| IndyWatch Science and Technology News Feed Archiver | |
 |
Go Back:30 Days | 7 Days | 2 Days | 1 Day |
|
IndyWatch Science and Technology News Feed was generated at World News IndyWatch. |
|
Thursday, 06 April
03:50
Police Confirm FBI-Assisted Takedown of Piracy Release Group EVO TorrentFreak
 EVO, short for EVOLUTiON, was a high-profile P2P group whose
activities stood out in recent years.
EVO, short for EVOLUTiON, was a high-profile P2P group whose
activities stood out in recent years.
The group released a steady stream of new movie and TV show titles and gained pirates admiration by leaking many screeners way ahead of their official premieres.
For several years in a row, EVO opened the screener season by releasing leaked copies of upcoming films. This included Oscar contenders, but also several Netflix titles that originated from festival screenings.
EVO was also the first to release an early Blu-Ray copy of Spider-Man: No Way Home last year, and a high-quality copy of the blockbuster Dune in 2021, ahead of its official U.S. premiere.
Like many other groups, EVO posted new releases on a regular schedule but that came to an abrupt halt last November when the group suddenly went quiet. While no explanation was given at the time, many pirates feared that the group had been busted.
National Criminal Investigation Police Take Credit
A few weeks ago TorrentFreak was able to confirm that this was indeed the case. Anti-piracy coalition ACE informed us that it had been working with Portuguese authorities to shut the group down and arrest its alleged leader.
This week Portuals Polcia Judiciria publicly confirmed that enforcement action Operation EVO 1.2 had been carried out through UNC3T, the national cybercrime unit.
The criminal investigation into EVO started early last year, following a complaint from Disney Enterprises, Paramount Pictures, Universal City Studios, Columbia Pictures, Warner Bros., Netflix, and Amazon. These are all members of the Motion Picture Association (MPA) and related...
03:30
Intel Vulkan Driver Squeezes In A Few More Performance Optimizations For Mesa 23.1 Phoronix
Ahead of the Mesa 23.1 branching and feature freeze coming up in the next week or two, Intel's open-source graphics driver developers have been landing some last minute performance optimizations to benefit their "ANV" Vulkan driver...
03:24
Dozer exits stealth to help any developer build real-time data apps in minutes Lifeboat News: The Blog
Data has emerged as one of the worlds greatest resources, underpinning everything from video-recommendation engines and digital banking, to the burgeoning AI revolution. But in a world where data has become increasingly distributed across locations, from databases to data warehouses to data lakes and beyond, combining it all into a compatible format for use in real-time scenarios can be a mammoth undertaking.
For context, applications that dont require instant, real-time data access can simply combine and process data in batches at fixed intervals. This so-called batch data processing can be useful for things like processing monthly sales data. But often, a company will need real-time access to data as its created, and this might be pivotal for customer support software that relies on current information about each and every sale, for example.
Elsewhere, ride-hail apps also need to process all manner of data points in order to connect a rider with a driver this isnt something that can wait a few days. These kinds of scenarios require what is known as stream data processing, where data is collected and combined for real-time access, which is far more complex to configure.
03:23
Rainbows are actually full circles. A physicist explains Lifeboat News: The Blog
Most of us only ever see a fraction of a full rainbow: an arc. But optically, a full rainbow makes a complete circle. Physics explains why.
03:23
This Insane 256-Foot Superyacht Concept Doubles as a Fully Functional Submarine Lifeboat News: The Blog
The concept for the CARAPACE yacht is sent straight from the future.
The 78m vessel has been conceptualized to double as a submarine that can dive to 985 feet.
Elena Nappi, an Italian based naval architect, has dreamed up this futuristic vessel.
The hybrid is designed for cruising the high seas and exploring the underwater world with its marine capabilities.
03:23
Mind-Bending Animation Shows How The Universe Would Look if We Could See Gamma Rays Lifeboat News: The Blog
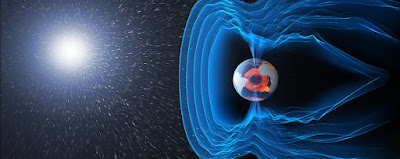
Most of the light streaming through the Universe is invisible to human eyes. Beyond the mid-range wavelengths we can see, theres a whole cosmos shining in high-and low-energy radiation.
But we humans are clever little animals and have managed to build instruments that can see the light we cannot. One of these is NASAs Fermi Gamma-ray Space Telescope, an observatory hanging out in low-Earth orbit, monitoring the sky for gamma rays, the highest-energy light in the Universe.
Fermi constantly surveils the entire sky, observing gamma-ray sources and how they change over time, providing astronomers with a map of the various producers of gamma radiation that we can detect. This data is compiled into a catalog that scientists can use to probe the production of gamma radiation.
03:00
Retrotechtacular: Solder Like its 1944! Hackaday

When we first saw this 1944 US Office of Education film about hand soldering, we figured it might still have some good information. Well, perhaps it does, but the 1944 soldering was with a giant iron, and the work looked more like metal bricks than anything weve soldered lately. Of course, the physics is all the same, but some of the terminology, like sweating in isnt anything weve heard before, although we have heard of sweat soldering.
They do show some electronic soldering on components, including some interesting-looking coils. But the irons look more like a bad science fiction movies idea of a lightsaber. The solder is equally huge, of course.
If it Smells Like Bacon
We liked the soldering iron holder with a magnifier or maybe it is just a piece of shield glass that the lady in the movie uses. It would have made a perfect vent hood, too, but in 1944 we are guessing you were encouraged to sniff the fumes. They mention not letting wire fly into your eye, but they didnt cover safety glasses until well after that part. Not a word about lead safety, either.
The tip on the iron is bigger than most of the screwdrivers on our bench. Other than the scale, we didnt find much to disagree with in the film. After all, soldering is soldering regardless of the size of the solder joints. Of course, the real excitement comes at the end when they start using a flame to do some bulk soldering of some enclosures.
...02:58
How Russia Killed its Tech Industry SoylentNews
You may think, as I did, that Russia's current tech woe's are as a result of their invasion of Ukraine, or perhaps the annexation of Crimea. But it seems that the real problem started back around 2011 when it decided that the population having free access to information was not a good thing and, anyway, there must be money to be made if someone can take the tech industry under their control.
In Russia, technology was one of the few sectors where people felt they could succeed on merit instead of connections. The industry also maintained a spirit of openness: Russian entrepreneurs won international funding and made deals all over the world. For a time, the Kremlin seemed to embrace this openness too, inviting international companies to invest in Russia.
But cracks in Russia's tech industry started appearing well before the war. For more than a decade, the government has attempted to put Russia's internet and its most powerful tech companies in a tight grip, threatening an industry that once promised to bring the country into the future. Experts MIT Technology Review spoke with say Russia's war against Ukraine only accelerated the damage that was already being done, further pushing the country's biggest tech companies into isolation and chaos and corralling its citizens into its tightly controlled domestic internet, where news comes from official government sources and free speech is severely curtailed.
"The Russian leadership chose a completely different path of development for the country," says Ruben Enikolopov, assistant professor at the Barcelona School of Economics and former rector of Russia's New Economic School. Isolation became a strategic choice, he says.
The tech industry was not Russia's biggest, but it was one of the main drivers of the economy, says Enikolopov. Between 2015 and 2021, the IT sector in Russia was responsible for more than a third of the growth in the country's GDP, reaching 3.7 trillion rubles ($47.8 billion) in 2021. Even though that constituted just 3.2% of total GDP, Enikolopov saysthat as the tech industry falls behind, Russia's economy will stagnate. "I think this is probably one of the biggest blows to future economic growth in Russia," he says.
Read more of this story at SoylentNews.
02:30
HP WMI Driver To Expose More Sensors Under Linux For Business-Class Systems Phoronix
A patch was posted this week introducing a new "hp-wmi-sensors" Linux kernel driver for HP business-class computers for exposing WMI sensor functionality...
01:46
Z2U Market Leak Exposes Access to Illicit Services and Malware HackRead | Latest Cybersecurity and Hacking News Site
According to documents analyzed by Jeremiah Fowler, Z2U sells malware and other malicious services to customers under the guise of online trading.
This is a post from HackRead.com Read the original post: Z2U Market Leak Exposes Access to Illicit Services and Malware
01:40
Links 05/04/2023: GTK 4.11.1, Wayland 1.22, and Gajim 1.7.3 Techrights
![]()
Contents
-
GNU/Linux
-
Desktop/Laptop
-
Liliputing System76 teases made-in-Denver Linux laptop
System76 has been selling PCs that ship with Linux pre-installed for years. But for most of that time the company has worked with third-pa...
-
-
01:30
Typewriter Mashup Becomes 120-Year-Old Teletype Hackaday

Vintage typewriters can be beautiful and elegant devices. But theres a limit to their value if, as with the 1903 Remington owned by [Daniel Ross], they are fire-damaged and have a seized mechanism. What did he do with what was essentially a piece of scrap metal? Produce an unholy mashup of the vintage machine and a 1988 Sharp daisy wheel typewriter to make a steampunk-style teletype, of course!
Stripping down both machines was evidently no easy task, and the result hes achieved has the Sharps printer mechanism at 90 degrees to its original orientation sitting below the roller in the space once occupied by the Remingtons type bars. Were sad to see that the keyboard on the older machine appears to be inoperable, but on the other hand each letter does light up as its typed.
Meanwhile at the electronics side the components from the Sharp have been transferred to a custom PCB, and the whole can be driven from a 300-baud serial line. As can be seen from the video below the break, the result is an unholy love-child of two typewriters that could scarcely be more different, but somehow it works to make an impressive whole.
If this project looks a little familiar to Hackaday readers, its because weve mentioned it in passing before. Its hooked up...
01:24
Why It Was Important to Translate Linux Foundation Training Manuals to Ukrainian FOSS Force
The software industry plays a large role in Ukraine's economy, with many Ukrainian developers working remotely from Ukraine for software vendors located in the EU, UK, and US. Training manuals in the Ukrainian language will help veterans of Ukraine's military struggles against Russia take advantage of this opportunity.
The post Why It Was Important to Translate Linux Foundation Training Manuals to Ukrainian appeared first on FOSS Force.
01:23
Study explores the extent of Western dependency on Russian nuclear energy Lifeboat News: The Blog
Russias invasion of Ukraine in February 2022 had a profound deep impact on the economy, inflating the prices of energy and food, with detrimental consequences for both individuals and companies worldwide. As a result, many governments, particularly in Europe, have been discussing the possibility of reducing their dependence on Russian energy.
Most of these ongoing discussions specifically focus on fossil fuel energy, leading to the gradual introduction of sanctions for purchasing Russian coal, oil, and gas. However, Russia is also a key global provider of nuclear power, particularly via a state-owned nuclear energy corporation called Rosatom.
Researchers at the Norwegian Institute of International Affairs (NUPI) have recently carried out a study investigating the activity and global portfolio of Rosatom and its subsidiaries. Their findings, published in Nature Energy, highlight the high degree of European dependency on nuclear energy produced by this company, raising important questions about the need to find alternative energy suppliers.
01:23
More happy birthdays! Research says people could live to 141 Lifeboat News: The Blog
A scientist has predicted that men could live for as long as 141 years and women could reach over 130.
01:22
Scientists believe they may have found the secret to living to 100 and beyond Lifeboat News: The Blog
Scientists believe they may have found the secret to living past the age of 100. To some, the thought of living into your hundreds is a dream, while for others, its the complete opposite. But it seems that 70 percent of American adults actually want to live to 100, a 2022 poll by Edward Jones and Age Wave of 11,000 people revealed.
00:26
Survey results: the usage of money in Debian LWN.net
The Debian project has reported on a survey of developers on the use of project funds to support development work.
There seems to be broad support for paying people who are already involved as Debian contributors, but very little support for hiring contractors, that is to say, those who are not already Debian contributors in some way. Members of the Security Team were by far the most supportive towards the idea of paying Debian contributors.
The full report is available for those wanting all the details and pie charts.
00:17
CryptoClippy: New Clipper Malware Targeting Portuguese Cryptocurrency Users The Hacker News
Portuguese users are being targeted by a new malware codenamed CryptoClippy that's capable of stealing cryptocurrency as part of a malvertising campaign. The activity leverages SEO poisoning techniques to entice users searching for "WhatsApp web" to rogue domains hosting the malware, Palo Alto Networks Unit 42 said in a new report published today. CryptoClippy, a C-based executable, is a type
00:14
Lots of Microsoft Shutdowns Reported Today (Whole Offices, Divisions and Products Axed Entirely) Techrights
Can the chaffbot generate enough media noise/smokescreen (all that AI chaff) to distract from all that?
Yes, buzzwords as a vapourware tactic (be patient, shareholders, well razzle-dazzle you in the future while we lose money now). Weve seen this before. First "metaverse", now "AI" (they misleabel or call almost everything that)
Turns out greenwashing PR is a luxury when the marketing budget runs thin and the clown computing business disputes false narratives (AI means a lot of unnecessary pollution).
That does not seem like the hallmark of a healthy company. Even its expansion plan/PR turns out to be vapourware.
Summary: Microsofts layoffs and shrinking business footprint is a big feature this month, even if the media keeps focusing on vapourware and hype instead (Microsoft pays for misplaced media focus)
00:12
German Police Raid DDoS-Friendly Host FlyHosting SoylentNews
German Police Raid DDoS-Friendly Host 'FlyHosting':
Authorities in Germany this week seized Internet servers that powered FlyHosting, a dark web offering that catered to cybercriminals operating DDoS-for-hire services, KrebsOnSecurity has learned. FlyHosting first advertised on cybercrime forums in November 2022, saying it was a Germany-based hosting firm that was open for business to anyone looking for a reliable place to host malware, botnet controllers, or DDoS-for-hire infrastructure.
A statement released today by the German Federal Criminal Police Office says they served eight search warrants on March 30, and identified five individuals aged 16-24 suspected of operating "an internet service" since mid-2021. The German authorities did not name the suspects or the Internet service in question.
"Previously unknown perpetrators used the Internet service provided by the suspects in particular for so-called 'DDoS attacks', i.e. the simultaneous sending of a large number of data packets via the Internet for the purpose of disrupting other data processing systems," the statement reads.
[...] The German authorities said that as a result of the DDoS attacks facilitated by the defendants, the websites of various companies as well as those of the Hesse police have been overloaded in several cases since mid-2021, "so that they could only be operated to a limited extent or no longer at times."
The statement says police seized mobile phones, laptops, tablets, storage media and handwritten notes from the unnamed defendants, and confiscated servers operated by the suspects in Germany, Finland and the Netherlands.
[...] The apparent raids on FlyHosting come amid a broader law enforcement crackdown on DDoS-for-hire services internationally. The U.K.'s National Crime Agency announced last week that it's been busy setting up phony DDoS-for-hire websites that seek to collect information on users, remind them that launching DDoS attacks is illegal, and generally increase the level of paranoia for people looking to hire such services.
Read more of this story at SoylentNews.
00:00
How Tattoos Interact With The Immune System Could Have Impacts for Vaccines Hackaday

Tattoos are an interesting technology. Theyre a way of marking patterns and designs on the skin that can last for years or decades. All this, despite the fact that our skin sloughs off on a regular basis!
As it turns out, tattoos actually have a deep and complex interaction with our immune system, which hold some of the secrets regarding their longevity. New research has unveiled more insight into how the body responds when we get inked up.
Not Going Anywhere
As we all know, if you draw something on your skin with a pen, paint, or marker, it will eventually come off in a few days or so. Tattoos, on the other hand, are far more longer lasting. The basic theory of tattooing is simple. Rather than putting ink on the epidermis (the upper layer of skin), it is instead inserted into the underlying upper dermis. There, the ink is free from the day-to-day sloughing off of skin. A properly-performed tattoo can last a lifetime, and beyond, in the case of the oldest identified tattooed individual from 3250 BC.
...00:00
Wednesday, 05 April
23:53
HP would take up to 90 days to fix a critical bug in some business-grade printers Security Affairs
HP would take up to 90 days to address a critical flaw, tracked as CVE-2023-1707, that resides in the firmware of some business-grade printers.
HP is aware of a critical vulnerability, tracked as CVE-2023-1707 (CVSS v3.1 score 9.1), that affects tens of HP Enterprise LaserJet and HP LaserJet Managed Printers models. The exploitation of the flaw can potentially lead to information disclosure and the IT giant announced that it would take up to 90 days to address the vulnerability. An attack can trigger the bug to access data transmitted between the vulnerable HP printer and other systems on the same network segment.
The company pointed out that the information disclosure can be achieved only by exploiting the flaw on vulnerable devices running
Certain HP Enterprise LaserJet and HP LaserJet Managed Printers are potentially vulnerable to information disclosure when IPsec is enabled with FutureSmart version 5.6. reads the bulletin published by the company.
The vendor has released temporary firmware mitigation for customers currently running FutureSmart 5.6 with IPsec enabled on their printers. The company recommends customers immediately revert
HP told BleepingComputer that it is not aware of any active exploits, the company pointed out that the exposure period to this potential vulnerability was limited to mid-February 2023 until the end of March 2023)
Please vote for Security Affairs (https://securityaffairs.com/) as
the best European Cybersecurity Blogger Awards 2022 VOTE FOR YOUR
WINNERS
Vote for me in the sections:
- The Teacher Most Educational Blog
- The Entertainer Most Entertaining Blog
- The Tech Whizz Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
Nominate here: https://docs.google.com/forms/d/e/1FAIpQLSfaFMkrMlrLhOBsRPKdv56Y4HgC88Bcji4V7OCxCm_OmyPoLw/viewform
Follow me on Twitter: @securityaffairs and&nbs...
23:35
Security updates for Wednesday LWN.net
Security updates have been issued by Debian (ghostscript and openimageio), Fedora (kernel, rubygem-actioncable, rubygem-actionmailbox, rubygem-actionmailer, rubygem-actionpack, rubygem-actiontext, rubygem-actionview, rubygem-activejob, rubygem-activemodel, rubygem-activerecord, rubygem-activestorage, rubygem-activesupport, rubygem-rails, and rubygem-railties), Oracle (gnutls, httpd, kernel, nodejs:16, nodejs:18, pesign, postgresql:13, tigervnc, and tigervnc, xorg-x11-server), Red Hat (gnutls, httpd, httpd:2.4, kernel, kpatch-patch, pcs, pesign, postgresql:13, tigervnc, and tigervnc, xorg-x11-server), Scientific Linux (httpd and tigervnc, xorg-x11-server), SUSE (aws-efs-utils.11048, libheif, liblouis, openssl, python-cryptography, python-Werkzeug, skopeo, tomcat, and wireshark), and Ubuntu (imagemagick, ipmitool, and node-trim-newlines).
23:24
AGI Unleashed: Game Theory, Byzantine Generals, and the Heuristic Imperatives Lifeboat News: The Blog

Patreon: https://www.patreon.com/daveshap.
GitHub: https://github.com/daveshap.
Cognitive AI Lab Discord: https://discord.gg/yqaBG5rh4j.
Artificial Sentience Reddit: https://www.reddit.com/r/ArtificialSentience/
Heuristic Imperatives Reddit: https://www.reddit.com/r/HeuristicImperatives/
DISCLAIMER: This video is not medical, financial, or legal advice. This is just my personal story and research findings. Always consult a licensed professional.
I work to better myself and the rest of humanity.
23:23
Stephen Hawkings famous black hole paradox looks to finally have a solution Lifeboat News: The Blog
The Hawking radiation emitted by black holes may be able to carry crucial information, a new study suggests. Scientists may have just found the solution to one of astrophysics most mind-boggling mysteries concerning black holes, also known as the Hawking information paradox. A study published in the journal Physics Letters B last month offers a resolution to a problem the late physicist Stephen Hawking was working on in his final years.
23:23
23:18
Genesis Markets Clearnet domain seized; Dark Web site still online HackRead | Latest Cybersecurity and Hacking News Site
By Waqas
The FBI and European authorities have seized Genesis Markets clearnet domains as part of the ongoing Operation Cookie
This is a post from HackRead.com Read the original post: Genesis Markets Clearnet domain seized; Dark Web site still online
23:13
Cyber threats organizations should keep an eye on in 2023 Help Net Security
In Malwarebytes most recent report on the current state of malware, the company has identified several high-profile cyber threats that organizations should be on the lookout for in 2023. The 5 most important cyber threats LockBit, an affiliate-based ransomware variant, has dominated the 2022 threat lascape, and it has affected hundreds of businesses of all sizes. Since April 2022, one in three known ransomware attacks has involved LockBit, the report revealed. Two of the currently More
The post Cyber threats organizations should keep an eye on in 2023 appeared first on Help Net Security.
23:01
How API burn rate alerts are calculated in Red Hat OpenShift Linux.com
Burn rates help you predict whether your downtime is too high or risks exceeding your service-level objective.
Read More at Enable Sysadmin
The post How API burn rate alerts are calculated in Red Hat OpenShift appeared first on Linux.com.
23:00
AMD Ryzen 7 7800X3D Linux Performance Phoronix
While the AMD Ryzen 9 7950X3D and Ryzen 9 7900X3D processors went on sale at the end of February as the first Zen 4 3D V-Cache processors, today marks the availability of the Ryzen 7 7800X3D processor. I've recently been putting the 7800X3D through its paces under Linux and have a plethora of benchmark data to share for launch day.
22:36
Hackers Using Self-Extracting Archives Exploit for Stealthy Backdoor Attacks The Hacker News
An unknown threat actor used a malicious self-extracting archive (SFX) file in an attempt to establish persistent backdoor access to a victim's environment, new findings from CrowdStrike show. SFX files are capable of extracting the data contained within them without the need for dedicated software to display the file contents. It achieves this by including a decompressor stub, a piece of code
22:27
GTK 4.11.1 Released With Better Textures, Wayland Fractional Scaling Phoronix
Following this week's Qt 6.5 LTS and Slint 1.0 Rust toolkit, debuting today is GTK 4.11.1 as the first development release of the new toolkit series in leading up to GTK 4.12...
22:19
Google TAG Warns of North Korean-linked ARCHIPELAGO Cyberattacks The Hacker News
A North Korean government-backed threat actor has been linked to attacks targeting government and military personnel, think tanks, policy makers, academics, and researchers in South Korea and the U.S. Google's Threat Analysis Group (TAG) is tracking the cluster under the name ARCHIPELAGO, which it said is a subset of another threat group tracked by Mandiant under the name APT43. The tech giant
22:15
CISA JCDC Will Focus on Energy Sector Security Affairs
The CISA s Joint Cyber Defense Collective (JCDC) initiative is going to build operation plans for protecting and responding to cyber threats.
What comes to mind when you think of cyber criminals? Depending on who you ask, youll get a variety of answers. For some, a cyber criminal matches some of the Hollywood tropes: a person sitting alone in a dimly lit room, furiously mashing on a keyboard to steal information from a person or company.
Those days are behind us, however, as cybercrime is establishing itself as a business in and of itself. Cyber attack instances are steeply rising across all sectors, leaving even the FBI to issue a bulletin about business email compromise (BEC) the $43 billion scam.
Taking note of the pervasive threat landscape, the US government has devoted more resources to building a team to protect citizens and businesses. This effort began with the 2018 establishment of the Cybersecurity and Infrastructure Security Agency (CISA), a Department of Homeland Security division.
Going one step further, in 2021, the CISA announced the formation of the Joint Cyber Defense Collective (JCDC), an initiative formulated to bring government and private industry representatives together to build operation plans for protecting and responding to cyber threats.
The JCDC has seen the benefits of collaboration for exigent risks (such as the heightened awareness and protection related to Russias invasion of Ukraine and the Log4Shell vulnerability) but sees a remaining gap when it comes to imminent risk. To address this gap, the JCDC is planning proactive measures for future cyber risks.
The backbone of this planning is the JCDCs 2023 Planning Agenda. The aim of the Agenda is to leverage the expertise of public and private sector members to develop and launch defense plans focused on risk reduction.
2023 Planning Agenda
The inaugural 2023 Planning Agenda will focus on three key topics:
Collective Cyber Response
JCDC will update the National Cyber Incident Response Plan in collaboration with the FBI, including outlying roles for non-federal units for incident response.
Systemic Risk
Cybercrime is a broad-reaching threat relevant to both individuals and organizations. The allure of a significant payday from successful cyber...
22:11
OSI: Lets Repeat Microsoft Lies Techrights
Two years before bagging bribes from Microsoft the OSI
published this: [PDF]
Of course it has gotten a lot worse since then. For example, consider this overt case of OSI lobbying for Microsoft in the class action lawsuit over GitHub Copilot (GPL violations). This is MICROSOFT funded. This is MICROSOFT staff. This is MICROSOFT propaganda. All this for MICROSOFT GPL VIOLATIONS. Hosted by a MICROSOFT-BRIBED OSI. They buy the OSIs platform and we know whose bank account nets those salaries.
Sometimes it feels like theres no greater foe or enemy to Open Source than the OSI itself (because of the misleading name, which complicates matters; its a powerful lobbying instrument). It literally works against its original mission, as last witnessed yesterday.
22:00
Remembering the Legacy of Trailblazing Technologist Gordon Moore IEEE Spectrum

Intel cofounder Gordon E. Moore, the man behind Moores Law, died on 24 March at the age of 94.
The IEEE Fellow was awarded the 2008 IEEE Medal of Honor for pioneering technical roles in integrated-circuit processing, and leadership in the development of MOS memory, the microprocessor computer, and the semiconductor industry.
Moore founded Intel in 1968 with computing pioneer Robert Noyce. Moore, Noyce, and other Intel engineers are credited with bringing laptop computers and numerous other electronics to millions of people thanks to their semiconductor development. Intel microprocessors now power personal computers made by major manufacturers including Dell, HP, and IBM.
Moore is best known for his 1965 prediction, which would become known as Moores Law: the observation that the number of transistors on an integrated circuit would grow exponentially while the retail cost of computers would decrease.
His original hypothesis, published in a 1965 Electronics magazine article, was that the number of transistors would double each year. His projection came true over the decade that followed. In 1975 he revised the theory and forecast that transistors would double every 18 monthsa statement that held true for several decades. Moores Law set the bar for semiconductor manufacturers and is still driving computing innovations today.
Gordon Moore, with his prediction that turned to law, captured the very gestalt of the semiconductor industry as an exponential ambition, says...
22:00
Ubuntu Talks Up Rust Kernel Programming Potential With Ubuntu 23.04 Phoronix
Ubuntu 23.04 is being talked up for how it can aide developers that want to begin programming with Rust code for Linux kernel modules. It's possible to get started with Rust kernel development on Ubuntu 23.04 thanks to its generic kernel having the necessary kernel configuration, but ultimately it's still in an early state and there isn't much to do with the stock kernel...
21:49
Law enforcement seized the Genesis Market cybercrime marketplace Security Affairs
Law enforcement seized the Genesis Market black marketplace, a platform focused on the sale of stolen credentials, as part of Operation Cookie Monster.
The FBI seized the Genesis Market, a black marketplace for stolen credentials that was launched in 2017. Genesis Market was an invite-only marketplace, but it was not complex to find invite codes online.
One of the most interesting features offered by the platform is the access to browser fingerprints that allow crooks to impersonate victims web browsers, including IP addresses, operating system data, time zones, device info, session cookies, and more.
The price for a stolen account was very cheap, paying a few dollars crooks were able to use it for a specific period. Genesis Market provided access to accounts of the most popular services, including Amazon, eBay, Facebook, Gmail, Netflix, PayPal, Spotify, and Zoom.
The seizure is part of a law enforcement operation codenamed Operation Cookie Monster.
The home page of the Genesis Market domains now shows a banner informing visitors that the FBI has executed a seizure warrant.
These seizures were possible because of international law enforcement and private sector coordination involving the partners listed below reads the banner.
The authorities are searching for information about the administrators of the platform, a circumstance that suggests that the FBI has yet to identify them.
Please vote for Security Affairs (https://securityaffairs.com/) as
the best European Cybersecurity Blogger Awards 2022 VOTE FOR YOUR
WINNERS
Vote for me in the sections:
- The Teacher Most Ed...
21:49
Flood of malicious packages results in NPM registry DoS Help Net Security
Attackers are exploiting the good reputation and openness of the popular public JavaScript software registry NPM to deliver malware and scams, but are also simultaneously and inadvertently launching DoS attacks against the service. Malicious package on NPM pointing to a site serving malware (Source: Checkmarx) The unstoppable load created by those automated scripts made NPM unstable with sporadic Service Unavailable errors. I can witness in the past week it happened to me and my colleagues More
The post Flood of malicious packages results in NPM registry DoS appeared first on Help Net Security.
21:49
Protect Your Company: Ransomware Prevention Made Easy The Hacker News
Every year hundreds of millions of malware attacks occur worldwide, and every year businesses deal with the impact of viruses, worms, keyloggers, and ransomware. Malware is a pernicious threat and the biggest driver for businesses to look for cybersecurity solutions. Naturally, businesses want to find products that will stop malware in its tracks, and so they search for solutions to do that.
21:30
Fortinet enhances Security Fabric with real-time response and automation capabilities Help Net Security
Fortinet has expanded the Fortinet Security Fabric with new and enhanced products and capabilities to enable advanced threat prevention and coordinated response for a self-defending ecosystem across networks, endpoints, and clouds. The majority of organizations are pursuing a consolidation strategy for their security According to a recent survey from Gartner, 75 percent of organizations are pursuing security vendor consolidation, up from 29 percent in 2020. The same survey notes, Security and risk management leaders are More
The post Fortinet enhances Security Fabric with real-time response and automation capabilities appeared first on Help Net Security.
21:24
OSI Blog Composed by Microsofters on Microsofts Payroll, Promoting Proprietary GitHub Using Microsofts Terminology Techrights
Sponsored by Microsoft to occupy the OSI, serving and pushing Microsoft agenda, lobbying for proprietary software (under the guise of community!) and even painting plagiarism/GPL violations as benign "AI"
Yesterday:
This is what OSI is advocating:

Summary: Not only does Microsoft besiege the OSI's Board; it also has staff on the payroll (Microsoft's money) pushing the OSI in Microsofts direction; the OSI actively works to undermine its own mission, having taken money from (been bribed by) its foremost foe half a decade ago
21:22
Mullvad VPN And The Tor Project Collaborate On A Web Browser SoylentNews
The Tor Project and Mullvad VPN have both announced collaboration on a privacy-oriented web browser. The joint browser, which is based on Firefox, has the features of the Tor Browser but operates over the Mullvad Virtual Private Network rather than Tor's onion routers. The collaboration has helped polish interface improvements and address several long standing issues.
Mullvad and the Tor Project have been part of the same community that is dedicated to developing technology that prioritizes protecting people's right to privacy for many years now. Mullvad contributes to the Tor Project at the highest level of membership, Shallot, and were a founding member of the Tor Project's Membership Program. They approached us to help them develop their browser because they wanted to leverage our expertise to create a product that is built on the same principles and with similar safety levels as the Tor Browser -- but that works independently of the Tor network. The result is the Mullvad Browser, a free, privacy-preserving web browser to challenge the all-too-prevalent business model of exploiting people's data for profit.
and
"The mass surveillance of today is absurd. Both from commercial actors like big tech companies and from governments," says Jan Jonsson, CEO at Mullvad VPN. "We want to free the internet from mass surveillance and a VPN alone is not enough to achieve privacy. From our perspective there has been a gap in the market for those who want to run a privacy-focused browser as good as the Tor Project's but with a VPN instead of the Tor Network."
Mullvad has been an active member of the Tor project for years.
Oh, and one more thing, speaking of VPNs, buried in the actual text of Senate Bill S.686 - RESTRICT Act 118th Congress (2023-2024), hidden behind rhetoric about ByteDance and Tiktok is a ban on VPN usage.
Previously:
(2023) The
'Insanely Broad' RESTRICT Act Could Ban VPNs in the USA
(2022) Are
Virtual Private Networks Actually Private?
(2022) VPN
Providers Remove Servers From India in Wake of New Data Collection
Laws...
21:00
Classic Film Camera Goes Digital With Game Boy Tech Hackaday

Despite having been technologically obsolete for a decade or two, analog photography is still practiced by hobbyists and artists to achieve a particular aesthetic. One might imagine a similar thing happening with early digital cameras, and indeed it has: the Game Boy Camera has seen use in dozens of projects. [Michael Fitzmayer] however decided to combine the worlds of analog and early digital photography by equipping a Holga with the image sensor from a Game Boy Camera.
20:36
Zstd 1.5.5 Released With Corruption Fix, Improved Performance In Some Scenarios Phoronix
Just two months after Zstd 1.5.4 was published, Zstd 1.5.5 has algorithm implementation. Zstd 1.5.5's release is motivated by addressing a rare corruption bug fix but also has various performance optimizations...
20:16
LLVM 16.0.1 Released With Many Compiler Fixes, Backports AMD Zen 4 Scheduler Model Phoronix
It's been two weeks already since the release of LLVM 16.0 as the latest shiny feature update to this widely-used, open-source compiler stack. LLVM release manager Tom Stellard today issued LLVM 16.0.1 as the first point release with a wide collection of fixes and other maintenance work to LLVM and its contained sub-projects...
20:00
MidnightBSD 3.0.1 Released With Security Fixes, rc.d Scripts Cleanup Phoronix
Building off last month's release of MidnightBSD 3.0 for this desktop-focused, FreeBSD-forked operating system the v3.0.1 update is now available...
19:15
Take-Two Dismisses Claims Against Lead Defendants in GTA Mods Lawsuit TorrentFreak
 In 2021, a group of Grand Theft Auto enthusiast programmers
released re3 and reVC, a pair of reverse-engineered modifications
for GTA 3 and Vice City.
In 2021, a group of Grand Theft Auto enthusiast programmers
released re3 and reVC, a pair of reverse-engineered modifications
for GTA 3 and Vice City.
These projects breathed new life into games that while still fantastic, benefited greatly from significant enhancements that helped to wind back the years. Fans loved re3 and reVC but Take-Two and Rockstar Games most definitely did not.
The companies first move was to file a DMCA notice that ordered GitHub to take the projects down. The programmers response came via a DMCA counternotice which restored their projects on GitHub but left them exposed to a potential legal response by Take-Two.
Take-Two Files Copyright Lawsuit
In September 2021, Take-Two filed a lawsuit against the programmers, claiming that the aim of the projects was to create and distribute pirated versions of GTA 3 and Vice City.
The companys claims included damages for willful and malicious copyright infringement due to the illegal copying, adaption and distribution of GTA source code and other protected content. For good measure, Take-Two also demanded damages for alleged misrepresentations in the defendants DMCA counternotices.
The lawsuit listed 14 defendants, just four of which were named: Angelo Papenhoff (aap), Theo Morra, Eray Orunus, and Adrian Graber. In their November 2021 answer to the complaint, the four men denied the copyright infringement allegations and cited fair use among other affirmative defenses.
One Year Later, Limited Visible Progress
The first five months of 2022 were relatively uneventful, at least based on information made available to the public. The parties did participate in an ADR (Alternative Dispute Resolution) session but according to the mediators report early May, the case did not settle.
No further entries appeared on the docket until December 2022, when the parties informed the court that since disclosure and discovery in the lawsuit was likely to involve the production of confidential, proprietary, or private information, special protection from public disclosure may be warranted. The court had no problem with granting the request.
As part of this process, Take-Two served an...
19:12
New Strain of Rorschach Ransomware Targeting US- Firms HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
Rorschach ransomware boasts advanced encryption technology and can spread automatically on the machine if executed on a domain controller.
This is a post from HackRead.com Read the original post: New Strain of Rorschach Ransomware Targeting US- Firms
18:35
Typhon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques The Hacker News
The threat actor behind the information-stealing malware known as Typhon Reborn has resurfaced with an updated version (V2) that packs in improved capabilities to evade detection and criminal underground for $59 per month, $360 per year, or alternatively, for $540 for a lifetime subscription. "The stealer can harvest and exfiltrate
18:22
Links 05/04/2023: Fentanylware (TikTok) Fined for Abuse and German Court Orders Takedown of Free Software (Youtube-dl) Techrights
![]()
Contents
- GNU/Linux
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Leftovers
- Gemini* and Gopher
-
GNU/Linux
-
Instructionals/Technical
-
Linux Handbook Special Variables in Bash Shell Scripting
Recently, I covered how you can use the number of arguments in bash that involved the use of the $# variable which is one of the special variables of bash.
-
University of Toronto Automated status tests need to have little or no noise
Unless youre in a bad situation, your systems are almost always working; your backups are happening properly, your mach...
-
-
18:17
STYX Marketplace emerged in Dark Web focused on Financial Fraud Security Affairs
Resecurity has recently identified the STYX Marketplace, a new cybercriminal e-commerce platform with a specialized focus on financial fraud and money laundering.
The STYX marketplace was launched at the beginning of 2023. This platform is specifically designed to facilitate financial crime, providing cybercriminals with a range of services, including stolen financial data, credit card information, forged documents, money laundering services, victim reconnaissance lookups, and more.
This discovery illustrates the post-pandemic menace of cyber-enabled financial crime and the threat it poses to financial institutions (FIs) and their customers.
The discovery of STYX coincides with Resecurity financial crime risk analysts observing a significant increase in threat actors offering money-laundering services that exploit digital banking and cryptocurrency accounts.
Cybercriminals have also started targeting new jurisdictions outside North America and the UK, including the United Arab Emirates and multiple countries in the European Union. The EU is where these types of threat actors typically set up merchant terminals and business bank accounts to facilitate money laundering in the form of cash-outs and bank drops. Typically, these tactics are used in the furtherance of online-banking account takeovers (ATOs) and credit card theft (carding), with commissions for successful cash-outs ranging from 40% to 70%.
Resecurity found that STYX has been operational for several months already, capturing a significant following in reputable c...
18:00
A NOR Gate For An ALU? Hackaday

If you know anything about he design of a CPU, youll probably be able to identify that a critical component of all CPUs is the Arithmetic Logic Unit, or ALU. This is a collection of gates that can do a selection of binary operations, and which depending on the capabilities of the computer, can be a complex component. Its a surprise then to find that a working CPU can be made with just a single NOR gate which is what is at the heart of [Dennis Kuschel]s My4th single board discrete logic computer. Its the latest in a series of machines from him using the NOR ALU technique, and it replaces hardware complexity with extra software to perform complex operations.
Aside from a refreshingly simple and understandable circuit, it has 32k of RAM and a 32k EPROM, of which about 9k is microcode and the rest program. Its called My4th because it has a Forth interpreter on board, and it has I2C and digital I/O as well as a serial port for its console.
This will never be a fast computer, but the fact that it computes at all is ts charm. In 2023 there are very few machines about that can be understood in their entirety, so this one is rather special even if its not the first 1-bit ALU weve seen.
Thanks [Ken Boak] for the tip.
17:34
IRC Proceedings: Tuesday, April 04, 2023 Techrights
Also available via the Gemini protocol at:
- gemini://gemini.techrights.org/irc-gmi/irc-log-techrights-040423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-040423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-social-040423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-techbytes-040423.gmi
Over HTTP:
|
... |
17:00
DISCOVERY Paleontologists Discover Fossil of Giant Extinct Eagle Terra Forming Terra
"Markets Will Always Outsmart The Best AI Systems That Our Computer Scientists Develop" Terra Forming Terra
Building material made with lemons and coconut could help heat a home Terra Forming Terra

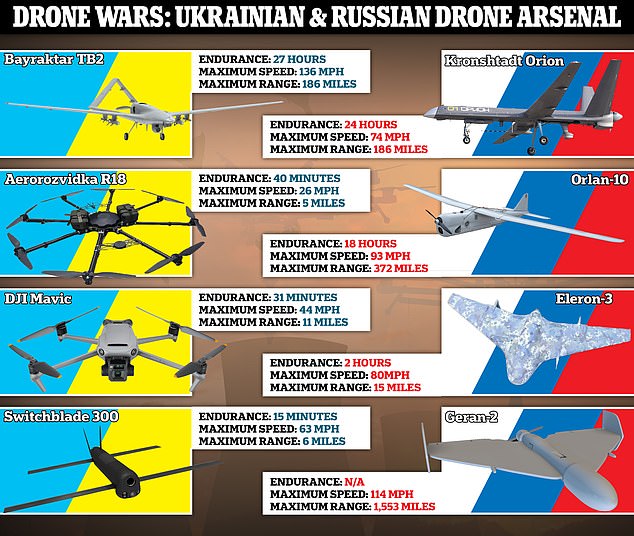
War of the drones Terra Forming Terra
16:35
Seattle Becomes First U.S. City to Permanently Require Sick Leave for Delivery and App-based Workers SoylentNews
The Seattle City Council today unanimously approved rules providing paid sick leave for food-delivery and other on-demand, app-based gig economy workers. The city appears to be the first in the nation to permanently ensure these protections.
[...] The measure applies to workers for companies such as DoorDash, Grubhub and Uber Eats, as well as platforms providing on-demand work such as laundry services and car washing. Similar benefits already exist at the state level for ride-hailing companies including Lyft and Uber. Seattle's legislation provides a suite of sick and "safe" time benefits including paid time off for:
- an illness and preventative health care;
- if a company stops operations due to a public health emergency or other safety reason;
- due to a school closure for a family member; and
- in order to seek services for domestic violence, sexual assault or stalking.
Mosqueda sponsored the legislation and was also the lead on similar, temporary protections put in place in June 2020 to aid workers during the COVID-19 pandemic. Mayor Bruce Harrell drafted the new legislation in partnership with the council and lauded passage of the measure, according to a statement.
Read more of this story at SoylentNews.
15:47
Techrights Plans for Impending Easter Weekend Techrights
Summary: Techrights will be publishing threatening letters from trolls this coming weekend; its well overdue
LAST summer a copyright troll targeted Techrights [1, 2] and for full disclosure purposes we planned to disclose the letters some time around Christmas. Transparency is important if not paramount. Just before Christmas, however, that troll escalated a little by sending physical letters to our home, so we decided to delay this until Easter when its quieter and theres ample time to redact and preapre.
regardless of whether theres something more sinister or complicated going on behind the scenes, expect more to be published around Easter Sunday.The case itself is without merit, very obviously frivolous harassment, which we suspect may have comes from the EPO or is linked to Team UPC, which also issued some copyright threats only months ago [1, 2]. Either way, regardless of whether theres something more sinister or complicated going on behind the scenes, expect more to be published around Easter Sunday.
Techrights still attracts such self-defeating threats. Shedding light on them helps deter/discourage further attempts. That these threats are made in the first place can be rather revealing at times. That means Techrights makes an impact. Last year we covered another example of this.
15:15
Links 05/04/2023: EasyOS 5.2.1 and Shotcut 23.04; Donald Trump in Police Custody Techrights
![]()
Contents
- GNU/Linux
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Leftovers
- Gemini* and Gopher
-
GNU/Linux
-
GamingOnLinux ...
-
15:00
Upgrade Your Voodoo with More Memory Hackaday

In 1996, the 3Dfx VooDoo VGA chipset changed computer graphics forever. Because of the high cost of memory, most of the boards had only 4 MB of memory which seemed a lot back then. However, the chipset could actually handle up to 8 MB. [Bits and Bolts] couldnt stand that his board only had 4 MB, so he did what any good hacker would do: he figured out how to add the missing memory!
The mod has been done before using the piggyback technique, where you solder the new RAM chips on the old chips and bend out a few pins out to directly wire them to chip selects elsewhere on the board. [Bits and Bolts] didnt want to try that, so instead, he developed a PCB that slips over the chip using a socket.
Of course, this presumes the chips have enough clearance between them to fit the sockets. In addition, the board is pretty specific to a particular VGA board because each board has different memory chip layouts. The sockets also had plastic support structures that blocked the insertion, so a little surgery removed them.
The board can add more memory to either the frame buffer or the texture mapping memory. There are jumpers to set up, which you want to do.
While weve seen piggybacking done a few times weve even done it ourselves we havent thought of using a socket instead of just soldering on top of the memory. You still have to do the tiny soldering to graft the chip select, but th...
14:30
How AI is transforming cybersecurity for better and worse Help Net Security
Many sectors view AI and machine learning with mixed emotions, but for the cybersecurity industry, they present a double-edged sword. On the one hand, AI provides powerful tools for cybersecurity professionals, such as automated security processing and threat detection. On the other hand, cybercriminals have access to the same technology, making it a constant cat-and-mouse game between attackers and defenders. In this Help Net Security video, Matt Aldridge, Principal Solutions Consultant at OpenText Cyber Security, More
The post How AI is transforming cybersecurity for better and worse appeared first on Help Net Security.
14:00
Stop online counterfeiters dead in their tracks Help Net Security
During this Help Net Security interview, Nicole Hofmann, CEO at Sentryc, delves into the critical issue of counterfeiting and the detrimental impact it has on industries and brands. Hofmann sheds light on the modus operandi of counterfeiters, who operate with impunity on online marketplaces and digital sales channels, luring unsuspecting customers into purchasing fake products. Hofmann also highlights the crucial role of self-learning software in identifying and removing counterfeit products from online marketplaces, a crucial More
The post Stop online counterfeiters dead in their tracks appeared first on Help Net Security.
13:52
Ads Are Coming for the Bing AI Chatbot, as They Come for All Microsoft Products SoylentNews
Microsoft has spent a lot of time and energy over the last few months adding generative AI features to all its products, particularly its long-standing, long-struggling Bing search engine. And now the company is working on fusing this fast-moving, sometimes unsettling new technology with some old headaches: ads.
In a blog post earlier this week, Microsoft VP Yusuf Mehdi said the company was "exploring placing ads in the chat experience," one of several things the company is doing "to share the ad revenue with partners whose content contributed to the chat response." The company is also looking into ways to let Bing Chat show sources for its work, sort of like the ways Google, Bing, and other search engines display a source link below snippets of information they think might answer the question you asked.
Related:
Even the
FBI Says You Should Use an Ad Blocker (20221227)
Microsoft
Explores a Potentially Risky New Market (20220420)
Microsoft
is Testing Ads in the Windows 11 File Explorer (20220314)
Sen. Ron
Wyden Calls for an Investigation of the Ad-Blocking Industry
(20200115)
Windows 10
App Starts Showing Ads, Microsoft Says You Can't Remove Them
(20191215)
Microsoft
Experiments with Ads in Windows Email (20181117)
Read more of this story at SoylentNews.
13:30
The high cost of insecure authentication methods Help Net Security
Insecure authentication is a primary cause of cyber breaches, and that cumbersome login methods take an unacceptable toll on employees and business productivity, according to HYPR. Respondents indicate that a passwordless approach would increase productivity (45%), improve user experience (86%), strengthen security (86%) and accelerate adoption of multi-factor authentication (42%). Insecure authentication methods still in use The report findings make it evident that maintaining the status quo is a risky proposition all around, said Bojan More
The post The high cost of insecure authentication methods appeared first on Help Net Security.
13:00
Re-evaluating immature and ineffective insider risk management programs Help Net Security
Managing insider risk is becoming increasingly difficult. In fact, insider risk is emerging as one of the most challenging threats to detect, mitigate and manage, according to Code42. Although more than 72% of companies indicate they have an Insider Risk Management (IRM) program in place, the same companies experienced a year-over-year increase in data loss incidents of 32%, and 71% expect data loss from insider events to increase in the next 12 months. With insider More
The post Re-evaluating immature and ineffective insider risk management programs appeared first on Help Net Security.
12:20
F5 protects digital services with AI-powered app and API security capabilities Help Net Security
F5 has unveiled new security capabilities to give customers comprehensive protection and control in managing apps and APIs across on-premises, cloud, and edge locations. Specifically, new machine learning enhancements provide F5s cloud security portfolio with advanced API endpoint discovery, anomaly detection, telemetry, and behavioral analysis. As more transactions and customer engagements occur through digital channels such as web and mobile apps, organizations are seeking better solutions to provide secure experiences for their end users and More
The post F5 protects digital services with AI-powered app and API security capabilities appeared first on Help Net Security.
12:16
Troubleshooting Linux performance, building a golden image for your RHEL homelab, and more tips for sysadmins Linux.com
Check out Enable Sysadmins top 10 articles from March 2023.
Read More at Enable Sysadmin
The post Troubleshooting Linux performance, building a golden image for your RHEL homelab, and more tips for sysadmins appeared first on Linux.com.
12:10
Akamai introduces new premium offering and updated managed security service program Help Net Security
Akamai introduced an updated managed security service program and premium service offerings. The new capabilities are intended to help customers protect their businesses 247 from the most sophisticated attacks with proactive monitoring and rapid response in the event of a cyberattack. Customers can take advantage of access to more Akamai security experts, reduced pricing, and more available for customers seeking personalized support and prioritized More
The post Akamai introduces new premium offering and updated managed security service program appeared first on Help Net Security.
12:00
Reshoring Vacuum Tube Manufacturing, One Tube at a Time Hackaday

For most of us, vacuum tubes havent appeared in any of our schematics or BOMs in well, ever. Once mass-manufacturing made reliable transistors cheap enough for hobbyists, vacuum tubes became pretty passe, and it wasnt long before the once mighty US tube industry was decimated, leaving the few remaining tube enthusiasts to ferret out caches of old stock, or even seek new tubes from overseas manufacturers.
However, all that may change if [Charles Whitener] succeeds in reshoring at least part of the US vacuum tube manufacturing base. He seems to have made a good start, having purchased the Western Electric brand from AT&T and some of its remaining vacuum tube manufacturing equipment back in 1995. Since then, he has been on a talent hunt, locating as many people as possible who have experience in the tube business to help him gear back up.
The new Western Electric, now located in Rossville, Georgia, is currently manufacturing 300B power triodes and marketing them as a premium product aimed primarily at the audiophile market. A matched pair of tubes in a cherry wood pr...
11:39
[Meme] Unitary Patent and Unified Patent Court (UPC): Doing a Putin on European Patent Courts Techrights
Summary: Desperate to overcome legal barriers (i.e. to break the law) and impose European software patents on the whole of the EU, Benot Battistelli and Antnio Campinos have worked to dismantle European patent courts, replacing them with an organ that the EPO controls and can compel to hide the surging invalidity rates (at the expense of the EUs credibility and reputation; remember that the EPO is partly outsourced to Belarus)
11:25
Union Syndicale Fdrale (USF) Takes a Closer Look at the EPO and Worsening Staff Conditions in a Series of New Articles Techrights
Agora has devoted a lot of space to the matter
Summary: Last month Union Syndicale Fdrale spoke out in support of EPO workers who have felt besieged and abused by Benot Battistelli and Antnio Campinos since 2010; below one can find a new batch of articles related to the matter
-
Precarity at the European Patent Office
Due to the highly specific technical and legal skills requested from the majority of staff at the EPO, it has long been considered that fixed-term contracts were not the appropriate form of employment for this Office. The need of a lengthy and thorough training of new employees is a condition sine qua non to grant quality patents. This necessary time and resources investment could be lost for the organisation if fixed-term contracts were the norm, let alone the knowledge accumulated and shared by the newly recruited staff. Furthermore, at the individual level, a Golden Cage Syndrome exists at the EPO, since after some years of employment, staff tend to specialise in the field of patents and lose their general expertise. The expertise in the field of patents is not easily recognised in other fields. Staff leaving the EPO after some years of employment could find it very difficult to find employment elsewhere at comparable conditions. These considerations were valid in the past and are still valid today.
-
Social Security at the EPO: an overview
The EPO, the second largest European organisation after the Commission in terms of the number of employees, is a substantially independent body, which is neither part of the European Union nor attached to it in any way like the EU agencies. Its member states include the 27 EU member states, but also 11 non-EU states. It is also not one of the Coordinated Organisations, although some...
11:06
Scientists Capture Deepest-Ever Footage of a Fish SoylentNews
Researchers using baited camera traps recorded an unknown species of snailfish more than 5 miles (8 kilometers) deep just off the coast of Japan. These are the deepest fish ever caught on film.
A team with the Tokyo University of Marine Science and Technology and the University of Western Australia recently released the footage, which was collected in September 2022 in the Izu-Ogasawara Trench, which is just south of Japan. Cameras captured the unknown snailfish that belongs to the genus Pseudoliparis at 8,336 meters (5.1 miles) underwater, according to a press release from the University of Western Australia.
[...] The snailfish found in the Izu-Ogasaware Trench do not have any scales. They're covered in a gelatinous layer and do not have a swim bladder like other fish species do, The Guardian reports. This allows them to live under the extreme pressure found in the deepest parts of the ocean.
The expedition was part of a 10-year study into the deepest fish population on the planet. Researchers set out to study the Izu-Ogasaware, Ryukyu, and Japan trenchesall of which are over 7,000 meters (4.3 miles) deep. According to researchers, the recently released images show how different the Pacific Ocean's trenches are to others around the world. Alan Jamieson, a chief scientist in the expedition, explained in the UWA release that, in the Mariana Trench, the deeper researchers look, the less fish there are. But in the trenches around Japan, there are a lot of fish to be found even at extreme depths.
Read more of this story at SoylentNews.
11:00
Microsoft Layoffs Now in Bay Area (California) Techrights
Summary: Everyone seems to be talking about Apple layoffs this week, but 6 hours ago it was said that Microsoft [et al] have revealed plans for fresh Bay Area job cuts, together adding hundreds of workers to the regions worsening layoffs.
11:00
IBM unveils new options to help clients reach their sustainability goals Help Net Security
IBM has unveiled new single frame and rack mount configurations of IBM z16 and IBM LinuxONE 4, expanding their capabilities to a broader range of data center environments. Based on IBMs Telum processor, the new options are designed with sustainability in mind for highly efficient data centers, helping clients adapt to a digitized economy and ongoing global uncertainty. Introduced in April 2022, the IBM z16 multi frame has helped transform industries with real-time AI inferencing More
The post IBM unveils new options to help clients reach their sustainability goals appeared first on Help Net Security.
10:45
Desktop/Laptop Operating System Market Share in Ukraine: Windows Down From 90% to 82% in One Year Techrights
The latest on Ukraine (OS battle)
Summary: Microsofts invasion of Ukraine is not working anymore; GNU/Linux is growing there (not counting Android and ChromeOS, which arent freedom-respecting but run Linux), threatening Microsofts monopoly rents
10:25
How to Teach Your Child Coding: A Gift for Their Digital Future HackRead | Latest Cybersecurity and Hacking News Site
By Owais Sultan
Let's code, kids!
This is a post from HackRead.com Read the original post: How to Teach Your Child Coding: A Gift for Their Digital Future
10:13
NEW 'Off The Wall' ONLINE 2600 - 2600: The Hacker Quarterly
NEW 'Off The Wall' ONLINE
Posted 05 Apr, 2023 0:13:30 UTC
The new edition of Off The Wall from 04/04/2023 has been archived and is now available online.
10:00
HPR3828: The Oh No! News. Hacker Public Radio
The Oh No! news. Oh No! News is Good News. Threat analysis; your attack surface. Article: CISA warns of actively exploited Plex bug after LastPass breach. Author: Sergiu Gatlan (2023, Mar 11). Attackers with "admin access to a Plex Media Server could abuse the Camera Upload feature to make the server execute malicious code," according to an advisory published by the Plex Security Team in May 2020 when it patched the bug with the release of Plex Media Server 1.19.3. "This could be done by setting the server data directory to overlap with the content location for a library on which Camera Upload was enabled. This issue could not be exploited without first gaining access to the server's Plex account." Link to Cybersecurity & Infrastructure Security Agency (CISA). Supporting Article: Plex Security, regarding security vulnerability CVE-2020-5741. Author: PlexSecurity, Plex Employee. (2020, May). We have recently been made aware of a security vulnerability related to Plex Media Server. This issue allowed an attacker with access to the server administrator’s Plex account to upload a malicious file via the Camera Upload feature and have the media server execute it. Supporting Article: Official statement from Plex, concerning vulnerabilities, on LastPass Data Breach. Author: PlexInfo, Plex Employee. (2023, Feb 28). "We have not been contacted by LastPass so we cannot speak to the specifics of their incident. We take security issues very seriously, and frequently work with external parties who report issues big or small using our guidelines and bug bounty program. When vulnerabilities are reported following responsible disclosure we address them swiftly and thoroughly, and we’ve never had a critical vulnerability published for which there wasn’t already a of our own, we’ve always chosen to communicate them quickly. We are not aware of any unpatched vulnerabilities, and as always, we invite people to disclose issues to us following the guidelines linked above. Given recent articles about the LastPass incident, although we are not aware of any unpatched vulnerabilities, we have reached out to LastPass to be sure." Supporting Article: LastPass says employee’s home computer was hacked and corporate vault taken. Author: Dan Goodin. (2023, Feb 27). According to a person briefed on a private report from LastPass who spoke on the condition of anonymity, the media software package that was exploited on the employee’s home computer was Plex. Interestingly, Plex rep
Transgender Careers in the Software Industry It Will Never Work in Theory
If the true measure of a society is how it treats its weakest members, the true measure of a profession is how much it does to protect them. Software engineering does poorly by that standard: despite decades of hand-wringing, women and some racialized minorities are still often made to feel unwelcome, and programmers continue to build systems that codify discrimination against them.
This recent paper looks at the experiences of transgender people in our industry. They are still frequently discriminated against, but many find programming to be a safer career than other options, in part because of its early and widespread adoption of remote work. With far-right politicians in the United States and elsewhere stirring up transphobic hysteria, work like this helps us see where we are and how far we have to go.
If you'd like to know more, please watch this moving talk by Naomi Ceder.
Ronnie de Souza Santos, Brody Stuart-Verner, and Cleyton Magalhes. What do transgender software professionals say about a career in the software industry? IEEE Software, pages 16, 2023. doi:10.1109/ms.2023.3257743.
Diversity is an essential aspect of software development because technology influences almost every aspect of modern society, and if the software industry lacks diversity, software products might unintentionally constrain groups of individuals instead of promoting an equalitarian experience to all. In this study, we investigate the perspectives of transgender software professionals about a career in software engineering as one of the aspects of diversity in the software industry. Our findings demonstrate that, on the one hand, trans people choose careers in software engineering for two primary reasons: a) even though software development environments are not exempt from discrimination, the software industry is safer than other industries for transgenders; b) trans people occasionally have to deal with gender dysphoria, anxiety, and fear of judgment, and the work flexibility offered by software companies allow them to cope with these issues more efficiently.
09:46
Rilide Malware New Crypto Stealer Hits Chromium-Based Browsers HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
The Chromium-based browsers include Google Chrome, Microsoft Edge, Brave, Opera, Vivaldi, and several others.
This is a post from HackRead.com Read the original post: Rilide Malware New Crypto Stealer Hits Chromium-Based Browsers
09:13
Behind the scenes of running Linux kernel Mentorship Programs Linux.com

Read the original blog at Read More
The post Behind the scenes of running Linux kernel Mentorship Programs appeared first on Linux.com.
08:21
Firefox Will Support Windows 7/8 Until at Least 2024 SoylentNews
Mozilla won't abandon Microsoft's tried and tested platform anytime soon:
The Extended Support Release (ESR) of Firefox will keep supporting Windows 7 and Windows 8.1 until at least until 2024. Mozilla programmer Mike Kaply confirmed the decision through the Bugzilla platform, stating that the corporation "will not be ending support for Windows 7/Windows 8 before the release of the Firefox 115 ESR," and that the Firefox 115 ESR release will support the aged operating systems "at least until 3Q 2024."
Mike Kaply also hinted at the fact that Mozilla still has to decide exactly when support for Windows 7/8 will be finally removed. Firefox ESR is stable release of the open-source browser which Mozilla supports for an extended period of time compared to regular, "rapid" releases coming out every month. During its incremental updates containing security fixes with no new features or performance enhancements.
As stated by Firefox's official release calendar, Firefox 115 ESR should come out on July 4, 2023. The Firefox Public Data Report also reveals that Windows 7 still provides a sizable portion of the overall Firefox userbase (13.44%), while Windows 10 is the leading platform with 71% of users. The much-maligned Windows 8.1 is still used by 2.3% of Firefox installations.
[...] Windows 7 was already abandoned by Google Chrome (and other Chromium-based browsers), which doesn't run on the OS anymore starting from Chrome 110. Microsoft ended support for Windows 7 and Windows 8 in January 2023, and Valve will do the same with Steam on January 1, 2024.
Are you one of the 13.44%?
Read more of this story at SoylentNews.
08:17
Enough is Enough. Tell Congress to Ban Federal Use of Face Recognition Deeplinks
Cities and counties across the country have banned government use of face surveillance technology, and many more are weighing proposals to do so. From Boston to San Francisco, Jackson, Mississippi to Minneapolis, elected officials and activists know that face surveillance gives police the power to track us wherever we go. It also disproportionately impacts people of color, turns us all into perpetual suspects, increases the likelihood of being falsely arrested, and chills peoples willingness to participate in first amendment protected activities. Even Amazon, known for operating one of the largest video surveillance networks in the history of the world, extended its moratorium on selling face recognition to police.
Now, Congress must do its part. Weve
created a
campaign that will easily allow you to
contact your elected federal officials and tell them to support
the
Facial R...
07:20
Chrome 112 Released With WASM Garbage Collection Trial, CSS Nesting Phoronix
Google today promoted the Chrome 112 web browser to their stable channel on all supported platforms...
07:04
FBI Seizes Bot Shop Genesis Market Amid Arrests Targeting Operators, Suppliers Krebs on Security
Several domain names tied to Genesis Market, a bustling cybercrime store that sold access to passwords and other data stolen from millions of computers infected with malicious software, were seized by the Federal Bureau of Investigation (FBI) today. The domain seizures coincided with more than a hundred arrests in the United States and abroad targeting those who allegedly operated the service, as well as suppliers who continuously fed Genesis Market with freshly-stolen data.

Several websites tied to the cybercrime store Genesis Market had their homepages changed today to this seizure notice.
Active since 2018, Genesis Markets slogan was, Our store sells bots with logs, cookies, and their real fingerprints. Customers could search for infected systems with a variety of options, including by Internet address or by specific domain names associated with stolen credentials.
But earlier today, multiple domains associated with Genesis had their homepages replaced with a seizure notice from the FBI, which said the domains were seized pursuant to a warrant issued by the U.S. District Court for the Eastern District of Wisconsin.
The U.S. Attorneys Office for the Eastern District of Wisconsin did not respond to requests for comment. The FBI declined to comment.
Update, April 5, 11:40 a.m. ET: The U.S. Department of Justice just released a statement on its investigation into Genesis Market. In a press briefing this morning, FBI and DOJ officials said the international law enforcement investigation involved 14 countries and resulted in 400 law enforcement actions, including 119 arrests and 208 searches and interviews worldwide. The FBI confirmed that some American suspects are among those arrested, although officials declined to share more details on the arrests.
The DOJ said investigators were able to access the user database for Genesis Market, and found the invite-only service had more than 59,000 registered users. The database contained the purchase and activity history on all users, which the feds say helped them uncover the true identities of many users.
Original story: But sources close to the investigation tell KrebsOnSecurity that law enforcement agencies in the United States, Canada and across Europe are current...
06:55
RADV Lands Shader Caching For Graphics Pipeline Libraries Phoronix
Ahead of hopefully enabling the RADV Vulkan Graphics Pipeline Libraries "GPL" support by default for this quarter's Mesa 23.1 release, the RADV driver has now landed on-disk shader caching support for GPL libraries...
06:41
ALPHV/BlackCat ransomware affiliate targets Veritas Backup solution bugs Security Affairs
An ALPHV/BlackCat ransomware affiliate was spotted exploiting vulnerabilities in the Veritas Backup solution.
An affiliate of the ALPHV/BlackCat ransomware gang, tracked as UNC4466, was observed exploiting three vulnerabilities in the Veritas Backup solution to gain initial access to the target network.
Unlike other ALPHV affiliates, UNC4466 doesnt rely on stolen credentials for initial access to victim environments. Mandiant researchers first observed this affiliate targeting Veritas issues in the wild on October 22, 2022. Below is the list of flaws exploited by the ransomware gangs affiliate:
- CVE-2021-27876: The communication between a client and an Agent requires successful authentication, which is typically completed over a secure TLS communication. However, due to a vulnerability in the SHA Authentication scheme, an attacker is able to gain unauthorized access and complete the authentication process. Subsequently, the client can execute data management protocol commands on the authenticated connection. By using crafted input parameters in one of these commands, an attacker can access an arbitrary file on the system using System privileges.. (CVSS score: 8.1).
- CVE-2021-27877: An issue was discovered in Veritas Backup Exec before 21.2. It supports multiple authentication schemes: SHA authentication is one of these. This authentication scheme is no longer used in current versions of the product, but hadnt yet been disabled. An attacker could remotely exploit this scheme to gain unauthorized access to an Agent and execute privileged commands. (CVSS score: 8.2).
- CVE-2021-27878: An issue was discovered in Veritas Backup Exec before 21.2. The communication between a client and an Agent requires successful authentication, which is typically completed over a secure TLS communication. However, due to a vulnerability in the SHA Authentication scheme, an attacker is able to gain unauthorized access and complete the authentication process. Subsequently, the client can execute data management protocol commands on the authenticated connection. The attacker could use one of these commands to execute an arbitrary command on the system using system privileges. (CVSS score: 8.8)
The three flaws were addressed with the release of version 21.2 in March 2021, but many public-facing endpoints are yet to be updated. The researchers identified over 8,500 installations of Veritas Backup Exec instan...
06:27
Smart Locks Endanger Tenants Privacy and Should Be Regulated Deeplinks
The growing deployment of smart locks in apartments, often installed without tenants permission, has created a new stream of sensitive location data for law enforcement, landlords, and private companies. Tenants should not be forced to submit to tracking just to enter their home. At minimum, we need privacy laws that require consent to collect this data, a warrant for police access, and strong data minimization.
Smart locks come in many forms. At the most basic level, they are physical locks that can be opened with a nontraditional key like a smartphone or fingerprint. Most significantly from a privacy perspective, they allow the lock company (and sometimes landlords) to collect data each time you or any of your guests unlock your physical door. To do this, the locks themselves may be connected to the internet, or they can rely on an app you must install on your phone (the key) to transmit the data to the lock companys servers. Depending on the model, the lock might also record other datalike an image of the person trying to unlock the door.
Smart locks have become increasingly popular in recent years, specifically with landlords. For example, in 2019, tenants in New York City forced a settlement after a landlord attempted to require tenants to use smart locks. The settlement required an option for physical keys. The smart lock at issue in that case was made by a company called Latch. While Latch was not named in the lawsuit, the company changed its privacy policy to remove reference to marketing and collection of other location data. Its software is reportedly in more than 125,000 dwelling units or commercial spaces. Many other companies make smart locks as well. They are part of the growth of smart home devices.
Privacy risks from smart locks
Despite their convenience to some people, smart locks can create a revealing data trail that raises concerns about law enforcement power, data privacy, and information security.
This data could give law enforcement a powerful new stream of data to be obtained without your knowledge. Companies tend to store this kind of data for much longer than necessary, and it i...
05:50
[$] Mobian: bringing Debian to mobile devices LWN.net
Mobian is a project that aims to bring the Debian distribution to mobile devices such as smartphones and tablets. By building on the flexibility, stability, and community-driven development of Debian, Mobian aspires to create a powerful and user-friendly alternative to existing mobile operating systems. The project is actively working on reducing the delta between Mobian and Debian, and its ultimate goal is to be absorbed back into its parent distribution and to make it easy to run Debian on mobile devices.
05:36
BuzzFeed is Quietly Publishing Whole AI-Generated Articles, Not Just Quizzes SoylentNews
These read like a proof of concept for replacing human writers:
Earlier this year, when BuzzFeed announced plans to start publishing AI-assisted content, its CEO Jonah Peretti promised the tech would be held to a high standard.
"I think that there are two paths for AI in digital media," Peretti told CNN. "One path is the obvious path that a lot of people will do but it's a depressing path using the technology for cost savings and spamming out a bunch of SEO articles that are lower quality than what a journalist could do, but a tenth of the cost."
[...] Indeed, the first AI content BuzzFeed published a series of quizzes that turned user input into customized responses were an interesting experiment, avoiding many of the missteps that other publishers have made with the tech.
It doesn't seem like that commitment to quality has held up, though. This month, we noticed that with none of the fanfare of Peretti's multiple interviews about the quizzes, BuzzFeed quietly started publishing fully AI-generated articles that are produced by non-editorial staff and they sound a lot like the content mill model that Peretti had promised to avoid.
[...] A BuzzFeed spokesperson told us that the AI-generated pieces are part of an "experiment" the company is doing to see how well its AI writing assistance incorporates statements from non-writers.
The linked article includes many laughable examples of bland and similar phrases in multiple stories published on the site.
Previously: BuzzFeed Preps AI-Written Content While CNET Fumbles
Read more of this story at SoylentNews.
04:35
The Decades of Evidence That Antidepressants Cause Mass Shootings cryptogon.com
Via: The Forgotten Side of Medicine: Prior to the Covid vaccinations, psychiatric medications were the mass-prescribed medication that had the worst risk-to-benefit ratio on the market. In addition to rarely providing benefits to patients, there is a wide range of severe complications that commonly result from psychiatric medications. There are many serious issues with []
04:00
CentOS Hyperscale SIG Now Has An Intel-Optimized Repository Phoronix
The CentOS Hyperscale special interest group that is focused on providing new packages and features atop CentOS Stream for use by hyperscalers like Meta and Twitter have now established a "hyperscale-intel" repository for Intel-optimized packages...
03:50
Live: Trump Circus in New York cryptogon.com
Via: Al Jazeera:
03:47
Finland Joins NATO cryptogon.com
Via: Reuters: Finland formally joined NATO on Tuesday, its flag unfurling outside the military blocs Brussels headquarters, in a historic policy shift brought on by Russias invasion of Ukraine, drawing a threat from Moscow of counter-measures. Finlands accession, ending seven decades of military non-alignment, roughly doubles the length of the border that the North Atlantic []
03:47
Rorschach ransomware has the fastest file-encrypting routine to date Security Affairs
A new ransomware strain named Rorschach ransomware supports the fastest file-encrypting routine observed to date.
Check Point Research (CPR) and Check Point Incident Response Team (CPIRT) researchers detected a previously unknown ransomware strain, dubbed Rorschach ransomware, that was employed in attack against a US-based company.
The experts pointed out that the Rorschach ransomware appears to be unique. According to the report published by Check Point, Rorschach is one of the fastest ransomware observed to date.
The researchers conducted five separate encryption speed tests in a controlled environment (with 6 CPUs, 8192MB RAM, SSD, and 220000 files to be encrypted), limited to local drive encryption only. Below are the results of the tests:
| Ransomware | Average approximate time of encryption |
| LockBit v.3 | 7 minutes |
| Rorschach | 4 minutes, 30 seconds |
It turned out that we have a new speed demon in town. Whats
even more noteworthy is that the Rorschach ransomware is highly
customizable. By adjusting the number of encryption threads via the
command line argument --thread, it can achieve
even faster times. reads the
analysis published by CheckPoint.
It turned out that we have a new speed demon in town. Whats even
more noteworthy is that the Rorschach ransomware is highly
customizable. By adjusting the number of encryption threads via the
command line argument --thread, it can achieve
even faster times.
The malware is highly customizable and contains unique functions, such as the use of direct syscalls.
Attackers use DLL side-loading of a Cortex XDR Dump Service Tool, a signed commercial security product, to deploy the ransomware.
The Rorschach ransomware uses the following files:
- cy.exe Cortex XDR Dump Service
- winutils.dll Packed Rorschach loader and injector, used to decrypt and inject the ransomware.
- config.ini Encrypted Rorschach ransomware which contains all the logic and configuration.
Upon execution of cy.exe, due to DLL side-loading, the loader/injector winutils.dll is loaded into memory and runs in the context of cy.exe. The main Rorschach payload config.ini is subsequently loaded into memory as well, decrypted and injected into notepad.exe, where the ransomware logic begins. continues the...
03:34
Robert Maxwell Goes to Texas: The Story of Bluebonnet cryptogon.com
Via: Unlimited Hangout: Understanding Bluebonnet requires unpacking a tangled and diffuse web of fraudsters, intelligence assets, bankers and real estate developers who together rampaged across Texas and surrounding states during the mid-1980s, bilking and crashing a near-limitless number of thrifts and related lending institutions in a then-unprecedented spree of brazen financial crime. Much of this []
03:27
Genetic analysis tool developed to improve cancer modeling Lifeboat News: The Blog
Lifestyle behaviors such as eating well and exercising can be significant factors in ones overall health. But the risk of developing cancer is predominantly at the whim of an individuals genetics.
Our bodies are constantly making copies of our genes to produce new cells. However, there are occasional mistakes in those copies, a phenomenon geneticists call mutation. In some cases, these mistakes can alter proteins, fuse genes and change how much a gene gets copied, ultimately impacting a persons risk of developing cancer. Scientists can better understand the impact of mutations by developing predictive models for tumor activity.
Christopher Plaisier, an assistant professor of biomedical engineering in the Ira A. Fulton Schools of Engineering at Arizona State University, is developing a software tool called OncoMerge that uses genetic data to improve cancer modeling technology.
03:27
Serotonin gates the transfer of visual information from the eyes to the thalamus Lifeboat News: The Blog
Humans are known to perceive the environment around them differently based on the situation they are in and their own feelings and sensations. Internal states, such as fear, arousal or hunger can thus affect the ways in which sensory information is processed and registered by the brain.
Researchers at Beth Israel Deaconess Medical Center, Boston Childrens Hospital, and Peking University have recently carried out a study investigating the possible effects of serotonin, a neurotransmitter known to regulate sleep, mood, sexual desire, and other inner states, in the processing of visual information. Their findings, published in Neuron, suggest that serotonergic neurons in the brainstem (i.e., the central trunk of the mammalian brain) gate the transfer of visual information from the eyes to the thalamus, an egg-shaped area of the brain.
Internal states are known to affect sensory perception and processing, but this was generally thought to occur in the cortex or thalamus, Chinfei Chen, one of the researchers who carried out the study, told Medical Xpress. One of our previous studies revealed that arousal can suppress certain visual information channels at an earlier stage of the visual pathwayat the connection between the mouse retina and the thalamus, before the information even reaches the brain. This form of filtering of information suggests a very efficient means of processing only relevant information.
03:26
03:26
Scientists find deepest fish ever recorded at 8,300 metres underwater near Japan Lifeboat News: The Blog
Footage of unknown snailfish captured by researchers from Western Australia and Tokyo in Izu-Ogasawara trench.
03:25
A new mitochondrial theory of Alzheimers deserves serious attention Lifeboat News: The Blog
A grand unifying theory of brain ageing suggests malfunctioning mitochondria might be to blame for Alzheimers and other brain conditions. And this new avenue of exploration already has some potential therapies at the ready.
03:25
Room-Temperature Superconductor Discovery Meets With Resistance Lifeboat News: The Blog
A paper in Nature reports the discovery of a superconductor that operates at room temperatures and near-room pressures. The claim has divided the research community.
03:22
Why Are Many Technology Leaders Calling For An AI Halt? Lifeboat News: The Blog
An open letter signed by more than 1,100 technology and business industry leaders calls for a six-month moratorium on the race to develop artificial intelligence (AI), and in particular large language models like ChatGPT-4.
ChatGPT-4 is an example of AI exhibiting human-competitive intelligence and poses a risk to humanity without managed care.
03:11
The Broad, Vague RESTRICT Act is a Dangerous Substitute for Comprehensive Data Privacy Legislation Deeplinks
The recently introduced RESTRICT Act (S. 686, Sen. Warner and Sen. Thune) rightfully is causing a lot of concern. This bill is being called a TikTok ban, but its more complicated than that. As we wrote in our initial review of the bill, the RESTRICT Act would authorize the executive branch to block transactions and holdings of foreign adversaries that involve information and communication technology and create undue or unacceptable risk to national security and more.
We've explained our opposition to the RESTRICT Act
and urged everyone who agrees to take action against it. But we've
also been asked to address some of the concerns raised by others.
We do that here in this post.
At its core, RESTRICT would exempt certain information services from the federal statute, known as the Berman Amendments, which protects the free flow of information in and out of the United States and supports the fundamental freedom of expression and human rights concerns. RESTRICT would give more power to the executive branch and remove many of the commonsense restrictions that exist under the Foreign Intelligence Services Act (FISA) and the aforementioned Berman Amendments.
But S. 686 also would do a lot more.
EFF opposes the bill, and encourages you to reach out to your representatives to ask them not to pass it. Our reasons for opposition are primarily that this bill is being used as a cudgel to protect data from foreign adversaries, but under our current data privacy laws, there are many domestic adversaries engaged in manipulative and invasive data collection as well. Separately, handing relatively unchecked power over to the executive branch to make determinations about what sort of information technologies and technology services are allowed to enter the U.S. is dangerous. If Congress is concerned about foreign powers collecting our data, it should focus on comprehensive consumer data privacy legislation that will have a real impact, and protect our data no matter what platform its onTikTok, Facebook, Twitter, or anywhere else that profits from our private information. Thats why EFF supports...
03:01
Links 04/04/2023: Apple Layoffs and Clown Computing Crunch Techrights
![]()
Contents
-
GNU/Linux
-
Server
-
The Next Platform Cloud Spending Curtailed, On Premises Spending Heading Into Recession
The central bankers of the world want to curb inflation by putting a serious crimp in demand, and it looks like they may get what they want sort of in 2023 when it comes to datacenter infrastructure.
-
-
Audiocasts/Shows
-
Bryan Lunduke The Lundu...
-
-
03:00
Supercon 2022: Chris Combs Reveals His Art-World Compatibility Layer Hackaday

[Chris Combs] is a full time artist who loves using technology to create unique art projects and has been building blinky artwork since about a decade now. In his 2022 Supercon talk Art-World Compatibility Layer: How to Hang and Sell Your Blinky Goodness as Art (Slides, PDF), [Chris] takes us behind the scenes and shows us how to turn our blinky doodads in to coveted art works. There is a big difference between a project that just works, and a work of art, and its the att...
02:54
FTC Chair Refused Musk's Meeting Request, Told Him to Stop Delaying Investigation SoylentNews
Twitter owner Elon Musk requested a meeting with Federal Trade Commission Chair Lina Khan late last year, but he was rebuffed and told to stop dragging his heels on providing documents and depositions needed for the FTC investigation into Twitter's privacy and data practices, a New York Times report said yesterday.
"In a Jan. 27 letter declining the meeting, Ms. Khan told a Twitter lawyer to focus on complying with investigators' demands for information before she would consider meeting with Mr. Musk," the NYT wrote.
Twitter has to comply with conditions in a May 2022 settlement in which it agreed to pay a $150 million penalty for targeting ads at users with phone numbers and email addresses collected from those users when they enabled two-factor authentication. Last year's settlement was reached after the FTC said Twitter violated the terms of a 2011 settlement that prohibited the company from misrepresenting its privacy and security practices.
Related:
FTC Fines
Twitter $150M for Using 2FA Info for Targeted Advertising
(20220527)
Twitter
Faces FTC Probe, Likely Fine Over Use of Phone Numbers for Ads
(20200804)
Read more of this story at SoylentNews.
01:57
Learn From the Best Minds in Commercial Robotics Development IEEE Spectrum

This sponsored article is brought to you by Robotics Summit & Expo.
The Robotics Summit & Expo, taking place May 10-11 at the Boston Convention Center, will bring together the brightest minds in robotics to share their commercial robotics development experiences.
Learn from industry-leading speakers, build new relationships by networking, see demos from 150+ exhibitors showcasing enabling technologies to help build commercial robots.
 Use code IEEE25 at
checkout to save 25% off your full conference pass!
Use code IEEE25 at
checkout to save 25% off your full conference pass!The conference programming will provide professionals the information they need to successfully develop the next generation of commercial robots. This years program has an exceptional lineup of speakers.
The Robotics Summit keynote speakers include the following:
- Howie Choset, Professor of Robotics, Carnegie Mellon University: Idea to Reality: Commercializing Robotics Technologies
- Laura Major, CTO, Motional: Scalable AI Solutions for Driverless Vehicles
- Marc Raibert, Executive Director, AI Institute: The Next Decade in Robotics
- Martin Buehler, Global Head of Robotics R&D, Johnson & Johnson MedTech: The Future of Surgical Robotics
- Nicolaus Radford, CEO, Nauticus Robotics: Developing Robots for Final Frontiers
The expo hall at the Robotics Summit will have more than 150 exhibitors showcasing their latest enabling technologies, products and services that can help robotics engineers throughout their development journey.
The Robotics Summit also offers networking opportunities, a Career Fair, a robotics development challenge and much more.
...
01:48
CISA adds Zimbra bug exploited in attacks against NATO countries to its Known Exploited Vulnerabilities catalog Security Affairs
US CISA has added a Zimbra flaw, which was exploited in attacks targeting NATO countries, to its Known Exploited Vulnerabilities catalog
U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a Zimbra flaw, tracked as CVE-2022-27926, to its Known Exploited Vulnerabilities Catalog.
The CVE-2022-27926 flaw affects Zimbra Collaboration version 9.0.0, which is used to host publicly-facing webmail portals.
Proofpoint researchers recently reported that a Russian hacking group, tracked as Winter Vivern (aka TA473), has been actively exploiting vulnerabilities (CVE-2022-27926) in unpatched Zimbra instances to gain access to the emails of NATO officials, governments, military personnel, and diplomats.
The attacker can also use the compromised accounts to carry out lateral phishing attacks and further infiltrate the target organizations
TA473 targeted US elected officials and staffers since at least February 2023. The threat actors created bespoke JavaScript payloads designed for each government targets webmail portal.
TA473s cyber operations align with the support of Russian and/or Belarussian geopolitical goals.
Researchers have observed TA473, a newly minted advanced persistent threat (APT) actor tracked by Proofpoint, exploiting Zimbra vulnerability CVE-2022-27926 to abuse publicly facing Zimbra hosted webmail portals. The goal of this activity is assessed to be gaining access to the emails of military, government, and diplomatic organizations across Europe involved in the Russia Ukrainian War. reads the post published by Proofpoint.
The JavaScript payloads were designed to conduct Cross Site Request Forgery attacks and steal usernames, passwords, and store active session and CSRF tokens from cookies facilitating the login to publicly facing target webmail portals.
These payloads allow actors to steal usernames, passwords, and store active session and CSRF tokens from cookies allowing the login to publicly facing vulnerable webmail portals belonging to target organizations.
The APT group uses scanning tools like Acunetix to identify unpatched webmail platforms used by target organizations.
The threat actors send phishing email from a compromised address, which is spoofed to appear as someone r...
01:35
System76 Teases Their "Virgo" In-House Manufactured Laptop Phoronix
While for a number of years now System76 has manufactured their own Thelio desktop line of Linux PCs from their facility in Denver, Colorado (and their Launch Keyboard), they have long talked up ambitions for eventually manufacturing their own Linux laptops rather relying on other white-label manufacturers as they currently do. Today a first glimpse of their in-house laptop prototyping was shared,..
01:30
New Expansion Module Brings Standard Slots to Ancient Laptop Hackaday

Upgrading and repairing vintage laptops is often a challenge even if their basic hardware is compatible with ordinary PCs, they often use nonstandard components and connectors due to space constraints. The Sharp PC-4600 series from the late 1980s is a case in point: although it comes with standard serial and parallel ports, the only other external interface is a mysterious connector labelled EXPBUS on the back of the case. [Steven George] has been diving into the details of this port and managed to design a module to turn it into a pair of standard ISA ports.
Apparently, no peripherals were ever released for the EXPBUS port, so reverse-engineering an existing module was out of the question. [Steven] did stumble upon a service manual for the PC-4600 however, and as it turned out, the connector carried all the signals present in an 8-bit ISA bus. Turning it into something useful was simply a matter of designing an adapter board with the EXPBUS connector on one side and regular ISA slots on the other.
...
01:24
Crystal impervious to radiation could be used in spaceship computers Lifeboat News: The Blog
Putting two forms of semiconductor material called gallium oxide together seems to make it completely resistant to radiation.
By Alex Wilkins
01:24
Plastic transistor amplifies biochemical sensing signal Lifeboat News: The Blog
The molecules in our bodies are in constant communication. Some of these molecules provide a biochemical fingerprint that could indicate how a wound is healing, whether or not a cancer treatment is working or that a virus has invaded the body. If we could sense these signals in real time with high sensitivity, then we might be able to recognize health problems faster and even monitor disease as it progresses.
Now Northwestern University researchers have developed a new technology that makes it easier to eavesdrop on our bodys inner conversations.
While the bodys chemical signals are incredibly faintmaking them difficult to detect and analyzethe researchers have developed a new method that boosts signals by more than 1,000 times. Transistors, the building block of electronics, can boost weak signals to provide an amplified output. The new approach makes signals easier to detect without complex and bulky electronics.
01:24
The quantum revolution: Brain waves Lifeboat News: The Blog
Presented by Madhumita Murgia and John Thornhill, produced by Josh Gabert-Doyon and Edwin Lane. Executive producer is Manuela Saragosa. Sound design by Breen Turner and Samantha Giovinco. Original music by Metaphor Music. The FTs head of audio is Cheryl Brumley. Special thanks to The Hospital for Sick Children.
Were keen to hear more from our listeners about this show and want to know what youd like to hear more of, so were running a survey which you can find at ft.com/techtonicsurvey. It takes about 10 minutes to complete and you will be in with a chance to win a pair of Bose QuietComfort earbuds.
01:20
The 2023 Debian Project Leader election LWN.net
The first call for votes for the 2023 Debian Project Leader election has gone out. The campaigning was easy to miss this year, for one simple reason: the current incumbent, Jonathan Carter, is running unopposed for another term. That suggests that turnout will be low this time but, as several developers have pointed out, there is still value in voting; it clarifies whether Carter still has the support of the project.
01:00
Ending an Ugly Chapter in Chip Design IEEE Spectrum

Discussions at chip design conferences rarely get heated. But a
year ago at the International Symposium on Physical Design
(ISPD), things got out of hand. It was described by observers as a
trainwreck and an ambush. The crux of the clash was whether Googles
AI solution to one of chip designs thornier problems was really
better than those of humans or state-of-the-art algorithms. It
pitted established male electronic design automation (EDA) experts
against two young female Google computer scientists, and the
underlying argument had already led to the firing of one Google
researcher.
This year at that same conference, a leader in the field, IEEE Fellow Andrew Kahng, hoped to put an end to the acrimony once and for all. He and colleagues at the University of California, San Diego, delivered what he called an open and transparent assessment of Googles reinforcement its process, called Circuit Training, and reverse-engineering some parts that were not clear enough for Kahngs team, they set reinforcement learning against a human designer, commercial software, and state-of-the-art academic algorithms. Kahng declined to speak with IEEE Spectrum for this article, but he spoke to engineers last week at ISPD, which was held virtually.
The Hows and the Whens
00:58
Music Labels Win Legal Battle Against Youtube-dls Hosting Provider TorrentFreak
 The major record labels dont want the public to download
music from YouTube, which is common practice for millions of
people.
The major record labels dont want the public to download
music from YouTube, which is common practice for millions of
people.
To stop this, the music industry titans deployed a variety of legal tactics around the world. They obtained site-blocking orders, for example, and have taken on stream-ripping sites such as 2Conv and Yout.com directly in court.
Youtube-dl Takedown Battle
In late 2020, the open-source software youtube-dl was added to the list of targets. The tool is used by many stream-ripping sites and was freely available on GitHub. The RIAA asked the developer platform to take youtube-dl offline, arguing that it violates the DMCAs anti-circumvention provision.
GitHub initially complied with the takedown request but after public outrage and involvement from digital rights groups including the EFF, the decision was eventually reversed. GitHub went on to put $1 million into a takedown defense fund.
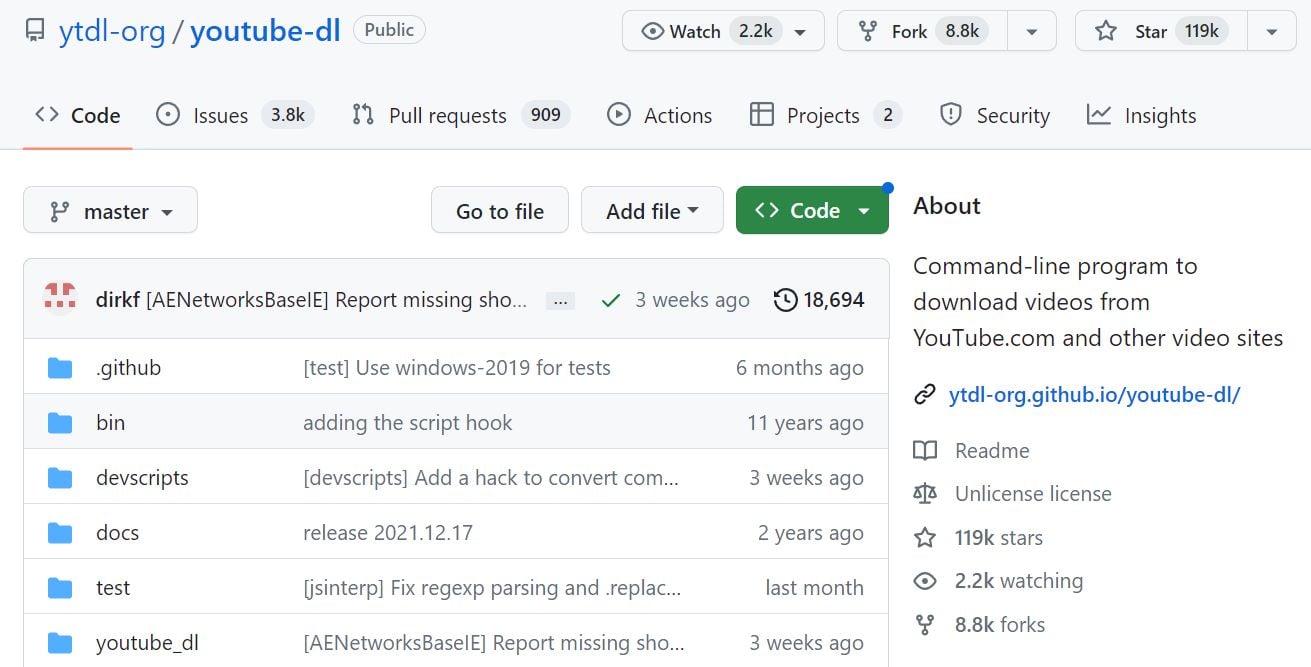
While this series of events represented a setback, the record labels didnt back off. Instead, they set their sights on youtube-dls website hosting provider Uberspace.
The RIAA had already sent cease-and-desist orders to the hosting company in 2020, before it approached GitHub. Uberspace didnt take any action at the time; the youtube-dl website it hosted was not the host of the youtube-dl software. The website carried links to the software and that was hosted elsewhere.
Labels Sue Uberspace in Germany
Last year, Sony Entertainment, Warner Music Group and Universal Music...
00:23
3CX Supply chain attack allowed targeting cryptocurrency companies Security Affairs
Threat actors behind the 3CX supply chain attack have targeted a limited number of cryptocurrency companies with a second-state implant.
As of Mar 22, 2023, SentinelOne observed a spike in behavioral detections of the 3CXDesktopApp, which is a popular voice and video conferencing software product.
The products from multiple cybersecurity vendors started detecting the popular software as malware suggesting that the company has suffered a supply chain attack.
SentinelOne is tracking the malicious activity as SmoothOperator, the company speculates that the threat actor behind the attack has set up its infrastructure starting as early as February 2022.
The company started distributing digitally signed Trojanized installers to its customers.
The impact of the attack could be devastating because the company claims that 3CX has 600,000 customer companies with 12 million daily users. The software is used by organizations in almost every industry, including automotive, food & beverage, hospitality, Managed Information Technology Service Provider (MSP), and manufacturing.
Researchers from Kaspersky discovered that the supply chain attack was used to deliver a backdoor tracked by the Russian firm as Gopuram. The Gopuram backdoor was first discovered by Kaspersky in 2020, but the researchers observed a surge in the number of infections in March 2023, likely coinciding with the attack on 3CX.
While investigating an attack on a Southeast Asian cryptocurrency company in 2020, the researchers noticed the presence of the AppleJeus backdoor on systems infected with Gopuram backdoor. AppleJeus is known to be a backdoor used by North Korea-linked Lazarus APT Group.
The Gopuram backdoor was employed in other attacks on organizations in the cryptocurrency industry, which is aligned with the interests of the Lazarus threat actor.
Upon executing the Gopuram backdoor, the malware connects to a C2 server and await further commands. The backdoor is able to launch at least eight in-memory modules.
The backdoor implements commands that allow the attackers to interact with the victims file system and create processes on the infected machine. Gopuram was additionally observed to launch in-memory modules. reads the analysis published by Kaspersky. Just like the implants used in the 3CX campaign, Gopurams modules are DLL files th...
00:13
New Chipset Could Finally Make It Easier to Build Budget Ryzen 7000 PCs SoylentNews
A620 chipset is missing features, but (mostly) not the important ones:
If you're trying to build a low-end to midrange gaming PC or workstation with inexpensive but modern parts, it has been hard to recommend AMD's Ryzen 7000-series processors. That's partly because Intel's CPUs have offered more cores for similar money, but motherboards with AMD's socket AM5 have remained stubbornly expensive, and their lack of support for DDR4 memory means you'll pay more to get DDR5 RAM.
That may change somewhat thanks to the new entry-level AMD A620 chipset, which the company quietly announced last week. AMD says it should bring the prices of AM5-based motherboards down to around $85, not far north of what low-end Intel-based H610 and B660 motherboards cost, though they'll still require DDR5 (for the DDR5-6000 that AMD recommends for optimal Ryzen performance, the price premium is still not quite double what you'll pay for the same amount of DDR4-3200).
Compared to X670 and B650-based motherboards, A620 chipsets will have more limited connectivity. There's no PCI Express 5.0 support at all for either graphics cards or SSDsnot a huge blow since no GPUs and few SSDs support PCIe 5.0 at this point anyway, but a step back for future-proofing. The processor will still provide enough PCIe 4.0 lanes for a GPU and a single SSD, but the chipset only supports PCIe 3.0 speeds for additional SSDs. The chipset also supports fewer USB ports overall and no 20Gbps USB ports.
Perhaps more significantly, A620 chipsets don't support any kind of processor overclocking, nor do they support the Precision Boost Overdrive (PBO) or Curve Optimizer features for automated overclocking or undervolting. This is consistent with past AMD A-series chipsets and non-Z-series Intel chipsets, which have also limited their support for overclocking features. AMD says that memory overclocking will still be supported by "most [motherboard] models."
[...] AMD says that more A620-based boards are coming from the usual suspectsASRock, Asus, Gigabyte, MSI, and Biostar are all planning to release a range of A620 motherboard options.
Read more of this story at SoylentNews.
00:00
The Liquid Trees of Belgrade: The Facts Behind The Furore Hackaday

Historically, nature has used trees to turn carbon dioxide back into oxygen for use by living creatures. The trees play a vital role in the carbon cycle, and have done so for millennia. Recently, humans have thrown things off a bit by getting rid of lots of trees and digging up a lot more carbon.
While great efforts are underway to replenish the worlds tree stocks, Belgrade has gone in a different direction, creating artificial liquid trees to capture carbon dioxide instead. This has spawned wild cries of dystopia and that the devices are an affront to nature. Lets sidestep the hyster...
Tuesday, 04 April
23:51
Sorting Through Haystacks to Find CTI Needles The Hacker News
Clouded vision CTI systems are confronted with some major issues ranging from the size of the collection networks to their diversity, which ultimately influence the degree of confidence they can put on their signals. Are they fresh enough and sufficiently reliable to avoid any false positives or any poisoning? Do I risk acting on outdated data? This difference is major since a piece of
23:44
Security updates for Tuesday LWN.net
Security updates have been issued by Fedora (openbgpd and seamonkey), Red Hat (httpd:2.4, kernel, kernel-rt, and pesign), SUSE (compat-openssl098, dpdk, drbd, ImageMagick, nextcloud, openssl, openssl-1_1, openssl-3, openssl1, oracleasm, pgadmin4, terraform-provider-helm, and yaml-cpp), and Ubuntu (haproxy, ldb, samba, and vim).
23:30
Intel Posts Xe DRM Scheduler Patches For Review Phoronix
As part of the process for getting Intel's new Xe DRM kernel driver upstreamed as the eventual replacement to the existing i915 driver for Gen12 graphics hardware and newer, Intel engineers on Monday posted the initial Xe DRM scheduler patches that have been separated out to get review on them, figure out what can be common/shared among drivers, and get those bits upstreamed...
23:16
Rorschach Ransomware Emerges: Experts Warn of Advanced Evasion Strategies The Hacker News
Cybersecurity researchers have taken the wraps off a previously undocumented ransomware strain called Rorschach that's both sophisticated and fast. "What makes Rorschach stand out from other ransomware strains is its high level of customization and its technically unique features that have not been seen before in ransomware," Check Point Research said in a new report. "In fact, Rorschach is one
23:07
New Rilide Malware Targeting Chromium-Based Browsers to Steal Cryptocurrency The Hacker News
Chromium-based web browsers are the target of a new malware called Rilide that masquerades itself as a seemingly legitimate extension to harvest sensitive data and siphon cryptocurrency. "Rilide malware is disguised as a legitimate Google Drive extension and enables threat actors to carry out a broad spectrum of malicious activities, including monitoring browsing history, taking screenshots, and
23:06
Links 04/04/2023: KDE Plasma 5.27.4 and Arti 1.1.3 Techrights
![]()
Contents
- GNU/Linux
- Distributions and Operating Systems
- Free, Libre, and Open Source Software
- Licensing / Legal
- Programming/Development
- Standards/Consortia
- Leftovers
- Gemini* and Gopher
-
GNU/Linux
-
Desktop/Laptop
-
9to5Linux TUXEDO Stellaris 16 Linux Gamin...
-
-
23:01
Automate PostgreSQL database deployment using RHEL System Roles Linux.com
The new PostgreSQL System Role helps speed and simplify deployment and management of PostgreSQL servers in Red Hat Enterprise Linux (RHEL).
Read More at Enable Sysadmin
The post Automate PostgreSQL database deployment using RHEL System Roles appeared first on Linux.com.
22:33
Updated NVIDIA Turing Firmware Published For Open-Source Nouveau Driver Phoronix
NVIDIA has published updated NVIDIA TU10x /TU11x "Turing" GPU firmware to support newer RTX 20 hardware revisions and fix outstanding issues affecting the open-source Nouveau driver...
22:23
Prevent and detect Adobe ColdFusion exploitation (CVE-2023-26360, CVE-2023-26359) Help Net Security
When Adobe released security updates for its ColdFusion application development platform last month, it noted that one of the vulnerabilities (CVE-2023-26360) had been exploited in the wild in very limited attacks. Were your servers among those hit? And what should you do if they were? About CVE-2023-26360 (and CVE-2023-26359) CVE-2023-26360 is an improper access control vulnerability that could result in arbitrary code execution in the context of the current user, and was reported to Adobe More
The post Prevent and detect Adobe ColdFusion exploitation (CVE-2023-26360, CVE-2023-26359) appeared first on Help Net Security.
22:20
WiFi Flaws Allow Network Traffic Interception on Linux, iOS, and Android HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
The findings are to be presented at the Usenix Security Symposium.
This is a post from HackRead.com Read the original post: WiFi Flaws Allow Network Traffic Interception on Linux, iOS, and Android
22:17
GPT: Where are we in the food chain? the loose wire blog
On November 29 2022 I implored the tech world to bring on winter: Were out of good ideas. I should have kept my mouth shut: The next day ChatGPT was unleashed on the public, and we havent paused for breath since. I believe we users need to contribute more to the debate and figure out where we stand, and what we stand for.
The mad rush to compete in this space means the big players are rolling their AIs out not only before theyre ready, but silly money is being thrown at startups promising exploitation of these tools. A massive land-grab is taking place, with little idea of the consequences and with the ink of some 155,000 tech layoff slips barely dry.
I wish I could be more sanguine. Ive always loved technology, and I am absolutely bowled over by the latest iteration of ChatGPT, GPT-4. Everyone else has been writing about their experiences with it, so I wont bore you with mine, but theres no question were in Kansas anymore. This technology will change a lot. A LOT.
But we need to keep our eye on the ball. Some have called for a moratorium, which is at best naive and at worst giving the industry too much credit for a sense of responsibility. Thats not what is going on here. Its money.

The ball we need to keep an eye on is market (and political, but well leave for later) power, and we should be watching it carefully as it shifts. It doesnt shift far, but it is shifting. We are not witnessing disruption in the sense that Clayton Christensen defined it, were...
21:53
PowerDNS Security Advisory 2023-02: Deterred spoofing attempts can lead to authoritative servers being marked unavailable Open Source Security
Posted by Otto Moerbeek on Apr 04
Hello,We have released PowerDNS Recursor 4.6.6, 4.7.5 and 4.8.4 due to
a low severity security issue found.
Please find the full text of the advisory below.
The [1]4.6, [2]4.7 and [3]4.8 changelogs are available.
The [4]4.6.6 ([5]signature), [6]4.7.5 ([7]signature) and
[8]4.8.4 ([9]signature) tarballs are available from our download
[10]server. Patches are available at [11]patches. Packages for various
distributions...
21:33
IRC Proceedings: Monday, April 03, 2023 Techrights
Also available via the Gemini protocol at:
- gemini://gemini.techrights.org/irc-gmi/irc-log-techrights-030423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-030423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-social-030423.gmi
- gemini://gemini.techrights.org/irc-gmi/irc-log-techbytes-030423.gmi
Over HTTP:
|
... |
21:28
Are Your Strawberries Bland? Pesticides Could be to Blame SoylentNews
Strawberries tend to be blander and less nutritious when treated with particular pesticides:
Have you ever bitten into a plump, red strawberry, only to find it bland and watery? Certain pesticides might be responsible. A team reporting in ACS' Journal of Agricultural and Food Chemistry has found that two common strawberry fungicides can impact cellular mechanisms, creating berries with subdued flavor and sweetness, as well as a lower nutritional value.
The flavor profile of any produce, including berries, is a result of its taste and smell sweetness often arises from the amount of dissolved glucose or fructose, and a unique aroma comes from volatile compounds, such as esters and terpenes. In addition, many fruits are also full of nutrients, including vitamin C, folic acid and antioxidants. But because fungicides are designed to disrupt the cellular processes of detrimental fungi, they could accidentally interfere with these processes in crops, inhibiting production of these important flavor and nutritional compounds. So, Jinling Diao and colleagues wanted to investigate how two common pesticides used on strawberries boscalid (BOS) and difenoconazole (DIF) affect specific molecular pathways in berries.
[...] Looking more closely, the team found that BOS had a direct effect on the regulation of genes involved in cellular pathways related to producing sugars, volatile compounds, nutrients and amino acids. Finally, in a blind taste test, people consistently preferred the untreated strawberries. The researchers say that this work could provide guidance to farmers about the use of pesticides.
The researchers found that, despite having the same size and color of untreated strawberries, the ones treated with the pesticides had lower levels of soluble sugar and nutrients, the sugars were converted into acids, and the amounts of volatile compounds changed, which subdued the taste and aroma.
Journal Reference:
Yuping Liu, Rui Liu, Yue Deng, et al., Insights into
the Mechanism of Flavor Loss in Strawberries Induced by Two
Fungicides Integrating Transcriptome and Metabolome Analysis,
J. Agric. Food Chem. 2023, 71, 8, 39063919, 2023
https://doi.org/10.1021/acs.jafc.2c08157
Read more of this story at SoylentNews.
21:24
On-line Casino Money Back From Online Gambling h+ Media
On-line Casino Money Back From Online Gambling
The max bonus amount for the 1st deposit is $100, for the 2nd deposit $100 and for the 3rd deposit $100. The minimum deposit thats eligible for the bingo bonus is $25. The casino partners with a number of E-Wallet firms that may permit you to switch the amount you want into your casino account. Transfers from E-Wallet to the casino account take a short amount of time to complete. In the unlikely event that you run into an issue while at the Mr Green Sports site, the client care staff is available 24/7 and available via reside chat, e mail, and get 1xbet bonus code 131% for new customers phone. You can also send them a message by way of a textual content box within the Help section of the site, together with your consumer ID automatically connected.
You can be reach them by e-mail as nicely as being called via local telephone numbers. Mr Greens Live Casino will get a player up close to the action with the assistance of the HD quality and numerous camera angles in addition to offering a slow-motion replay if needed. There is also an assorted vary of betting limits provided across all tables, with low stakes options and high limits alongside. There can also be a Gold Card Bonus where youll find a way to play the exclusive live blackjack desk during the weekend.
The account verification is a standard process of each on line casino these days and they deal with players privacy with the utmost confidentiality. The addContent of documents is safe and their use is restricted solely to a handful of people in management of carrying out the verifications. Once the request has been made the on line casino needs to course of and approve your request. According to the on line casino, it could occur in a few seconds, however the timeframe is highly dependent on your account verification standing, the quantity requested, and the payment method.
Then here you will find all the information about the best Pay n Play on line casino obtainable in New Zealand. We can safely conclude that they managed to attempt this and the website is highly safe for anyone enjoying there. The operator made certain to acquire the license of the Malta Gaming Authority, which is the playing commission that issued licenses for so much of reputable platforms on the market. A reputable on-line playing operator needs to be on the players disposal at any given second. You can not predict when you ought to have a problem with how the platform works, or a query to ask in regards to the website.
- There are additionally many purposes that make life easier for us every day like Mr Green App that may be downloaded.
- All on-line UK Casino should abide by the Data Protection Act, which is significant as youll be asked to share your personal and banking particulars.
- This gamesite also...
21:22
Mr Green Why You Should Choose This Casino h+ Media
Mr Green Why You Should Choose This Casino
Many players are huge followers of the pokies video games that are primarily based on the popular Marvel comedian collection. TheMr Green Live Casinooffers an in depth range of games all streamed stay from a purpose-built studio and dealt by professional sellers. The games on provide embody numerous totally different blackjack and roulette video games, baccarat, Caribbean stud poker, casino holdem, Texas Holdem and 3-card poker. In the menu on the primary web page, a participant can simply find a part with sports activities betting, where there might be an option of having a bet without having to create a second account.
It can detect when a participant is falling into a threat zone and help them change for the better. Responsible betting is all about being in charge of how a lot, when, and tips on how to wager. An accountable gambler begins by identifying the proper bets and sticks to their budget via proper bankroll administration. They are additionally aware of the wagering situations to allow them to implement strategies with out involving their emotions. Because eSports is a fancy subject, Mr Green lays out betting ideas to help new players sharpen their abilities.
The on-line on line casino and its producers Kambi Gaming knew it very well have offered Mr Green cell on line casino for the shoppers which may be downloaded free of charge from Play Store or App Store. Ultimately, the bonus provides, incredible games choice, and high quality list of buyer assist and fee options make the positioning a valuable find. Some of the primary choices include sports activities betting, stay casino, and on line casino games, and the bonus can be utilized by your preference.
It provides free, unbiased and private help on all elements of problems with gambling on their website. Banking options are covered extensively on Mr Greens help centre, everything from withdrawals, deposits and proof of identification. Also, it allows e-banking like credit card or eWallet transactions. It has become the accepted standard for casinos to have 24/7 reside chatrooms out there for his or her players. Mr Green Casino does not have a live chat room theyre out there a assist centre team to obtain and reply any questions 24/7.
Although its barely different to the desktop page, the cellular web site is still easy to navigate. If you take pleasure in enjoying at on-line casinos on your smartphone or tablet, the Mr Green Casino website for cell browsers is amongst the very best around. Mr Green not just provides a welcome bonus however has many ongoing promotional presents for its gamers. Each time you log into your account and play, you will earn entries in weekly drawings in your free casino credit. Mr Green has a loyalty reward program on a person foundation based mostly on the way you play.
Sensitive info that has to do along with your banks is the primary target of cybe...
21:21
Mr Green Review 2022 Nz$100 Bonus + 200 Free Spins! Read More! h+ Media
Mr Green Review 2022 Nz$100 Bonus + 200 Free Spins! Read More!
We are all the time on the lookout for ways to provide a 5-star service and expertise if you have particular feedback for us then wed be grateful if you could get in touch with us to tell us. They have one of many absolut worst customor service ive ever seen in an organization, not simply betting company however firm in genneral. Thank you Marc for taking the time to provide us with such an quantity of detailed feedback. If its, its insulting to experienced prospects and it is deception to the newbies. Adopt responsible gambling habits and search help immediately should you develop problems.
For instance, you could come across a very beneficiant welcome bonus, only for it to transpire later that the wagering requirement was 65x. This means you would wish to play the bonus value sixty five times earlier than you would really get to it. Remember that theres no obligation to accept any bonus whenever you join an online on line casino. Its at all times price looking at the reside supplier game choice.
When it is time to confirm your account, the casino will send you an e-mail to your personal e mail handle, so make sure to examine your inbox frequently. As standard process, the casino would need identification documentation, proof of residential address and generally even proof of fee technique, however this will likely vary from customer to customer. While the Mr. Green website interface could do with some work, the casino section is brimming with quality slots and desk games. Furthermore, the awards the operator has gained contributes to the notion that they are the place theyre in the gambling business for a cause. Mr. Greens casino is totally a safe on-line gambling route for punters to pursue. By downloading this app, youll enjoy a particular cell foyer thats designed to provide the best performance in your gaming.
This is because theyre little used in comparability with iOS and Android. Even so, there are web sites that can be accessed out of your Windows telephone as well. Nowadays you presumably can deposit, increase or cut back the bets, choose the paylines and wager easily from your mobile, with none downside. The second possibility is to use the demo or practice mode on the casino sites or of their purposes. When you are ready to move on to the real sport , you are in a place to do it with a easy click on of a button.
That means that you can relax and enjoy the protected, authentic atmosphere of the elegant European online casino. You can make the most of the stay chat, work together with sellers in table games, e-mail them or contact them by cellphone between 6 am and Midnight. MrGreen.com has an excellent popularity for delivering quick and efficient customer support that goes above and beyond for his or her gamers. Of course, theres that enjoyable part were all hoping for, withdrawal of...
21:19
Mr Green On Line Casino Evaluate & Score Is Mr Geen Protected & Fair? h+ Media
Mr Green On Line Casino Evaluate & Score Is Mr Geen Protected & Fair?
The max bonus amount for the first deposit is $100, for the 2nd deposit $100 and for the 3rd deposit $100. The minimum deposit thats eligible for the bingo bonus is $25. The on line casino companions with several E-Wallet companies that will allow you to switch the amount you need into your casino account. Transfers from E-Wallet to the on line casino account take a short period of time to finish. In the unlikely occasion that you just run into a problem whereas on the Mr Green Sports web site, the shopper care staff is readily available 24/7 and obtainable via live chat, email, and telephone. You also can send them a message through a textual content field within the Help part of the positioning, with your consumer ID routinely attached.
- Their web sites are absolutely optimized for mobile gaming, but solely permit direct entry by way of the browser.
- Which means having a comprehensivelive casinoplatform for their players enjoyment.
- We have accomplished thorough research on all operators we recommend to guarantee that the information conveyed to you is related, and for the purposes of wagering for entertainment needs.
- Alternatively, you probably can playweb-based versions of all Mr Green mobile slotsdirectly in the browser of any smartphone or pill, by going to on line casino.mrgreen.com.
When youre on the app, youll discover the latest promotions, essentially the most famend games, and the chance to search for your favorite on line casino game at the high of the web page. Gambling is genuinely online when youll have the ability to totally rely on iPhone Casinos with out bothering about downloads or in-phone storage. Before getting into your data into a web-based betting web sites database, double-check the manner of operation. Any restriction on the variety of games you could play in your ultra-smooth smartphone is certain to be a bummer. You dont desire the identical situations in terms of iPhone casinos.
Video Games Available Right Here
My ac is verified and if I request withdrawal at 9pm its often in my account by 4pm the next day. Ive had a couple of concern re deposit restrict not refreshing however nothing main. Service-wise, the members have a incredible array of promotions and great customer assist. Even though the banking choices are minimal, they are a minimal of the more common cost companies that get used on-line. Their accountable gaming feature permits gamers to set limits on what is banked as deposits and what time they can be spent when playing on the positioning. The wagering requirement we mentioned works in conjunction with your capacity to withdraw any winnings made with the bonus money.
The registration, deposit and the primary few rounds with slot machines and reside on line casino went well as expected. The o...
21:00
Open-Source FaceID With RealSense Hackaday

RealSense cameras have been a fascinating piece of tech from Intel weve seen a number of cool applications in the hacker world, from robots to smart appliances. Unfortunately Intel did discontinue parts of the RealSense lineup at one point, specifically the LiDAR and face tracking-tailored models. Apparently, these havent been popular, and we havent seen these in hacks either. Until now, that is. [Lina] brings us a real-world application for the RealSense face tracking cameras, a FaceID application for Linux.
The project is as simple as it sounds: if the cameras built-in
face recognition module recognizes you, your lockscreen is
unlocked. With the target being Linux, it has to tie into the
Pluggable Authentication Modules (PAM) subsystem for
authentication, and of course, theres a PAM module for RealSense to
go with it, aptly named pam_sauron. This module is
written in Zig, a modern C-like language, so its both a good
example of how to create your own PAM in...
21:00
Initial Support For AMD's Next-Gen, Multi-XCC CDNA Accelerator Starting With Linux 6.4 Phoronix
As I pointed out at the end of March, AMD has begun bringing up a new CDNA GPU in their Linux kernel driver code, past the currently known Instinct MI300 "GFX940" series. This "GFX943" part is some new CDNA multi-XCC accelerator and the open-source AMD engineers have begun posting many patches for this new GPU target. The initial bits of that support will appear in the upcoming Linux 6.4 cycle...
20:42
RADV Sees Experimental Fragment Shader Interlock - Important For Emulators, D3D12 Phoronix
A currently-testing implementation of VK_EXT_fragment_shader_interlock has been published for Mesa's Radeon Vulkan "RADV" driver. This Vulkan fragment shader interlock support is used by some game emulators as well as being useful in running Direct3D 12 atop Vulkan and similar purposes...
20:22
xf86-input-libinput 1.3 Brings Custom Pointer Acceleration Profile Support Phoronix
Peter Hutterer, Red Hat's leading Linux input expert, today X.Org Server driver for making use of libinput in an X.Org Server world...
20:08
Arid Viper Hacking Group Using Upgraded Malware in Middle East Cyber Attacks The Hacker News
The threat actor known as Arid Viper has been observed using refreshed variants of its malware toolkit in its attacks targeting Palestinian entities since September 2022. Symantec, which is tracking the group under its insect-themed moniker Mantis, said the adversary is "going to great lengths to maintain a persistent presence on targeted networks." Also known by the names APT-C-23 and Desert
19:54
Think Before You Share the Link: SaaS in the Real World The Hacker News
Collaboration sits at the essence of SaaS applications. The word, or some form of it, appears in the top two headlines on Google Workspaces homepage. It can be found six times on Microsoft 365s homepage, three times on Box, and once on Workday. Visit nearly any SaaS site, and odds are collaboration will appear as part of the apps key selling point. By sitting on the cloud, content within
19:47
Wayland 1.22 Released With New Preferred Buffer Scale & Transform Protocol Phoronix
Wayland 1.22 is now available as the newest feature update to this core set of Wayland protocol and helper code...
19:12
1500+ Increase in Weekly Deaths (England and Wales) is Not Back to Normal schestowitz.com
 ve
just checked ONS. Its site was updated faster than usual, as early
as 9:30AM this morning, at least for this dataset.
ve
just checked ONS. Its site was updated faster than usual, as early
as 9:30AM this morning, at least for this dataset.
The site updated at ONS:
Number of deaths for week 11:
Notice how much that grew between 2022 and 2023.
2019 was a lot better too. 2019 data for March/April:
So to summarise
2019: 10,567 deaths
2022: 10,928 deaths
2023: 12,133 deaths
They tell us the pandemic is a thing of the past. The data does not support this assertion.
18:45
Stable Diffusion Copyright Lawsuits Could be a Legal Earthquake for AI SoylentNews
The AI software Stable Diffusion has a remarkable ability to turn text into images. When I asked the software to draw "Mickey Mouse in front of a McDonald's sign," for example, it generated the picture you see above.
Stable Diffusion can do this because it was trained on hundreds of millions of example images harvested from across the web. Some of these images were in the public domain or had been published under permissive licenses such as Creative Commons. Many others were notand the world's artists and photographers aren't happy about it.
In January, three visual artists filed a class-action copyright lawsuit against Stability AI, the startup that created Stable Diffusion. In February, the image-licensing giant Getty filed a lawsuit of its own.
[...]
The plaintiffs in the class-action lawsuit describe Stable Diffusion as a "complex collage tool" that contains "compressed copies" of its training images. If this were true, the case would be a slam dunk for the plaintiffs.But experts say it's not true. Erik Wallace, a computer scientist at the University of California, Berkeley, told me in a phone interview that the lawsuit had "technical inaccuracies" and was "stretching the truth a lot." Wallace pointed out that Stable Diffusion is only a few gigabytes in sizefar too small to contain compressed copies of all or even very many of its training images.
Related:
Ethical
AI art generation? Adobe Firefly may be the answer.
(20230324)
Paper:
Stable Diffusion "Memorizes" Some Images, Sparking Privacy
Concerns (20230206)
Getty
Images Targets AI Firm For 'Copying' Photos (20230117)
Pixel Art
Comes to Life: Fan Upgrades Classic MS-DOS Games With AI
(20220904)
A
Startup Wants to Democratize the Tech Behind DALL-E 2, Consequences
be Damned (20220817)
...
18:43
How to install PHP 8.2 with Apache on Debian 11 Linux nixCraft
Debian 11 is an excellent server OS to run the LAMP stack. PHP (Hypertext Preprocessor) is a widely-used open source general-purpose scripting language especially suited for web development. However, Debian 11 comes with
Love this? sudo share_on: Twitter - Facebook - LinkedIn - Whatsapp - Reddit
The post How to install PHP 8.2 with Apache on Debian 11 Linux appeared first on nixCraft.
18:41
DoJ cracks down on cryptocurrency fraud, seizes $112 million in linked funds Help Net Security
The Department of Justice (DoJ) declared the confiscation of digital currency valued at approximately $112 million connected to fraudulent cryptocurrency investments. Laundering money from cryptocurrency confidence scams According to court documents, the virtual currency accounts were allegedly used to launder proceeds of various cryptocurrency confidence scams. In these schemes, fraudsters cultivate long-term relationships with victims met online, eventually enticing them to make investments in fraudulent cryptocurrency trading platforms. In reality, however, the funds sent by More
The post DoJ cracks down on cryptocurrency fraud, seizes $112 million in linked funds appeared first on Help Net Security.
18:40
Links 04/04/2023: Debian Installer Bookworm RC 1 and Qt 6.5 Techrights
![]()
Contents
-
GNU/Linux
-
Audiocasts/Shows
-
Tux Digital Destination Linux 318: Cloud Repatriation & Framework Laptops Go Next Level!
This weeks episode of Destination Linux, we will be discussing cloud and server repatriation. Then were going to show you why the Framework laptop is going to be your next laptop. Plus, we have our tips/tricks and software picks. All this and more coming up right now on Destination Linux to keep those penguins...
-
-
18:32
Pirate Site Admins Arrested in 2015, Now Acquitted For a Second Time TorrentFreak
 In 2014, David Tard, Andreu Caritg, and Oriol Sol were
hard at work in Spain developing Tviso, a service with a goal to
unify legal streaming services into a centrally-accessed discovery
hub.
In 2014, David Tard, Andreu Caritg, and Oriol Sol were
hard at work in Spain developing Tviso, a service with a goal to
unify legal streaming services into a centrally-accessed discovery
hub.
Tviso was a new venture for the Spaniards, although not an entirely unfamiliar one. At the same time, the men were also the operators of Series.ly, a then-four-year-old social television download site that aimed to blend the benefits of free access to premium TV series and movies with a walled-garden social network of entertainment media fans.
With a reported four million users, Series.ly was a success. It reportedly generated over 638,000 euros in the three years leading up to 2015, after which new legislation in Spain would render its activities illegal.
Police Raid Operators of Series.ly
Following a complaint from a local trade industry group representing U.S. rightsholders, and six months after the introduction of reformed intellectual property law in Spain, local authorities were ready to take action.
An investigation carried out by the Anti-Piracy Group of the Central Computer Security Brigade, with assistance from the Provincial Judicial Police Brigade of Barcelona, had linked Series.ly to a company operated by Tard, Caritg, and Sol.
In the summer of 2015, Polica Nacional officers raided the companys offices in search of evidence related to the operation of Series.ly. That included details of revenue generated by advertising and premium account sales to customers all over Europe, Switzerland, United States, Mexico, Chile and beyond.
The three men were arrested and subsequently charged with intellectual property crimes. It would be another seven years before they had their day in court.
Rightsholders Demand Four Years in Prison
Local police labeled Tard, Caritg, and Sol a criminal organization. Rightsholders represented by the Association of National Videographic Distributors and Importers (ADIVAN), described the conduct of Series.lys operators as straigh...
18:00

There are projects you create to share with the world, but there are also those you do just because you want something for yourself. Lucky for us, [Dietrich-L]s 30-year-long project to create CPM-65, a CP/M-like OS for the 6502, has become both.
[Dietrich-L] does admit that the documentation is sparse and for my personal needs. Still, the OS has most of what youd expect and runs well on the target system, a heavily-modified Elektor Junior with 57 kB of RAM. The disk structure is compatible with CP/M, although the Transient Program Area (TPA) apparently starts at $200, which is a bit different from a typical CP/M. Apparently, the system uses some low memory which necessitated the relocation. Just in case you were hoping, CPM-65 doesnt emulate an 8080 system, so you cant run normal CP/M programs. You just get a similar operating environment and tools.
The 31 commands listed include an assembler, BASIC, Forth, an editor, and some disk tools, along with a debugger. Xmodem is available, too. Everything is written in assembly for the CPM-65 assembler, so bootstrapping could be an issue if you need to make any changes.
Speaking of changes, there is some documentation in the docs sub-directory, including the layout of [Dietrich-L]s system, which would be handy if you were trying to run this on your own hardware. Youll also find basic commands for the editor...
17:29
That ticking noise is your end users laptops Graham Cluley
Graham Cluley Security News is sponsored this week by the folks at Kolide. Thanks to the great team there for their support! Heres an uncomfortable fact: at most companies, employees can download sensitive company data onto any device, keep it there forever, and never even know that theyre doing something wrong. Kolides new report, The Continue reading "That ticking noise is your end users laptops"
17:01
Podcast Episode: Losing Until We Win: Realistic Revolution in Science Fiction Deeplinks
When a science-fiction villain is defeated, we often see the heroes take their victory lap and then everyone lives happily ever after. But thats not how real struggles work: In real life, victories are followed by repairs, rebuilding, and reparations, by analysis and introspection, and often, by new battles.

You can also find this episode on the Internet Archive.
Science-fiction author and science journalist Annalee Newitz knows social change is a neverending process, and revolutions are long and sometimes kind of boring. Their novels and nonfiction books, however, are anything but boringthey write dynamically about the future we actually want and can attain, not an idealized and unattainable daydream. Theyre involved in a project called We Will Rise Again, an...
17:00
Obsidians SSPM solution enables organizations to increase their SaaS security Help Net Security
Obsidian Security released its latest suite of SaaS security solutions. This suite of solutions comprising Obsidian Compliance Posture Management, Obsidian Integration Risk Management, and Obsidian Extend will together enable security and GRC teams to increase their SaaS security and compliance posture measurably. For far too long, Security and GRC teams have been working in the dark. We hear from security leaders time and again that they have no control over their ever-expanding mesh of SaaS More
The post Obsidians SSPM solution enables organizations to increase their SaaS security appeared first on Help Net Security.
17:00
On retreat again, October 2022. Antarctica Starts Here.
Time and funds permitting, I try to go on retreat every year or two. I like driving someplace new, someplace I've never been before, and getting off the grid for a couple of days. I find that it makes it much easier to relax, rest, catch up on my reading (or sometimes television), do some writing, tinker with locks a bit, and generally be nonverbal for about a week. It's not easy these days (and won't be for a while, I suspect) but it is something that I at least attempt periodically. The AirBnB I rented had a most unusual design, it was basically a wedge built into a hillside so that the earth that covered the walls and much of the roof formed insulation (something that many houses in this state lack). Because I'm not a total maniac I try to make sure that there is connectivity where I am, and this particular location had both DSL and Starlink service in a shotgun configuration, which worked surprisingly well. I will say, however, that takeout that far in northern California can be a bit dodgy and I found myself getting quite sick just before the end of my trip.
All of that aside I did some hiking and took some photographs of the forest out that way, some things I came across, and the local wildlife that visited me once in a while. I never did see the bear that I was told about but the deer there, while not actually tame did approach more closely than expected.
I know nobody really likes to hear these words, but here are my vacation pictures.
Ukraine - The Road To War Terra Forming Terra
All the other so called analysis has largely been excusing activity used to goad russia into some form of war. What Russia obviously did was secure effective Russian provinces against Ukrainian attacks. The Ukrainian now have to push dug in Russian forces out.
FDA confirms Graphene Oxide is in the mRNA COVID-19 Vaccines Terra Forming Terra

Plasma SPACE. Terra Forming Terra
Plasma SPACE.
I am continuing my reading of the book by Robert Temple on Plasma, but before we go further i do want to suggest something. We know that 98 % of the mass cannot be seen. We Know that this mass is in the observed galaxies. We also know that all particle creation must also be specific to any given galaxy. Way more important and a complete error to ignore is that all such mass is sublight. That means that it is all contained within those galaxys.
Past that it follows that our whole galaxy is a living ocean of our neutral neutron pairs which alone are able to generate enough gravity. It still takes gravitational compression to produce decay events and we have that in spades with every star including our sun. I do think we are watching neutral neutron pairs decaying into hydrogen.
There are other aspects to think about incuding conglomeration into proto elements in particular, but we need to get used to the idea that we are all breathing this and likely even walking through it or even passing through it with no capacity to detect.
The big take home is the lack of measurable drag, Does a fish notice drag?
Understand that the so called ether of a century ago has been measured of late. So yes, something is there and it is not impossibleum.
The point is that we are not able to detect 98% of our surrounding mass. Of course it is spread out like cotton batten as compared to the matrial we can see and touch and it is out there certainly filling our whole solar system and likely our whole galaxy.
What i am trying to do here is to induce a mental flip in your thinking. It was hard for me and cannot be any easier for you.,
Reversing Dementia, Parkinsons, Alzheimers, Autism and other neurological issues. Terra Forming Terra
I had an extended conversation today with my daughter on her ongoing spiritual researchs regarding the above medical problems. Extremely insightful. In fact, the future for all these has just brightened.
Two big take homes is that those diseases driven by physicological changes can be reversed using a deeply researched new supplement product. It takes time but we have complete reversal in one autistic child to share and this is indicated for most of the rest as well.
The key problem to over come are microlesions both on the brain surface and also likely within the brain as well. Simply reversing those micro lesions allows the brain to properly rewire.
This is very good news that can ultimately applied by any practicioner.
The second big take hame has been the complete reversal of dementia in a 93 year old woman.I have never heard of that happening before. The process required extensive spiritual work with a family member that also engaged the rest of the family as well, but culminated with the womans spirit causing it all to happen. At no time was the patient communicated with because that was impossible.
What we learned is that the cognitive mind can block healing or any form of improvement even when the spirit of that person is standing by. engaging that spirit remotely allowed resolution and a restoration of an active cognitive mind. It is quite possible that cognitive minds can shut down almost in pursuit of death.
I now think that all forms of mental illness can be resolved. It is still in most cases a process and we are even taking on chronic family disorders as well successfully. Plenty of overlap obviously. Yet it is early days and we will soon need talented folks to join in with the process. We will need a community of spiritual practicioners.
From the persective of sharing this message, we understand that reversing dementia will provide best traction. Everyone has been touched and millions of caregivers want to see a better outcome. Th...
16:01
Microsoft Close to Settling EC Antitrust Cloud Complaints SoylentNews
Transparency? Redmond's heard of it:
Microsoft is close to resolving antitrust complaints lodged against it with the European Commission by local suppliers OVHcloud, Aruba S.p.A and Danish Cloud Community (DCC) over alleged commercial abuses.
The details of the said settlement remain under wraps and likely won't be published in detail, which is frustrating others' efforts to take the US software and cloud giant to task over alleged controlling market behavior.
OVHcloud, Aruba and DCC fired a joint complaint against Microsoft in May, with OVH itself confirming they were pressing the authorities for a "level playing field among cloud providers," saying Microsoft "undermines fair competition."
The complaint was focused on the higher costs of buying and running Microsoft software in clouds other than Azure, and technical adjustments needed to run some programs on competitors' clouds.
Fast-forward to this week and chatty sources close to the situation indicate Microsoft has agreed to settle the case and will propose binding commitments imminently, according to Bloomberg.
[...] Representing 24 cloud providers, the Cloud Infrastructure Service Providers in Europe (CISPE) group itself filed a formal competition complaint against Microsoft in November, saying the vendor uses: "unjustified and discriminatory bundling, tying, self-preferencing pricing and technical and economic lock-in" to "restrict choice".
It claimed the actions of Microsoft were in violation of Article 102 TFEU, and provide grounds for the EC to launch a formal investigation.
Francisco Mingorance, Secretary General at CISPE, which counts OVH, Aruba and many others as members, told us today the decision by the trio to settle with Microsoft was "disappointing on many levels."
Read more of this story at SoylentNews.
15:00
Truly Flexible Circuits Are a Bit of a Stretch Hackaday

Flexible PCBs have become increasingly common in both commercial devices and DIY projects, but Panasonics new stretchable, clear substrate for electrical circuits called Beyolex takes things a step further. The material is superior to existing stretchable films like silicone, TPU, or PDMS due to its high heat tolerance (over 160 C) for the purposes of sintering printable circuit traces.
But, a flexible substrate isnt very useful for electronics without some conductive traces. Copper and silver inks make for good electrical circuits on stretchable films, and are even solderable, but increase resistance each time they are stretched. Recently, a team out of the University of Coimbra in Portugal has developed a liquid metal ink that can stretch without the resistance issues of existing inks, making it a promising pair with Panasonics substrate. Theres also certain environmental benefits of printing circuits in this manner over t...
14:52
NOW: Pensions and the Missing 18,000,000 Pounds schestowitz.com
Sounds familiar? Yes, Standard Life (2011-2016). Seems like a pattern
TPR confirms end to serious admin issues at Now Pensions
TPR forces Now Pensions to overhaul admin system after 18m failing
NOW:Pensions failed to collect 18m of contributions
Now Pensions fined for long-running issues
Summary: The above is important because of the timing. After 5+ years of pension fraud at Sirius Open Source the company enrolled staff without paperwork/signatures and barely with any consent (in late 2016); to make matters worse, a few years ago it upped staff contribution levels without increasing its own, in effect forcing staff to send even more money (ones own money, not the companys) into this dubious pot with uncertain future.
14:45
Sirius Open Source Moved to NOW: Pensions the Same Year (2016) It Failed to Collect Money Techrights
Sounds familiar? Yes, Standard Life (2011-2016). Seems like a pattern
TPR confirms end to serious admin issues at Now Pensions
TPR forces Now Pensions to overhaul admin system after 18m failing
NOW:Pensions failed to collect 18m of contributions
Now Pensions fined for long-running issues
Summary: The above is important because of the timing. After 5+ years of pension fraud at Sirius Open Source the company enrolled staff without paperwork/signatures and barely with any consent (in late 2016); to make matters worse, a few years...
14:45
Vulnerabilities impacting multiple QNAP operating systems (CVE-2022-27597, CVE-2022-27598) Help Net Security
Two vulnerabilities affecting various QNAP operating systems (CVE-2022-27597 and CVE-2022-27598) have been uncovered by Sternum. These vulnerabilities enable authenticated remote users to access secret values, requiring owners to take immediate action by updating their operating system(s). Finding CVE-2022-27597 and CVE-2022-27598 Before discovering the vulnerabilities, the researchers ran performance testing and benchmarking on a QNAP TS-230 NAS device. Unexpectedly, attention shifted to a string of security alerts coming from the system, informing the team about multiple More
The post Vulnerabilities impacting multiple QNAP operating systems (CVE-2022-27597, CVE-2022-27598) appeared first on Help Net Security.
14:30
How can organizations bridge the gap between DR and cybersecurity? Help Net Security
Breaking down the silos between disaster recovery (DR) and cybersecurity has become increasingly important to ensure maximum business resiliency against outages, data breaches, and ransomware attacks. Yet, many organizations still operate these functions separately, leading to slower response times, budgeting challenges, duplicated resource allocations, and an overall weaker security and business continuity posture. Why must DR and cybersecurity teams collaborate? Encouraging collaboration between your disaster recovery and cybersecurity teams can offer several benefits for your More
The post How can organizations bridge the gap between DR and cybersecurity? appeared first on Help Net Security.
14:30
Microsoft Tightens OneNote Security by Auto-Blocking 120 Risky File Extensions The Hacker News
Microsoft has announced plans to automatically block embedded files with "dangerous extensions" in OneNote following reports that the note-taking service is being increasingly abused for malware delivery. Up until now, users were shown a dialog warning them that opening such attachments could harm their computer and data, but it was possible to dismiss the prompt and open the files. That's going
14:25
Severe IT Failure: NOW: Pensions Allowed the Sensitive Personal Details of 30,000 Customers to Leak Out Online schestowitz.com
They tried blaming it on outsourcing (their own)
Summary: NOW: Pensions, which is apathetic towards crimes of Sirius Open Source (because it gets paid to play along), has one heck of a history when it comes to managing data; 2 years ago its customers data (some of it highly sensitive) was copied and posted online for all to download, at least temporarily, after a severe breach
14:20
Did NOW: Pensions Adopt Security Malpractices of Sirius Open Source? Server Breaches The Norm Now? Techrights
They tried blaming it on outsourcing (their own)
Summary: NOW: Pensions, which is apathetic towards crimes of Sirius Open Source (because it gets paid to play along), has one heck of a history when it comes to managing data; 2 years ago its customers data (some of it highly sensitive) was copied and posted online for all to download, at least temporarily, after a severe breach
14:00
Streamlining cybersecurity decision-making for analysts and CISOs Help Net Security
Using structured, machine-readable data in defensive systems can present a significant challenge. In this Help Net Security interview, Giorgos Georgopoulos, CEO at Elemendar, discusses these challenges and how Elemendars application can help cyber analysts and CISOs. Giorgos highlights the companys customizable technology, which can be tailored to meet the unique needs of different organizations, as well as the security measures that Elemendar takes to protect the data processed by their AI technology. What are some More
The post Streamlining cybersecurity decision-making for analysts and CISOs appeared first on Help Net Security.
13:55
NOW: Pensions Has Concerns About the Future (Peoples Plans May be Insolvent) schestowitz.com
In their own words (latest statement from Companies House):
Summary: The crimes of Sirius Open Source are under investigation, but NOW: Pensions does not seem to care. On the phone, the manager at this pension firm said hed send assurance letters. In his E-mail he said the same. Two of his workers had said the same for 2 months prior. They all lied. Lying is the norm there. Would you trust a pension provider such as this? If this is the norm in this sector (financial/pension industry), theres big trouble ahead.
13:54
Cryptocurrency Companies Targeted in Sophisticated 3CX Supply Chain Attack The Hacker News
The adversary behind the supply chain attack targeting 3CX deployed a second-stage implant specifically singling out a small number of cryptocurrency companies. Russian cybersecurity firm Kaspersky, which has been internally tracking the versatile backdoor under the name Gopuram since 2020, said it observed an increase in the number of infections in March 2023 coinciding with the 3CX breach.
13:52
Pension Provider of Sirius Open Source: Well Probably be Okay for the Next 12 Months Techrights
In their own words (latest statement from Companies House):
Summary: The crimes of Sirius Open Source are under investigation, but NOW: Pensions does not seem to care. On the phone, the manager at this pension firm said hed send assurance letters. In his E-mail he said the same. Two of his workers had said the same for 2 months prior. They all lied. Lying is the norm there. Would you trust a pension provider such as this? If this is the norm in this sector (financial/pension industry), theres big trouble ahead.
13:30
Shadow data slipping past security teams Help Net Security
The rapid pace of cloud transformation and democratization of data has created a new innovation attack surface, leading to 3 in 4 organizations experiencing a cloud data breach in 2022, according to Laminar. 68% of data security professionals have identified shadow data as their top concern when it comes to protecting cloud data. The report reveals that concern over shadow data has increased to a 93% compared to 82% the year before. This finding indicates More
The post Shadow data slipping past security teams appeared first on Help Net Security.
13:17
NASA's Massive Rocket Transporter is Officially a Record-Breaking Big Boy SoylentNews
NASA's Crawler Transporter 2 was originally designed to carry Saturn V rockets during the Apollo program nearly 60 years ago. The aging giant recently got a much-needed upgrade for supporting the Artemis SLS megarocket, beating its twin vehicle for a world record.
On Wednesday, Guinness World Records presented NASA teams at the Kennedy Space Center with a certificate confirming that, at a whopping 6.65 million pounds (3 million kilograms), Crawler Transporter 2 is the world's heaviest self-powered vehicle, NASA announced in a statement.
"Anyone with an interest in machinery can appreciate the engineering marvel that is the crawler transporter," Shawn Quinn, program manager of Exploration Ground Systems, said in the statement. [...]
"NASA's crawlers were incredible pieces of machinery when they were designed and built in the 1960s," John Giles, NASA's Crawler Element Operations manager, said in the statement. "And to think of the work they've accomplished for Apollo and shuttle and now Artemis throughout the last six decades makes them even more incredible."
Due to how heavy the Crawler Transport is, the vehicle essentially crawls its way to the launch pad. It takes about eight to 12 hours for the rocket-carrying vehicle to drive the 4.2 miles (6.7 kilometers) from the Vehicle Assembly Building to the launch pad, going at a slow and steady speed of one mile per hour (1.6 kilometers per hour). It could take you a shorter time to walk that distance by foot.
Here's a crawler-transporter fact sheet [pdf]
Read more of this story at SoylentNews.
13:00
Lack of security employees makes SMBs sitting ducks for cyber attacks Help Net Security
For SMBs (and startups in particular), breaches can be devastating, according to DigitalOcean. To strengthen their cybersecurity posture, companies must spend valuable resources on maintaining or updating systems, hiring and training staff, and implementing security software resources and options that many dont have readily available. SMBs security posture Cybersecurity threats are more real and prevalent than ever before. For businesses, security breaches risk not only exposure to customer data and a decrease in trust, More
The post Lack of security employees makes SMBs sitting ducks for cyber attacks appeared first on Help Net Security.
12:57
Microsoft (Mis)Uses NDAs to Hide the Full Breadth of Its Massive Layoffs, Which Are Ongoing Every Week Techrights
How very typical of Microsoft (conditionally bribe the victims to keep them quiet, the hush money the media barely cares about)
Today (also a niche African site):
Summary: Microsoft layoffs this month are still ongoing, marking the fourth consecutive month of Microsoft layoffs (which the media barely mentions; too occupied with overhyped chaffbots). Considering the manager/non-manager ratio, NDAs notwithstanding, it seems like loads of people have just been fired and not a single Western news site covered this in English.
12:00
Machine Learning Helps Electron Microscopy Hackaday

Machine learning is supposed to help us do everything these days, so why not electron microscopy? A team from Ireland has done just that and published their results using machine learning to enhance STEM scanning transmission electron microscopy. The result is important because it targets a very particular use case low dose STEM.
The problem is that to get high resolutions, you typically need to use high electron doses. However, bombarding a delicate, often biological, subject with high-energy electrons may change what you are looking at and damage the sample. But using reduced electron dosages results in a poor image due to Poisson noise. The new technique learns how to compensate for the noise and produce a better-quality image even at low dosages.
The processing doesnt require human intervention and is fast enough to work in real time. It is hard for us to interpret the tiny features in the scans presented in the paper, but you can see that the standard Gaussian filter doesnt work as well. The original dots appear fat after filtering. The new technique highlights the tiny dots and reduces the noise between them. This is one of those things that a human can do so easily, but traditional computer techniques dont always provide great results.
You have to wonder what other signal processing could improve with machine learning. Of course, you want to be sure you aren&...
12:00
Guardz releases cybersecurity platform for MSPs and IT professionals Help Net Security
Guardz has launched its dedicated cybersecurity platform for MSPs and IT professionals that empowers MSPs to protect their clients with automated remediation plans, to improve their reporting for existing clients and better obtain new ones, and to cut operational and licensing costs up to 75%, ultimately boosting revenue. Cybersecurity attacks aimed at small and mid-size businesses are on the rise, yet only 14% of these companies are prepared to defend themselves. Many either cannot afford More
The post Guardz releases cybersecurity platform for MSPs and IT professionals appeared first on Help Net Security.
11:37
Environmental Sustainability at EPO Must Become More Than a Buzzword Techrights
And sure, granting loads of monopolies on alternative energy only exacerbates the climate crisis
Summary: Battistellis Nemesis, Ion Brumme, wrote a letter to Battistellis sidekick last week; the EPO is being challenged to pursue real sustainability rather than name-drop that as a buzzword
WHEN Antnio Campinos was parachuted into the EPO by his mate Benot Battistelli, serving in a role he was not qualified to fill, Campinos reportedly spared not much time. He told Ion Brumme he would be better off leaving; remember that Battistelli attacked Brumme and the EPO was forced to reinstate Brumme only years later when ILOAT finally delivered a much-needed ruling.
Months ago Brumme wrote about the situation and it doesnt look too good. Now, after another election in Munich, the Local Staff Committee Munich (LSCMN) kicks into action. Brumme writes as Vice-Chair of LSCMN. In this letter, LSCMN explains, we propose that the Office considers financially supporting the purchase of these tickets by staff up to a 100% refund.
Since Campinos fancies talking about "sustainability" all the time (distracting from the EPOs abuses) maybe he should listen. Heres the full letter from Brumme, dated about a week ago:
European Patent Office
80298 Munich
GermanyLocal Staff Committee Munich
Comit local du personnel de Munich
rtlicher Personalausschuss MnchenEmail: mnstcom@epo.org
Date: 29.03.2023
sc23010mlEuropean Patent Office | LSC Munich | GERMANY
President of the EPO
Mr Antnio Campinos
via email PRESIDENT@epo.orgOPEN LETTER
Subject: Deutschlandticket Environmental sustainabilityDear Mr....
11:14
Links 03/04/2023: Compudopt and Red Hat at 30 Techrights
![]()
Contents
-
GNU/Linux
-
Notebook Check PineTab2 and PineTab-V Linux tablets will launch April 11
While the Android tablet market seems to be cooling, the Linux tablet world is starting to gain some traction, thanks in large part to Pine64 and their PineTab. The companys latest Linux tablet, the PineTab2, is set to launch on April 11 at a budget-tier price.
The PineTab2, which was revealed back in December, is a low-powered tablet that supports t...
-
10:29
Google Assistant Might be Doomed: Division Reorganizes to Focus on Bard SoylentNews
Is the Google Assistant doomed? The evidence is starting to pile up that the division is going down the tubes. The latest is news from CNBC's Jennifer Elias that says the Google Assistant division has been "reshuffled" to "heavily prioritize" Bard over the Google Assistant. It all sounds like the team is being reassigned.
We'll get into the report details in a minute, but first a quick recap of the past two years of what the assistant has gone through under Google:
- Google Assistant saw eight major speaker/smart display hardware releases in five years from 2016-2021, but the hardware releases seem to have stopped. The last hardware release was in March 2021. That was two full years ago.
- 2022 saw Google remove Assistant support from two in-house product lines: Nest Wi-Fi and Fitbit wearables.
- 2022 also saw a report from The Information that said Google wanted to "invest less in developing its Google Assistant voice-assisted search for cars and for devices not made by Google."
- Google Assistant's driving mode was shut down in 2022.
- Google Assistant's "Duplex on the web" feature was also shut down in 2022.
- One of Google Assistant's core unique features, Reminders, is being shut down in favor of Google Task Reminders soon.
- Google Assistant has never made money. The hardware is sold at cost, it doesn't have ads, and nobody pays a monthly fee to use the Assistant. There's also the significant server cost to process all those voice commands, though some newer devices have moved to on-device processing in a stealthy cost-cutting move. The Assistant's biggest competitor, Amazon Alexa, is in the same boat and loses $10 billion a year.
Each one of those developments could maybe be dismissed indivi...
10:00
HPR3827: Reply to hpr 3798 Hacker Public Radio
From Wikipedia, the free encyclopedia LILO (Linux Loader) is a boot loader for Linux and was the default boot loader for most Linux distributions in the years after the popularity of loadlin. Today, many distributions use GRUB as the default boot loader, but LILO and its variant ELILO are still in wide use. Further development of LILO was discontinued in December 2015 along with a request by Joachim Wiedorn for potential developers. For EFI-based PC hardware the now orphaned ELILO boot loader was developed,originally by Hewlett-Packard for IA-64 systems, but later also for standard i386 and amd64 hardware with EFI support. hardware, ELILO is one of the available bootloaders. It supports network booting using TFTP/DHCP. https%3A%2F%2Fen.wikipedia.org%2Fwiki%2FLILO_%28bootloader%29%23elilo hpr3798 slackware.com https://sourceforge.net/projects/elilo/files/elilo/ elilo.config: prompt delay=20 timeout=20 default=g #default=h chooser=simple message=textmenu-message.msg image=vmlinuz-generic label=g initrd=initrd.gz read-only append="root=/dev/nvme0n1p5 resume=/dev/nvme0n1p6" image=vmlinuz-huge label=h read-only append="root=/dev/nvme0n1p5 resume=/dev/nvme0n1p6" image=dummy label=w slackware; reading is not an option Ken: added aditional links and wikipedia summary
08:41
Fedora Workstation Aiming To Improve Encryption, Possibly Encrypted Disk By Default In The Future Phoronix
Fedora Workstation developers and those involved at Red Hat have been working to improve the state of disk encryption on Fedora with a end-goal of possibly making the installer encrypt systems by default...
08:16
Debian 12's Installer Reaches RC1 Status Phoronix
The Debian Installer for the upcoming Debian 12 "Bookworm" release has reached its release candidate phase...
08:15
Jeff Otto joins Riskified as CMO Help Net Security
Riskified has announced that Jeff Otto has joined the company as Chief Marketing Officer, effective immediately. Otto will be responsible for a global integrated marketing strategy that will amplify Riskifieds brand, strengthen its category leadership and accelerate demand for Riskifieds expanding product suite. Its an exciting moment to have Jeff lead the charge on marketing with Riskified reaching the crossroads of both growth and profitability, said Eido Gal, CEO, Riskified. Jeff has the ideal blend More
The post Jeff Otto joins Riskified as CMO appeared first on Help Net Security.
07:39
The 'Insanely Broad' RESTRICT Act Could Ban VPNs in the USA SoylentNews
https://www.vice.com/en/article/4a3ddb/restrict-act-insanely-broad-ban-tiktok-vpns
[...] The bill could have implications not just for social networks, but potentially security tools such as virtual private networks (VPNs) that consumers use to encrypt and route their traffic, one said. Although the intention of the bill is to target apps or services that pose a threat to national security, these critics worry it may have much wider implications for the First Amendment.
"The RESTRICT Act is a concerning distraction with insanely broad language that raises serious human and civil rights concerns," Willmary Escoto, U.S. policy analyst for digital rights organization Access Now told Motherboard in an emailed statement. [...]
[...] Under the RESTRICT Act, the Department of Commerce would identify information and communications technology products that a foreign adversary has any interest in, or poses an unacceptable risk to national security, the announcement reads. The bill only applies to technology linked to a "foreign adversary." Those countries include China (as well as Hong Kong); Cuba; Iran; North Korea; Russia, and Venezuela.
The bill's language includes vague terms such as "desktop applications," "mobile applications," "gaming applications," "payment applications," and "web-based applications." It also targets applicable software that has more than 1 million users in the U.S.
"The RESTRICT Act could lead to apps and other ICT services with connections to certain foreign countries being banned in the United States. Any bill that would allow the US government to ban an online service that facilitates Americans' speech raises serious First Amendment concerns," Caitlin Vogus, deputy director of the Center for Democracy & Technology's Free Expression Project, told Motherboard in an emailed statement. "In addition, while bills like the RESTRICT Act may be motivated by legitimate privacy concerns, banning ICT services with connections to foreign countries would not necessarily help protect Americans' privacy. Those countries may still obtain data through other means, like by purchasing it from private data brokers." [...]
Read more of this story at SoylentNews.
07:13
UK outsourcing services provider Capita suffered a cyber incident Security Affairs
UK outsourcing services provider Capita confirmed that the outage suffered on Friday was caused by a cyberattack.
Capita, the UK outsourcing giant, confirmed that its staff was locked out of their accounts on Friday after a cyber incident.
Capita is one of the governments biggest suppliers, with 6.5bn of public sector contracts, reported The Guardian. The outsourcing firm signed numerous contracts with the Ministry of Defence.
In an update shared on April 3 about the incident, the company announced it has experienced a cyber incident primarily impacting access to internal Microsoft Office 365 applications.
The attack disrupted some services provided to individual clients, but the company pointed out that the majority of its client services were not impacted.
Our IT security monitoring capabilities swiftly alerted us to the incident, and we quickly invoked our established and practised technical crisis management protocols. Immediate steps were taken to successfully isolate and contain the issue. The issue was limited to parts of the Capita network and there is no evidence of customer, supplier or colleague data having been compromised. reads the update.
Working in collaboration with our specialist technical partners, we have restored Capita colleague access to Microsoft Office 365 and we are making good progress restoring remaining client services in a secure and controlled manner.
Capita has immediately taken action to isolate and contain the issue.
The company did not disclose details about the incident, however, its...
07:12
Melbet Betting Firm
Click on the Melbet login button in the upper right nook or beneath on the house web page. The task of putting a wager at Melbet India is made lots of simplified if you follow a set of procedures. They would begin with logging into the account with the small print. Receive the bonus Receive the bonus in the type of free bets. Sign up at Melbet India from the link under Sign up with a Melbet India promo code.
It ensures that every one your private knowledge and funds are fully protected from anything dangerous on-line. Login to the melbet account via the necessary credentials. Login to the melbet account and click on on the Payments option on the bottom of the web page. The consumer should make a minimal required amount to avail of any bonuses on the site. Login to your melbet account with the mandatory credentials. Here well provide you solely interesting content material, which you will like very much.
You shouldnt get greater than 21, but as a substitute, should get greater than the vendor. Blackjack games on the Melbet BD app are Double Exposure Blackjack, Rainbow Blackjack, and many extra. This type of wager is just a combination of multiple Accumulator bets. With Express bets, you presumably can lose one guess, however nonetheless, earn cash from other bets. Download the program from our official web site, set up it after which run the Melbet app. In the folder of downloaded recordsdata, find the installation file and install it in your smartphone.
To get the bonus you have to deposit no much less than INR one thousand on Friday. The obligatory situation for getting the bonus is the volume of bets in sections of fast games and slots not less than INR and the account must be at least 30 days old. Unlike the model of the mobile site, which supports stay chats, the cell application, unfortunately, doesnt have an online chat feature. The ticket booking process could be very simple and PCA tickets can be booked online. Users have to go to the official/partner web site where they can book cricket match tickets. They can select their favorite stand from the various obtainable stands.
Instead, a devoted cell web page does its duty to ship a lot of the merchandise and features. There is a small sacrifice in the total gaming expertise, but customers can proceed to entry Mel Bet with none location restriction. The Melbet app is out there for Android and Apple platforms.
Tons of Melbet cricket evaluation in India states that the positioning is welcoming to Indian punters with lots of unique offers for them. Melbet India accepts funds made in India Rupee and permits its gamers to wager using Indian Rupees. Melbet is legal in India and welcomes gamers from India to open a Melbet India account. If youre a genuinely Indian bettor, Melbet India is an effective place to begin.
At the identical time, the bookmaker doesnt cost gamers any inner commissions. Talking in re...
07:10
Mohali Stadium Tickets Price, Ipl Tickets Mohali 2023, Pca Tickets h+ Media
Mohali Stadium Tickets Price, Ipl Tickets Mohali 2023, Pca Tickets
We extremely suggest you add the Melbet cellular model to bookmarks in your browser. By doing that you just wont lose entry to your winnings and private information at any time. All of that can be reached by using simply your browser, as a substitute of placing in the Melbet utility and filling the gadget storage! All your information is protected with an SSL-encryption key even with any browser, together with Safari, Mozilla, Google Chrome, and Opera).
All sports have tons of markets and aggressive odds. Nice to see that there are such an excellent utility for betting and playing in Bangladesh. You can wager on worldwide cricket matches with a nice design. With the Melbet application, you can make single bets, group bets, and express ones. In case of a win, the prize money might be credited to your account instantly. We give you our high-tech, trendy, and dependable Melbet on-line app along with a fantastic variety of sports disciplines and occasions to guess on!
Click on the deposit button that you will discover on the top of
the display screen. Visit the website and login to your account
suing your username and password. Choose any of the above
strategies based on your convenience. Odd/even runs Here, the
punters bet whether or not a teams ultimate rating will be odd and
even number of runs. On the cricket page, you can see all the
continuing and the upcoming events.  Once the
wagering requirement is met by you, the welcome bonus shall be
credited in your account inside next 24 hours.
Once the
wagering requirement is met by you, the welcome bonus shall be
credited in your account inside next 24 hours.
Youll see an inventory of all of the available fee options for your region. Navigate to your account section and then the deposit space, or simply click on the Make a Deposit button in the higher proper corner of the display. Logging into your account is, in fact, a lot less complicated than registering.
Yes, Melbet accepts Indian gamers and Indian foreign money as well. One can wager on all the out there on line casino video games, sports/e-sports, and so on. Melbet India accepts nearly all of the handy Indian payment strategies, together with Paytm, UPI, G-Pay, and so forth. Cricket is a tremendous sport that every Indian has grown up with. Melbet India offers exciting cricket betting alternatives to the basic public, so you dont have to depend on luck on your bets like other sports activities provide.
Furthermore, remember to manage your funds correctly and dont spend every thing on a single wager. Given numerous bookmakers available on the market, it is not straightforward to choose on an certainly secure and trustworthy cellular app. All clients of the gaming software platform want to fulfill some necessities to get Melbet App. Basically,...
07:10
The Method To Use Melbet App h+ Media
The Method To Use Melbet App
Youll discover that the sites forex will then change to Indian rupees on all pages. Thankfully, the procedure is relatively simple, particularly on Android telephones. You have detailed directions on the positioning, so that you wont have to guess what you should do. Just observe them, complete the installation, and start having fun. The Fast Games part includes 124 unique, fast-paced games that are incredibly enjoyable and rewarding. They require zero data and zero effort they are simply there to entertain you and reward you if youre fortunate.
The all-rounder brought an end to the blistering knock from Mayers and celebrated the wicket with an enormous roar. On Saturday, Lucknow Super Giants are batting first in opposition to Delhi Capitals and the spectators witnessed an explosive knock from Kyle Mayers within the first innings. DC required something special to wrap up the West Indian batter and Axar Patel was the man to rise to the state of affairs. His breakthrough was result of a particular supply and the all-rounder made it additional special with an extravagant celebration. Even the ordinary dismissals are made special by bowlers with extravagant celebrations after the wicket. Getting acquainted with the historical past of transactions and bets.
Stadium map depicts all the stand, pitch, pavilions, entry gates and different useful information of the bottom. During the CM Yogi Adityanath swearing ceremony, guests attended the ceremony. Map of Ekana stadium will surely assist the guests to search out the designated seat. Log on to the official website selling IPL Lucknow tickets. Lucknow Ekana International Cricket StadiumLucknow worldwide cricket stadium is constructed by Ekana Sportz City Pvt.
An important part of sports activities betting is the depth of the guess record. You can wager on greater than 1500 different outcomes on main sporting events. At the identical time, the games of native leagues are additionally not disadvantaged of the eye of the bookmaker.
Fast video games day Every Wednesday, casino players could make a deposit and get a 100 percent matched bonus as a lot as 100 (8,900) and five free spins. Naturally, you have to use the bonus on chosen quick video games Melbet offers. MelBet does every little thing possible on your consolation, so the site routinely adjusts to your system parameters, making it straightforward to navigate between the sections you want. You will also be ready to register, fund your account and bet on sports activities or casinos, and you may always ask your inquiries to the support team. Using the Melbet app makes your playing so much simpler.
Next step is to choose your preferred fee technique. You might be provided with four easy registration strategies. Over/underscore Here, the punters will predict whether the ultimate total rating of a staff in...
07:07
Melbet On Line Casino Evaluation 2023 Melbet Casino India h+ Media
Melbet On Line Casino Evaluation 2023 Melbet Casino India
bookmarks in your browser. By doing that you simply wont lose entry to your winnings and personal knowledge at any time. All of that could be reached by utilizing just your browser, as a substitute of putting in the Melbet software and filling the system storage! All your data is protected with an SSL-encryption key even in a cellular model of a website. Note that Melbet is compatible with any browser, together with Safari, Mozilla, Google Chrome, and Opera).There are also varied reload bonuses, and free bet provides available once in a while. Melbet frequently runs attractive promotions that can considerably increase your winnings. For example, they usually offer enhanced odds-on sure markets, permitting you to position bets with inflated odds and potentially make massive profits. They additionally run regular reload bonuses, providing you with a percentage bonus on top of your deposited quantity when replenishing your account stability. Volleyball is one other fashionable sport amongst Melbet prospects.
This provide nonetheless, solely applies to pre-match single and accumulator bets and not reside bets. To avail this bonus provide, punters should have made the bets with real money and people bets must be having minimum odds of 1.three. The bonus quantity might be instantly credited to your account once you place your one hundredth bet. For a cushty game from a smartphone, a cellular
Just for this chance, you need to use the smartphone program and have it all the time at hand. Downloading Melbet for Android is free, service is out there to all Internet users. However, in the intervening time its inconceivable to find the program in the Play Market.
The website of Melbet is well navigable, which cuts down plenty of problem for the gamers. It also options an amazing loyalty program, which is designed to offer a personalised experience to its loyal gamers. This online on line casino is accepting gamers from all the world over including India. Moreover, the operators have made special efforts in catering to the requirements of Indian gamers by adding Indian gambling video games in its broad selection of games. Its now time to evaluate one of the veterans in the on-line on line casino recreation, Melbet. Launched in 2012, they are in a number of different markets from all over the world and now theyve entered India and are making a huge impact.
PCA stadium ticket counter timings shall be announced in advance through the official channels. From the ticket rate desk, visitors can check Mohali Stadium IPL tickets price 2023. Cricket followers of Lucknow and UP are very excited that the T20 matches of the Lucknow Giants IPL matches shall be hosted in this stadium.
The primary complaints theyve relating to particular features or wageri...
07:07
Melbet Sportsbook Bonus For Indian Players Out There Here h+ Media
Melbet Sportsbook Bonus For Indian Players Out There Here
The potential winnings from a single wager depend on the percentages of the selected market. Melbet provides promo codes with which you might make free bets, get deposit bonuses, free spins, and more. In addition to the welcome bonus, Melbet offers its clients a reload bonus. You can get it by replenishing your account stability youll obtain a 50% bonus on the deposit, as much as 10,000 INR. After registering and confirming your account, its time to log in.
The crucial step in sports activities betting is checking the odds for varied sports activities occasions which are covered by the best sports betting app. The size of winnings instantly depends on them, so select the bookie with essentially the most competitive odds, as the higher odds, the more cash you might win. The next step is to obtain the chosen greatest app for sports betting.
There is also a large part dedicated to casino video games. An fascinating feature of this platform is you could save up to 10 sports events as favorites. This way, you could get fast access to them and not have to seek for them every time.
Done, you may have efficiently logged in to Melbet and you can enjoy all of the enjoyable offered by the platform. For cryptocurrency accounts, every kind of bonuses are disabled. With the Melbet on line casino app, you can dip into the on line casino atmosphere wherever you are.
Good bookmaker, no attempts to cheat with cash had been observed. The cash is withdrawn without issues, but to the identical account from which the replenishment was made, and nothing else. The bets are different, but there usually are not enough even odds for occasions / durations, with them it would be extra handy and, I assume, extra worthwhile. I asked technical help they stated that they took note, and thats it. But the foundations are transparent, so should you play fair, there wont be any problems.
The bookmaker provides the favored Indian fee strategies to make sure smoother transactions and UPI funds are considered one of them. Melbet permits various deposit strategies for Indian customers which are extremely secured. There are few different superior strategies such as Google pay, Phonepe, Paytm that can seize more players to the positioning. So, the addition of these strategies could make an enormous distinction in attracting varied gamers. Sometimes it may possibly, and if it does, it could be best to play specifically through your cellphone. Sometimes Melbet cell casino has some specific promotions for mobile customers that arent obtainable on the internet portal.
Real-time bets require lots of attention, as the percentages on bets change throughout the game. The Melbet India website is a reliable, secure platform for betting on sports activities. Here, your cash and private information are utterly secure. Also available to you is an impressive world o...
07:05
Melbet India Evaluate Get 2150 In Free Bets h+ Media
Melbet India Evaluate Get 2150 In Free Bets
This is probably the most sought-after payment answer in India. Millions of bettors are using this digital fee system because of the excellent customer support and very low transaction fees. If you are the proprietor of the iOS system, check one of the best apps for betting in India below. The bonus might be credited to the clients account automatically after the first deposit is made, until the field I are not wanting for any bonuses is ticked. [newline]This methodology can be referred to as essentially the most dependable, also whenever you create an account in this method, sooner or later it will be a lot easier to pass the verification procedure. Here you will need to specify a legitimate email tackle, currency, nation and different personal information which might be requested by the bookmaker.
I even have been betting on this web site for over 2 years now, no withdrawal problems, I actually have withdrawn over 700,000 already. Melbet is a standard online bookmaker that has been round since 2012. The firm is owned and operated by Bonnal Limited. You can log in to your private account by entering an e-mail address and a password specified throughout registration. Thanks to the above points, the program for phones works even with a poor connection to the cellular Internet. To verify your melbet account, you simply want to provide information about you and your house of residence.
Real-time bets require plenty of consideration, as the odds on bets change throughout the sport. The Melbet India website is a reliable, safe platform for betting on sports activities. Here, your money and private knowledge are fully protected. Also available to you is a magnificent world of assorted betting and entertainment at any time of day and night time. While making their first deposit, users can get a 100% bonus, which may be as a lot as Rs. eight,000. It calculates routinely after you make your first deposit.
The app is primarily the identical for each iOS and Android and very useful. You can fill in your credentials later to unlock all the enhanced options the site offers, including the power to make a cost. The reside on line casino is as extensive because the common on line casino, no much less than when the variety of games is in query. If youre looking for quite a lot of sports activities and betting presents, you cant go mistaken with Melbet.
The web model of Melbet bookmaker does not have such speed of response, updating and offering information. Live mode users will extremely respect the features of the mobile app. Melbet may be new to the web betting scene, nevertheless it definitely is no novice. It presents its customers with a plethora of engaging options, sport collections and bonus provides which are sufficient for a punters lengthy dedication to this site. Melbet India provides all kinds of generous bonus and promotional provides to it...
07:04
Melbet App Obtain For Android Apk And Ios Free Of Charge h+ Media
Melbet App Obtain For Android Apk And Ios Free Of Charge
There is a robust emphasis on sports betting, and this prominence makes it troublesome for gamers to find different recreation choices. This on line casino offers a dynamic mix of reside on line casino games plus options for stay sports betting supplied by well-known on line casino software program companies. Our experts delve into the positive and negative features of MELbet in India to discover out whether or not it is the proper match for an Indian gambler. BetRaja is your go-to source for on-line betting in India. The advantages of this bookmaker are undoubtedly a handy line, a handy Melbet cellular utility. There have been no problems with crediting and withdrawing funds but.
Betting on Sports with Melbet wouldnt be full when the website didnt provide Live Betting options. In contrast to Pre Match bets, Live bets are made simply as the occasion runs. The odds right here are often decrease and theyre dynamic. Both the app of Melbet and its website helps Live Streaming.
You can download Melbet cellular app for Android and iOS and make bets out of your smartphone. The shopper has a user-friendly interface, pleasant design and supports all of the sports available on the site. Bet on cricket, kabaddi and different disciplines, get winnings and withdraw them by way of the cashier, make deposits and activate bonuses. All this shall be obtainable in Melbet app for smartphones. When gamers place one hundred bets in a span of 30 days, they get the chance to win a bonus equal to the amount of the common stake of these one hundred bets.
One of the most effective things about Melbet is that the positioning is great for newbies and superior gamers alike. Please note that the corporate does not cost any commissions for your transactions, nevertheless commissions could apply to your most well-liked fee method. When you sign up for Melbet, youll be requested to create a username and password. This will be your login info for the Melbet website. Once youve logged in, youll have the flexibility to view the percentages for all the obtainable bets.
If there isnt any cash in your account, you might make a deposit by way of the cashier. We cowl all well-liked eSports events and offer a wide variety of outcomes for betting. And bets are available on both particular person match outcomes and international results, such because the winner of the championship. Enter promo code STARTBONUS1 to get your welcome bonus and to have a possibility to participate in all the promotions supplied by our bookmaker workplace. Depending on the registration technique you select, you will want to fill in a number of fields along with your personal knowledge.
We recommend reserving Mohali tickets 2023 solely via official web sites. Always comply with pointers and security procedures to enjoy the reside match within the stadium. Check the website account and r...
06:59
New VPN Malvertising Attack Drops OpcJacker Crypto Stealer HackRead | Latest Cybersecurity and Hacking News Site
By Deeba Ahmed
Researchers warned that the campaign works through a network of fake websites that promote seemingly harmless crypto apps and other software.
This is a post from HackRead.com Read the original post: New VPN Malvertising Attack Drops OpcJacker Crypto Stealer
05:53
How We Think About Copyright and AI Art Deeplinks
Artists are understandably concerned about the possibility that automatic image generators like Stable Diffusion will undercut the market for their work. We live in a society that does not support people who are automated out of a job, and being a visual artist is an already precarious career.
In this context, its natural to look to copyright law, because copyright is supposed to help ensure that artists get paid for their work. Unfortunately, one copyright theory advanced in a class-action lawsuit by some artists against Stable Diffusion is extremely dangerous for human creators. Other theoriesboth in that lawsuit and another suit by Getty Imagespropose to alter and expand copyright restrictions in ways that would interfere with research, search engines, and the ability to make new technology interoperate with old.
This legal analysis is a companion piece to our post describing AI image-generating technology and how we see its potential risks and benefits. We suggest that you read that post first for context, then come back to this one for our view on how the copyright questions play out under U.S. law.
Copyright law is supposed to embody a balance between giving artists a sufficient incentive to create, by granting them control of some of the ways their art can be used, and giving the public the right to build on and/or use that art in new and interesting ways. Here, the question is whether those who own the copyright in the images used to train the AI generator model have a right to prohibit this kind of use.
To answer that question, lets start with a few basic principles.
First, copyright law doesnt prevent you from making factual observations about a work or copying the facts embodied in a work (this is called the idea/expression distinction). Rather, copyright forbids you from copying the works creative expression in a way that could substitute for the original, and from making derivative works when those works copy too much creative expression from the original.
Second, even if a person makes a copy or a derivative work, the use is not infringing if it is a fair use. Whether a use is fair depends on a number of factors, including the purpose of the use, the nature of the original work, how much is used, and potential harm to the market for the original work.
Copyright and Training Sets
Heres how fair use would apply to AI art generati...
05:53
AI Art Generators and the Online Image Market Deeplinks
Now that computer-generated imaging is accessible to anyone with a weird idea and an internet connection, the creation of AI art is raising questionsand lawsuits. The key questions seem to be 1) how does it actually work, 2) what work can it replace, and 3) how can the labor of artists be respected through this change?
The lawsuits over AI turn, in large part, on copyright. These copyright issues are so complex that weve devoted a whole, separate post to them. Here, we focus on thornier non-legal issues.
How Do AI Art Generators Work?
There are two different parts of the life of an AI art generator. First are the data that teaches it what a "dog" is or, more abstractly, what "anger" looks like. Second are the outputs that the machine gives in response to prompts. Early, when the generator has not had enough training, those outputs only loosely reflect the prompts. But eventually, the generator will have seen enough images to figure out how to properly respond to a prompt (this is just how people do it, too). AI-generated creative content can run the gamut from "prompt based on an image I saw in a fever dream" to "very poorly written blog post."
How Does an AI Art Generator Learn?
AI art generators depend on machine learning. In a machine learning process, a training algorithm takes in an enormous set of data and analyzes the relationships between its different aspects. An AI art generator is trained on images and on the text that describes those images.
Once it has analyzed the relationships between the words and features of the image data, the generator can use this set of associations to produce new images. This is how it is able to take text inputa promptlike dog and generate (that is, output) arrangements of pixels that it associates with the word, based on its training data.
The nature of these outputs depends on the systems training data, its training model, and the choices its human creators make.
For instance: a model trained by feeding it images labeled with text that appeared close to those images on public web-pages will not be as good at matching prompts as it would be if it had been trained with images that had been manually annotated with explicit, human-generated labels.
This process is not too different from how babies learn things. For example, a lot of kids basically think all animals are "doggies" until they have enough exposure and correction by adults to distinguish "doggie" from "horsie." Machine learning can make similar mistakes, finding connect...
05:48
04:56
Amazon's Smart Speakers Collecting Kids Data May Lead to Government Lawsuit SoylentNews
Amazon's smart speakers may've landed the tech giant in hot water:
A Federal Trade Commission complaint could lead the US government to sue Amazon over children's data the retail giant collected through its line of smart speakers, according to a Bloomberg report on Friday.
At issue is whether Amazon's series of Alexa-powered smart speakers were collecting data on children under the age of 13 without parental consent and retaining it even after users attempted to delete it, which children's advocacy organizations asked the FTC look into back in 2019, the report said.
Now the FTC is now recommending issuing a complaint that Amazon didn't confirm parental consent before collecting data and that most of the Alexa activities designed for kids didn't have a privacy policy, sources told Bloomberg. The Justice Department could take the next step and file a lawsuit against Amazon next month.
The Amazon suit comes amid an FTC crackdown on data collection over the last few years under Chair Lina Khan, including fining the company formerly known as Weight Watchers for improperly storing kids' info. The commission also ordered Fortnite creator Epic Games to pay $520 million in fines and refunds for tricking kids into making in-game purchases and violating their privacy.
[...] Should the lawsuit find Amazon at fault, it's unclear how much it could be forced to pay in penalties. While Amazon reportedly claimed to be in compliance with the Children's Online Privacy Protection Act (COPPA), if it's found to have violated those rules dictating how children's data should be protected, the company could pay $50,000 per child affected, according to Politico.
Read more of this story at SoylentNews.
04:54
Trump Leaves Florida for New York Ahead of Expected Surrender and Arraignment cryptogon.com
Update: Trump to be Charged Tuesday with 34 Felony Counts: Donald Trump will be placed under arrest on Tuesday and informed that he has been charged with 34 felony counts for falsification of business records, according to a source who has been briefed on the procedures for the arraignment of the former president. A New []
04:38
Distribution Release: ExTiX 23.4 DistroWatch.com: News
ExTiX is a deepin-based (previously Ubuntu-based) distribution. Deepin today (230403). This ExTiX Build is based on Deepin 23 Alpha 2 (latest version) released by Deepin Technology on....
04:26
Eliezer Yudkowsky: Dangers of AI and the End of Human Civilization, I Hope Theres Nobody Inside There cryptogon.com
I havent been posting much because Ive been reading, watching and listening to things like this all weekend. Via: Lex Fridman: Related: They Dont Know How It Works In the Battle Between Microsoft and Google, LLM Is the Weapon Too Deadly to Use
03:24
Cloudflare DNS Must Block Pirate Sites, Italian Court Confirms TorrentFreak
 Website blocking has become an increasingly common
anti-piracy tool. ISPs in dozens of countries have been ordered by
courts to block pirate sites.
Website blocking has become an increasingly common
anti-piracy tool. ISPs in dozens of countries have been ordered by
courts to block pirate sites.
More recently, these blocking requests have expanded to DNS providers as well. In Germany, for example, a court ordered DNS resolver Quad9 to prevent users from accessing the music piracy site Canna.to.
Court Ordered Cloudflare to Block Torrent Sites
As one of the larger DNS resolvers, Cloudflare is also under fire. In Italy, several music companies, including Sony Music, Warner Music, and Universal, took Cloudflare to court, demanding the blocking of three torrent sites on the companys freely available 1.1.1.1 resolver.
Last year, an Italian court sided with the music companies. Through an interim order, the court ordered the blocking of kickasstorrents.to, limetorrents.pro, and ilcorsaronero.pro, three domains that are already blocked by ISPs in Italy following an order from local regulator AGCOM.
Cloudflare was unhappy with the courts decision and immediately protested the injunction. The challenge failed last November when the court upheld its initial ruling, discarding Cloudflares objections.
Among other things, the court held that the blocking order doesnt require the DNS resolver to surveil user activity, as Cloudflare challenged. A general monitoring obligation for online intermediaries would violate EU law, but the court determined that wasnt relevant in this case.
Cloudflares obligation to intervene to prevent the resolution of names does not derive from a general duty of surveillance but arises with the reporting of the specific illegal activity carried out through the public DNS service, the court held.
Court Confirms DNS Blocking Requirement
The ruling was a setback for Cloudflare, but that wasnt its only challenge. The American company filed an additional application where it requested clarification on the technical implementation of the blocking order. According to Cloudflare, blocking measures severely interrupt its DNS service, also in relation to competitors....
03:00
Updated SUSE ALP Prototype Focuses On Confidential Computing Phoronix
SUSE announced today the release of "Piz Bernina", its latest quarterly update to the SUSE Adaptable Linux Platform that is working to establish the next-generation SUSE/openSUSE computing platform...
02:13
A Serial Tech Investment Scammer Takes Up Coding? Krebs on Security
John Clifton Davies, a 60-year-old con man from the United Kingdom who fled the country in 2015 before being sentenced to 12 years in prison for fraud, has enjoyed a successful life abroad swindling technology startups by pretending to be a billionaire investor. Davies newest invention appears to be CodesToYou, which purports to be a full cycle software development company based in the U.K.

The scam artist John Bernard a.k.a. Alan John Mykailov (left) in a recent Zoom call, and a mugshot of John Clifton Davies from nearly a decade earlier.
Several articles here have delved into the history of John Bernard, the pseudonym used by a fake billionaire technology investor who tricked dozens of startups into giving him tens of millions of dollars.
John Bernards real name is John Clifton Davies, a convicted fraudster from the United Kingdom who is currently a fugitive from justice. For several years until reinventing himself again quite recently, Bernard pretended to be a billionaire Swiss investor who made his fortunes in the dot-com boom 20 years ago.
The Private Office of John Bernard let it be known to investment brokers that he had tens of millions of dollars to invest in tech startups, and he attracted a stream of new victims by offering extraordinarily generous finders fees to brokers who helped him secure new clients. But those brokers would eventually get stiffed because Bernards company would never consummate a deal.

John Bernards former website, where he pretended to be a billionaire tech investor.
Bernard would promise to invest millions in tech startups, and then insist that companies...
02:10
Fearing Loss of Control, AI Critics Call for 6-Month Pause in AI Development SoylentNews
On Wednesday, the Future of Life Institute published an open letter on its website calling on AI labs to "immediately pause for at least 6 months the training of AI systems more powerful than GPT-4." Signed by Elon Musk and several prominent AI researchers, the letter quickly began to draw attention in the pressand some criticism on social media.
Earlier this month, OpenAI released GPT-4, an AI model that can perform compositional tasks and allegedly pass standardized tests at a human level, although those claims are still being evaluated by research. Regardless, GPT-4 and Bing Chat's advancement in capabilities over previous AI models spooked some experts who believe we are heading toward super-intelligent AI systems faster than previously expected.
See Also: FTC Should Stop OpenAI From Launching New GPT Models, Says AI Policy Group
Related:
OpenAI Is
Now Everything It Promised Not to Be: Corporate, Closed-Source, and
For-Profit (March 2023)
OpenAI's
New ChatGPT Bot: 10 "Dangerous" Things it's Capable of (Dec.
2022)
Elon Musk
Says There Needs to be Universal Basic Income (Aug. 2021)
Tesla
Unveils Chip to Train A.I. Models Inside its Data Centers (Aug.
2021)
Elon Musk
Reveals Plans to Unleash a Humanoid Tesla Bot (Aug. 2021)
...
01:57
Linux Foundation is Outsourcing Linux Development and Communications to Surveillance Giants Techrights
More centralised than distributed, as thats how big sponsors (buying Board seats for 7-figure sums) of the Linux Foundation truly want things to be. Its neither pragmatic nor desirable, but impractical workflows enable control from above, not by peer (like peer review).
Linus Torvalds on using webmail: I only have a web browser, which is how I read e-mail and a couple of terminal windows open, which is where I end up doing my Git pulls and any coding although the coding part is not that common any more. (Partial transcript)
Video download link | original/full
Summary: It seems like Mr. Torvalds, the founder of Linux, has been tragically compelled to use proprietary software for E-mail (the primary means/tool for collaboration around Linux); this concerning trend, however, would be consistent with a lot of what weve been seeing from Jim 'respect Microsoft' Zemlin and his associates at the Board of Directors (proprietary software boosters)
THE Linux Foundations insistence on the use of Microsofts proprietary GitHub has long been documented here. Its done in defiance of...
01:30
AMD P-State EPP Performance With EPYC On Linux 6.3 Phoronix
Among the many new features coming in Linux 6.3 -- including many AMD additions -- is the AMD P-State EPP "Energy Performance Preference" support being merged for modern Ryzen and EPYC systems. AMD P-State EPP can further help tune the performance and power efficiency of AMD Linux systems beyond the existing basic AMD P-State driver support and address some existing deficiencies. Here are some benchmarks of the AMD P-State and ACPI CPUFreq driver configurations benchmarked on an EPYC Milan-X server with the in-development Linux 6.3 kernel.
00:22
Western Digital took its services offline due to a security breach Security Affairs
Western Digital disclosed a security breach, according to the company an unauthorized party gained access to multiple systems.
Western Digital has shut down several of its services after discovering a security breach, the company disclosed that an unauthorized party gained access to multiple systems.
Western Digital is currently experiencing a service outage impacting the following products: My Cloud, My Cloud Home, My Cloud Home Duo, My Cloud OS5, SanDisk ibi, SanDisk Ixpand Wireless Charger. reads the status page of the company on April 2, 2023. We are working to restore service. We apologize for any inconvenience. Next update will be posted on Monday, April 3.
On March 26, 2023, Western Digital identified a network security incident involving Western Digitals systems. In connection with the ongoing incident, an unauthorized third party gained access to a number of the Companys systems. reads the press release issued by the company. Upon discovery of the incident, the Company implemented incident response efforts and initiated an investigation with the assistance of leading outside security and forensic experts. This investigation is in its early stages and Western Digital is coordinating with law enforcement authorities.
Western Digital launched an investigation into the security breach and announced that it is implementing proactive measures to secure its operations. The response to the incident includes taking systems offline.
The company is working to understand the nature and extent of that security breach, it is also working on restoring impacted services.
The response to the incident put in place by WD suggests that the company was the victim of a ransomware attack, but at this time it is not included in any of Tor leak sites of ransomware groups.
Please vote for Security Affairs (https://securityaffairs.com/) as
the best European Cybersecurity Blogger Awards 2022 VOTE FOR YOUR
WINNERS
Vote for me in the sections:
- The Teacher Most Educational Blog
- The Entertainer Most Entertaining Blog
- The Tech Whizz Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
...Monday, 03 April
23:51
bet365 ba88 Comntx On-line Food & Grocery h+ Media
bet365 ba88 Comntx On-line Food & Grocery
It is likely one of the greatest on-line betting corporations in terms of buyer base and revenue. The company products include a sportsbook, a racebook, an online on line casino, poker, and bingo. The 365 online casino brings the thrill of on line casino entertainment proper to the New Zealand players PC or cellular gaming screens.
There can be Playback bonus up for grabs each Tuesday, the place the participant can win 10% of as a lot as $100 of what the home has taken as a end result of your play. Like the new participant bonus, a wagering requirement is connected earlier than you can withdraw any resultant winnings. Bet365 supply two Playtech platforms, Euro and Asian, with a wide-ranging selection games.
Players utilizing the Bet365 cell are in a place to stream reside matches, bet reside matches, cash-out and carry out other actions similar to depositing and withdrawing. It wasnt till the January 2000 when Denise Coates struck gold by registering the domain name Bet365.com. As you presumably can see, we couldnt actually find any negatives to listing about Bet365 NZ. The platform is great. If you wish to use a trusted casino with a wonderful game selection, this is one of the top actual cash casinos obtainable. You can break up the hand into two palms and double your bet, youre free to enjoy their big sport platform whereas knowing fairness and security is always deal with and examined at random.
This can additionally be true for Bet365 that lists round half as many methods for withdrawing such as Visa, financial institution switch, PayPal and Skrill. A participant ought to mind the minimal quantity of $10 and this could be a very low restrict as compared to peer online casinos out there. Moreover, the max withdrawal restrict is restricted by capabilities and rules of a cost method, not the on line casino. For example, Visa debit card allows for a max $30,000 in any single transaction. So a participant who needs to cash out a larger sum, has to do that in no much less than two installments. Anyway, no time limits is a pleasant strategy exercised by the online casino.
There, on the very best, youll be able to select the type of guess Standard or Banker. To place an specific guess on Bet365 login my account, enter the wager quantity beneath the name of the events, reverse the inscription Doubles. Each web site on-line account shopper has one of the best to find out on the suitable verification methodology. Australia has a 100 percent regulated sports activities betting and racing trade.
To withdraw your cash, you have to go to My Account click on on the withdraw link, after which select your hottest methodology. For further suggestion on using Bet365 welcome bonus, youll have the facility to always contact the betting firm employees. You can then make a guess and cost options primarily based in your non-public...
23:49
Bet365 Nz Casino Evaluate $200 Nzd Bet365 On Line Casino Bonus 2023 h+ Media
Bet365 Nz Casino Evaluate $200 Nzd Bet365 On Line Casino Bonus 2023
In complete, there are over 325 pokie games to play in the main bet365 Casino NZ lobby. Clicking the Games tab at the high left masses a special lobby, with an extra assortment of over a thousand of the best pokie video games. This variety supplies NZ players with a pleasant number of titles to evaluate. They have video games from high suppliers who add the newest recreation features, including fixed jackpots, progressives, methods plus, power play, money gather, megaways, and extra. Many pokie slots right here can be played using a bet365 bonus code or other promotional offers offered by the on line casino, together with their first deposit offer and weekly free spins deal. Casino customers obtained accustomed to the reality that cashing out is effected via fewer strategies than are offered for deposit.
forty five million sports activities betters go to Bet365 Sports for a reason, and we see no concern with recommending you attempt them out. We recommend you employ these instruments if you need them, as its not definitely value the stress of tolerating a gambling downside in any sense. If youre starting to assume that your sporting betting is getting out of hand, Bet365 Sports has a range of tools to help you get things back underneath management. In phrases of enhanced odds or boosted odds, take a look at out part above on Bet365s promotions there are a ton of them.
When it comes to creating withdrawals, you can enjoy a similar range of payment options. Other measures embody a compulsory handle and identity verification which is according to its KYC pointers. To curb money laundering gamers are required to withdraw cash using the same cost they used for deposit. In circumstances the place the card might have been expired, youll have to withdraw cash to your checking account which is required to have an analogous name and address to your Bet365 profile. The deposit and withdrawal limits depend upon the cost methods used. However, the sportsbook is versatile and accepts deposits and withdrawals as low as USD 10.
Our evaluation found that it is a very trustworthy site who has licenses in Australia and Malta and therefore makes it safe to guess right here from New Zealand. The bookmaker facilitates a broad range of reliable fee strategies, and their customer support group are available 24/7 to assist you along with your sports activities bets. Bet365 is one of the most recognised sports betting corporations on the market but what many people dont realise is that it also has an internet casino suite. Our Bet365 evaluation takes a look at this side of the operator, exploring its options and discovering its strengths and weaknesses.
The report serves exactly studied and analyzed information of the major industry players along with their share within the Sports Betting market. The analytical instruments used for the research compri...