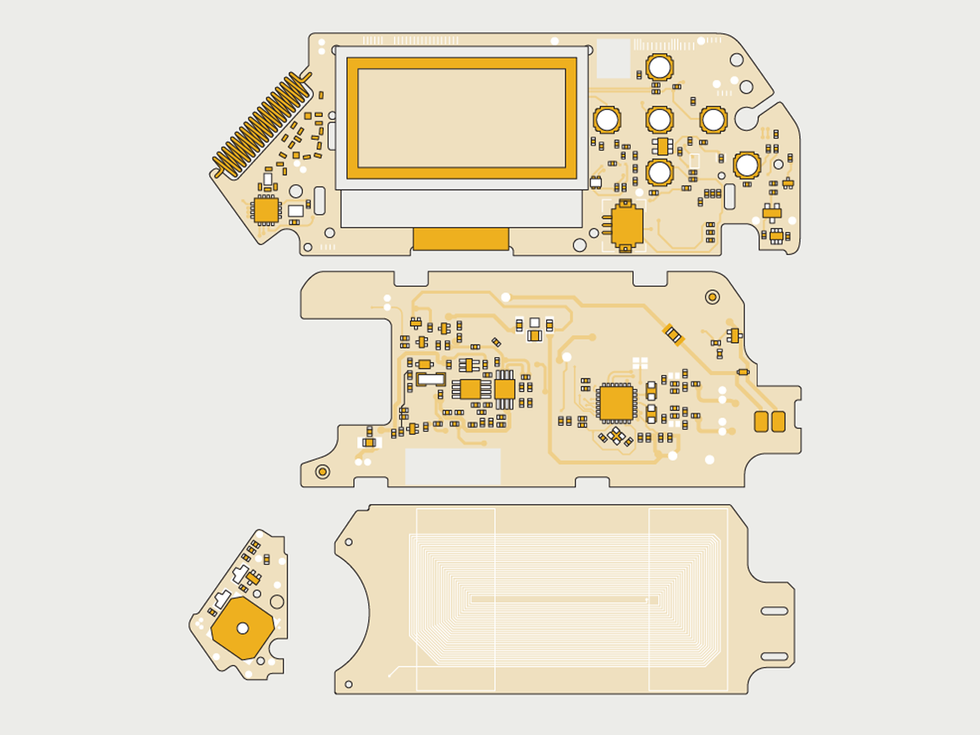 An
open-source design, the Flipper is composed of a main board with an
ARM-based CPU and transceiver chip, a board for NFC and RFID
communications, a PCB antenna, and an extra board to handle IR and
iButton interfacing.James Provost
An
open-source design, the Flipper is composed of a main board with an
ARM-based CPU and transceiver chip, a board for NFC and RFID
communications, a PCB antenna, and an extra board to handle IR and
iButton interfacing.James Provost





 Piracy is by no means exclusive to any particular generation
but among the general public, its often associated with younger
people.
Piracy is by no means exclusive to any particular generation
but among the general public, its often associated with younger
people.